Risky Bulletin Newsletter
March 04, 2026
Risky Bulletin: Cyber Command conducted cyberattacks ahead of Iran strikes
Written by

News Editor
This newsletter is brought to you by Okta. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
The Pentagon says that US Cyber Command carried out cyber operations that disrupted Iranian defenses ahead of a joint US-Israeli military operation over the last weekend.
"The first movers were US CyberCom and US SpaceCom, layering non-kinetic effects, disrupting and degrading and blinding Iran's ability to see, communicate, and respond," Joint Chiefs of Staff Chairman Gen. Dan Caine said in a press conference on Monday.
"Coordinated space and cyber operations effectively disrupted communications and sensor networks across the area of responsibility, leaving the adversary without the ability to see, coordinate, or respond effectively," he added.
Similar attacks were also carried out by Israeli cyber units.
According to the Financial Times, one of the Israeli attacks disrupted mobile towers around the location of Iranian leader Ali Khamenei. The attack flooded the towers and made the phone appear busy, preventing possible warnings of the incoming attack reaching Khamenei's security detail.
The joint strikes killed Iran's leader Ali Khamenei and about 50 of his high-ranking officials.
A great factor in all the successful strikes was the ability to track and pinpoint where targets would be on the day of the operation.
Sources told FT that this was made possible because Israeli hackers had hacked nearly all of Tehran's traffic cameras years before.
Video feeds had been collected in Tel Aviv for years, where the data was analyzed and used to identify where high-value targets like to park their cars and what routes they drove.
This allowed the US and Israel to determine that Khamenei would be in his office during the attack and where other ministers and military and intelligence officials would be as well.
Hackers also breached a major Iranian prayer app and urged Iranians to rise against the regime and the army to switch sides, although it's unclear who carried out this operation.
This is the second major US military operation this year where US cyber units received praises and flowers from Pentagon leadership. The Department of War also credited Cyber Command with crucial operations to disable Venezuelan anti-missile defenses and power grid ahead of its capture of President Maduro in January.
As for Iran, US officials say they expect the current operation to continue for at least several more weeks.
Iran responded to the current attack by launching its own missiles and drones against Israel, US bases, and Middle East countries hosting them. No major Iranian cyber operations have been reported so far, but this might be because the country's internet went down shortly after the attack and has been out since.
All cybersecurity and geopolitical experts expect the Iranian regime to answer this new aggression with both military and cyber strikes. Iran has already launched drone and missile attacks against US ships and its military bases across the Middle East. Missiles have also struck Israel and the Middle East states that host US bases, with infamous photos showing the iconic Burj Al Arab hotel in Dubai in flames after an Iranian drone strike.
On the cyber side, nothing has happened yet, probably because Iran has cut off internet access in the country, and after US and Israeli missiles also damaged its infrastructure.
Several cybersecurity firms have already published threat intel briefs on what Iran's cyber response could be, ranging from DDoS attacks to critical infrastructure digital sabotage. Check out briefs from Check Point, Cyderes, Flashpoint, Nozomi Networks, Palo Alto Networks, and SentinelOne.
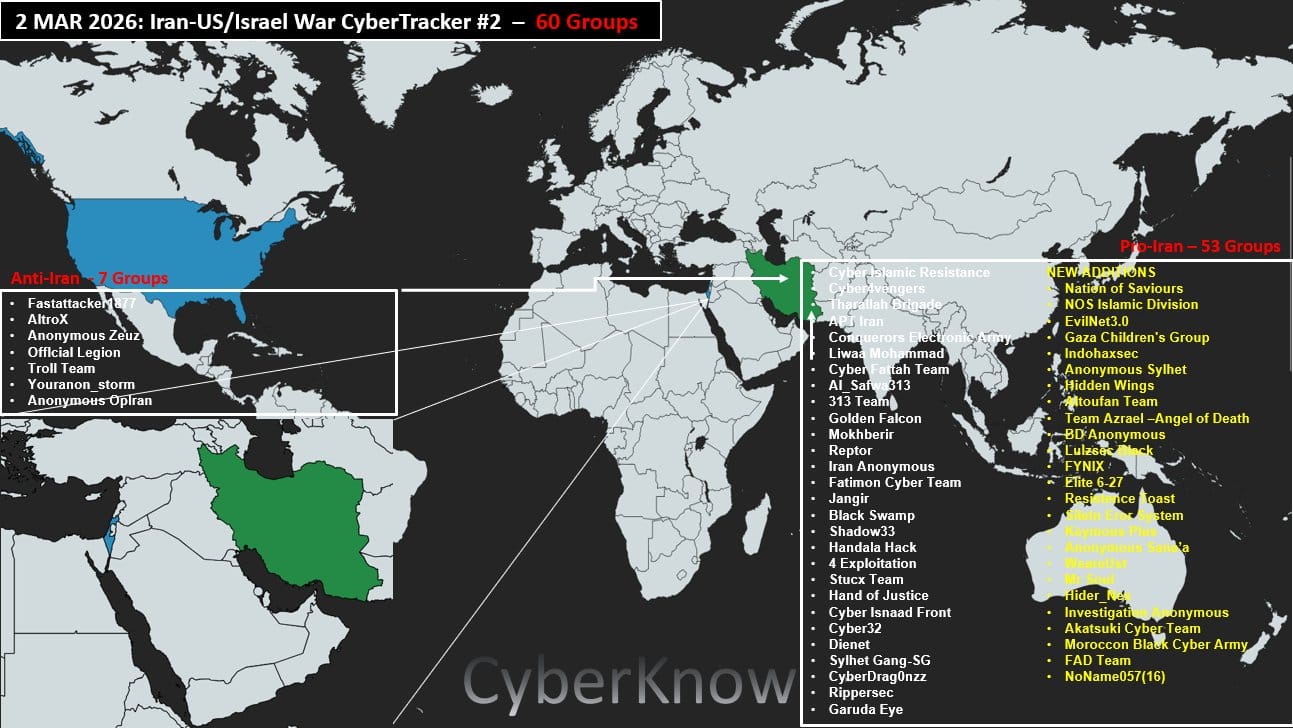
On the useless and more performative side of "the cyber," over 60 hacktivist groups have pledged their support for Iran or the US-Israel side. Most of them are pro-Kremlin groups who joined Iran's side, but no major DDoS attacks have been carried out so far.
Iran's cyber response isn't as feared as it once was either. First, because Iranian cyber-attacks that took place following the first wave of joint US-Israeli bombings last June didn't cause any lasting or significant damage. Second, according to a Bloomberg report, the number of active Iranian-linked hacking groups has dwindled from more than 130 last year, to just 17 this year.
So there's less groups doing less dumb hacks like disabling water pumps at some random African car wash. Unless they release something like WannaCry to have global impact, there's not really anything to fear outside Iran's kinetic response.
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
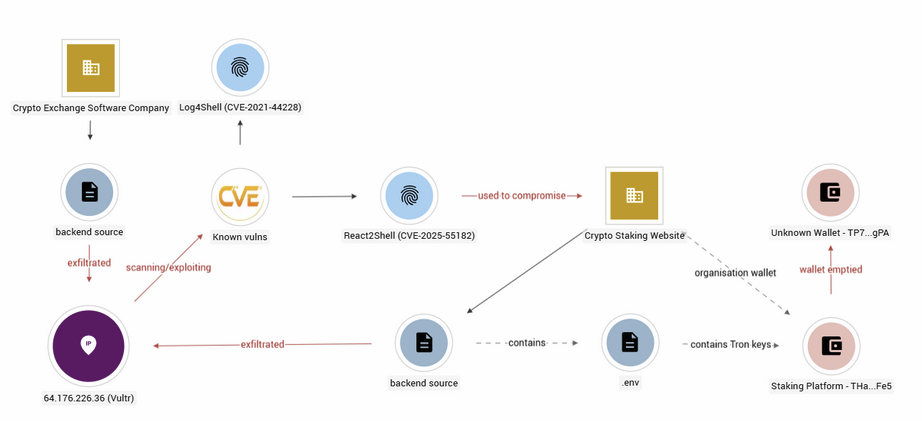
LexisNexis has another breach: LexisNexis has confirmed that hackers breached its platform and are now selling the data on hacking forums. The hack was traced back to the React2Shell vulnerability. This is the company's second breach over the past year. [BleepinComputer]
Odido crowdfunding campaign refunded: A Dutch security researcher has returned funds raised through a public crowdfunding campaign to pay a hacker ransom. Sijmen Ruwhof raised more than €2,000 from Odido customers to pay hackers not to release their data. Ruwhof returned the funds after the ShinyHunters group said it would release the Dutch ISP's data this week. [Tweakers]
CIG breach: Hackers have breached and stolen user data from CIG, a gaming studio behind the Star Citizen game.
DPRK group hacks crypto orgs: A suspected North Korean hacking group has breached software providers for the crypto sector and stole AWS tokens and hardcoded secrets for its customers. The attackers gained access to the software providers' web apps by exploiting the React2Shell vulnerability. The successful intrusions were discovered after the attackers left a web directory exposed online. [Ctrl-Alt-Intel]
General tech and privacy
PlayOn Sports fined for privacy violations: California's privacy watchdog has fined high-school sports ticketing platform PlayOn Sports $1.1 million for privacy violations. The platform allegedly forced users to agree to its terms of service in order to use purchased tickets. The company then used the data for targeted advertising. More than 1,400 US high-schools use the platform.
AWS data center hit by missiles in MENA regions: AWS says Iranian missiles hit two of its data centers in Bahrain and hit close to another data center in the UAE. The strikes caused outages and loss of connectivity. [DCD]
Massive scalping surge hits RAM market: Security firm DataDome has detected a massive surge in web scalping activity around DDR5 RAM marketplaces.
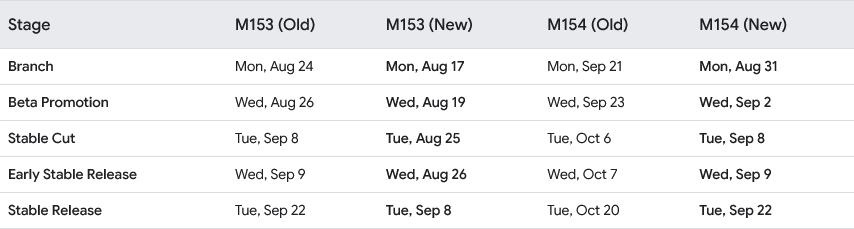
Chrome moves to two-week release cycle: The Google Chrome web browser will switch to a two-week release cycle starting in September this year. Chrome has been releasing a new browser version every four weeks since 2021. Security updates will continue to be released every week, if needed.
Government, politics, and policy
Procurement docs show China's use of AI for cyber: An analysis of procurement documents reveal that China is pushing for the integration of AI tools into its military, intelligence, and cyber operations. In the cyber realm, the PLA is using AI to detect intrusions, enhance cyber operations, and for disinformation campaigns. It is also experimenting with AI to ingest and analyze large quantities of data, pilot unmanned combat vehicles, and hit targets on its own. Beijing also wants to use AI to assist and accelerate decision-making because CCP officials are afraid the PLA's chain of command might be overmatched in a real battlefield. [Foreign Affairs]
Russia wants digital sovereignty by 2028: The Russian government anticipates it will be able to achieve digital sovereignty and separate the RuNet from the rest of the internet by 2028. Officials say they are in the process of replacing hardware and software running crucial systems. The entire process is expected to cost up to $13 billion. While Russia is excising western technology from its networks, it is replacing them with Chinese and Indian systems, creating a new dependence. [Gazeta.ru]
UK warns of possible Iranian cyberattacks: The UK's cybersecurity agency has warned local organizations to review their security postures in the aftermath of the conflict in Iran. The NCSC expects Iranian hackers and hacktivists to respond against all US allies after recent missile strikes that killed almost 50 officials, including leader Ali Khamenei.
6G coalition: The UK, US, Canada, Japan, Finland, Sweden, and Australia have launched at this year's Mobile World Congress a joint group to help develop new 6G technologies.
Dutch parties want a digital security package for citizens: Dutch political opposition parties have petitioned the government to create a digital security package for Dutch citizens. The government would have to create and run its own ad blocker, VPN, password manager, and antivirus system. The new package would be made public and free for any Dutch citizen.
CBP is tracking people with ad data: The US Customs and Border Protection is buying data from online advertisers to track people's movements. According to internal DHS documents, the data is taken from real-time bidding (RTB) ad platforms. This allows the agency access to near real-time location data without a warrant or having to go through mobile operators. [404 Media]
Sponsor section
In this Risky Business sponsor interview, Casey Ellis chats to Harish Peri, SVP and general manager for AI security at Okta, a cloud-based identity and access management company. The pair chat about the fact that AI is forcing enterprises to relearn the basics around identity security, and how Okta for AI Agents can help.
Arrests, cybercrime, and threat intel
IMSI gang trial in France: French authorities are seeking an eight-year prison sentence for a Chinese national who sold IMSI catchers in France. The devices were bought by fraudsters to impersonate mobile towers and send SMS spam. The messages were used to lure victims to online scams and phishing pages. The fraudsters are also on trial in France and prosecutors are seeking prison sentences of up to four and five years for each. [Le Monde]
Sextortionist pleads guilty: An Alabama man has pleaded guilty to hacking social media accounts of young women and then extorting owners for money or sexually explicit photos. Jamarcus Mosley hacked and extorted hundreds of victims, including underage teens. The hacks took place between 2022 and 2025 and targeted Snapchat, Instagram, and other social media accounts. Several victims gave into the extortion.
License trafficker gets 2 years: A Florida woman has been sentenced to 22 months in prison for trafficking in Microsoft software licenses. Heidi Richards and her company harvested software licenses from product labels and re-sold them at much lower prices online. The scheme lasted for five years and netted Richards millions of dollars.
India arrests 27 fraudsters: Indian authorities have arrested 27 suspects as part of a week-long crackdown on cyber fraud gangs. The main suspects conducted investment scams via WhatsApp, Instagram, and other mobile apps. Other suspects were arrested for laundering some of the stolen proceeds. The entire operation allegedly made more than $1.5 million. Just over a tenth was recovered during the raids. [Hindustan Times // The 420]
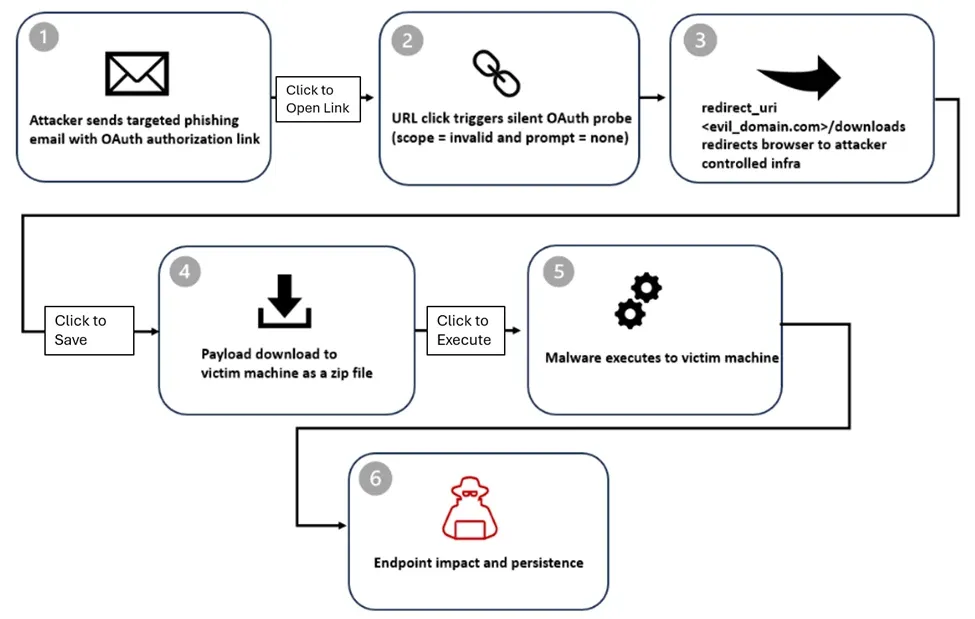
OAuth redirection abuse: Threat actors are abusing the redirection-to-URL feature of legitimate OAuth services to redirect the targets of phishing campaigns to malicious downloads. Attacks are ongoing and have targeted government and public-sector organizations. Microsoft has removed some of the OAuth apps involved in the attacks.
ClickFix campaign targets crypto investors: Moonlock researchers have spotted a social engineering campaign targeting cryptocurrency investors and Web3 professionals. The attackers pose as crypto investors and use video conference links to lure victims on ClickFix pages.
Malicious Chrome extension: The QuickLens Chrome extension turned malicious after it was sold by its original developer. The update strips security headers and redirects users to ClickFix pages.
D-Shortiez back button abuse: A malvertising group known as D-Shortiez is using a WebKit bug to abuse back button behavior and redirect users to scam sites.
IceWarp exposure: There are more than 1,200 IceWarp team collaboration servers exposed on the internet and vulnerable to a recent RCE vulnerability tracked as CVE-2025-14500.
Malware technical reports
Amos Stealer: Security researcher Gi7w0rm looks at a new variant of the macOS Amos Stealer that is currently being distributed in the wild via malvertising campaigns.
AuraStealer: Intrinsec looks at AuraStealer, a new infostealer gaining followers after last year's Lumma takedown by Europol. Researchers say they have now identified 48 C&C AuraStealer servers in the wild, showing its growing popularity.
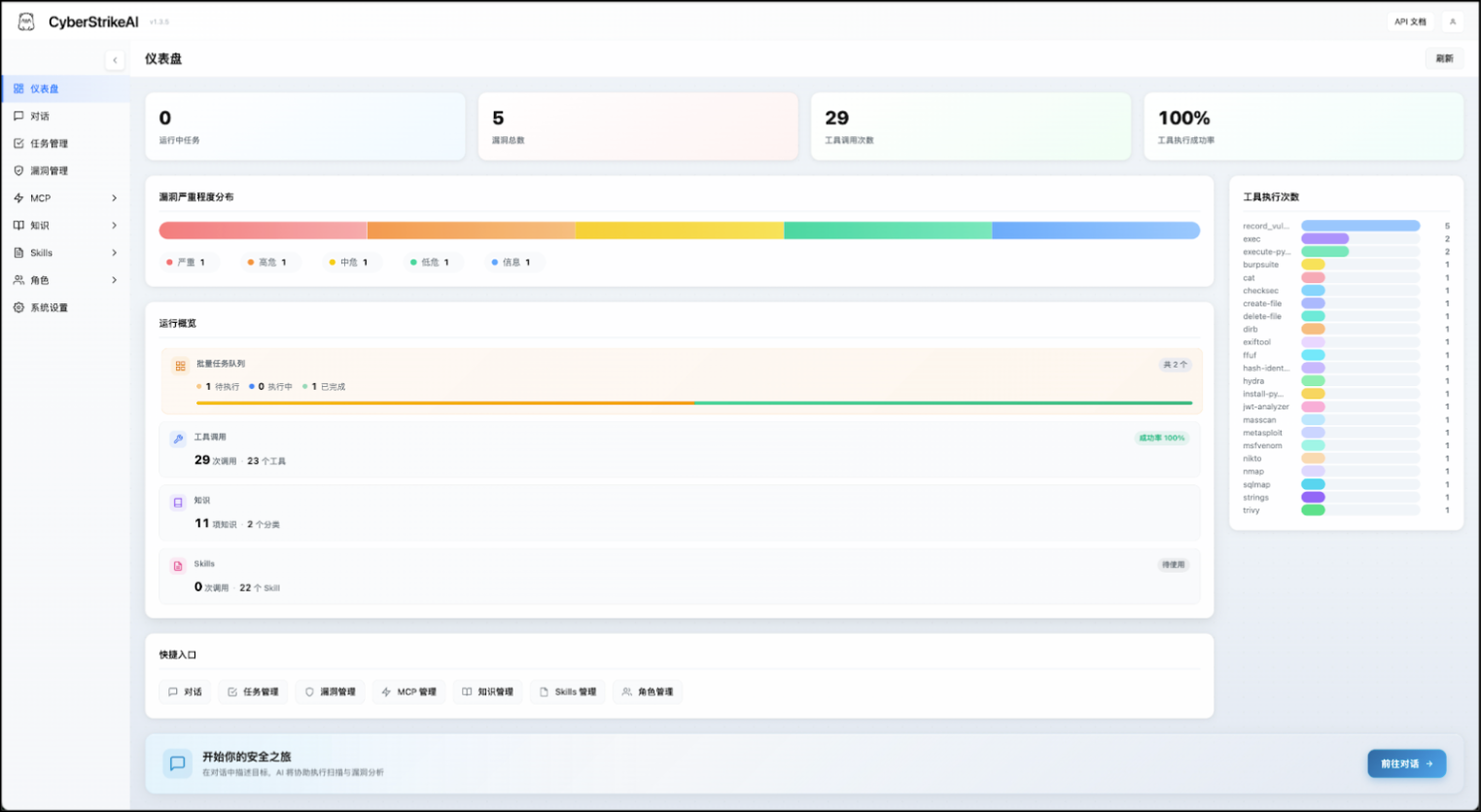
CyberStrikeAI: A Chinese developer going by Ed1s0nZ is behind a new AI-based offensive toolkit named CyberStrikeAI. It is one of the AI tools used by a Russian-speaking attacker to hack more than 600 Fortinet firewalls this year. According to TeamCymru, the tool's developer has ties to MSS-friendly Chinese private sector firms.
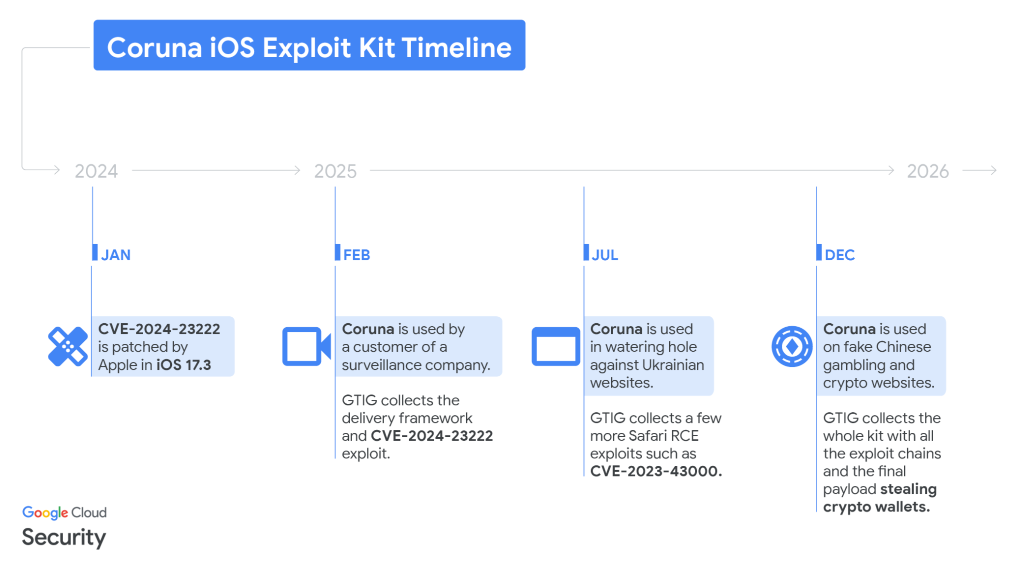
Coruna exploit kit: A Russian APT and a Chinese e-crime group have used a new exploit kit to target iOS users. The new Coruna toolkit was spotted on Ukrainian sites and Chinese gambling portals. According to Google, Corina was developed by an unnamed surveillance vendor and comes with 23 exploits spread across five exploit chains. The exploits are based on old zero-days that can hack devices up to iOS 17.2.1 , released in December 2023. Security firm iVerify told WIRED the kit might have been initially developed for the US government and is similar to the Triangulation exploits used against Russian officials in early 2023.
Sponsor section
In this sponsored product demo, Okta's Harish Chakravarthy and Brett Winterford walk through four new features Okta introduced in the wake of the emergence of modern attacker techniques targeting identity providers. These features will help you to prevent or limit the damage to your environment if an attacker manages to compromise a session token. If you're an Okta shop, you should absolutely watch this video.
APTs, cyber-espionage, and info-ops
SloppyLemming targets Bangladesh, Pakistan: A suspected Indian APT has conducted an "extensive" cyber-espionage campaign targeting government entities and critical infrastructure operators in Pakistan and Bangladesh. The SloppyLemming (Outrider Tiger, Fishing Elephant) group has targeted the Pakistan Navy, the National Logistics Corp, nuclear regulatory bodies, and major telcos and energy providers. Security firm Arctic Wolf discovered the full breadth of the campaign after the group left multiple command and control servers with open directories.
Mythic Likho: Positive Technologies has spotted a new Mythic Likho campaign targeting Russian critical infrastructure orgs with malware such as HuLoader, the ReflekPulse bootloaders, and the Loki backdoor.
UAC-0252: CERT Ukraine has detected a new threat actor targeting government agencies. This one, tracked as UAC-0252, deployed the DEAFTICKK backdoor, the SALATSTEALER infostealer, and the SHADOWSNIFF open-source infostealer.
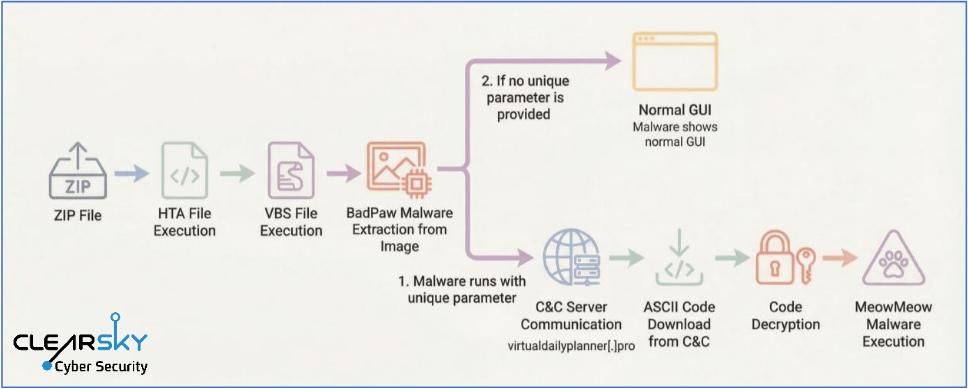
New APT28 campaign targeting Ukraine: ClearSky has spotted a new APT28 campaign targeting Ukraine and using new malware—the BadPaw loader and the MeowMeow backdoor.
New PlugX domains: The Cyber and Ramen team has discovered a bunch of new domains hosting PlugX malware infrastructure for Chinese espionage groups like Mustang Panda, UNC6384, and RedDelta.
"The C2 operator shows a preference for registering once expired domains and pointing them to VPS on ASN 149440 (Evoxt Enterprise) before moving to Cloudflare to mask attacker-controlled infrastructure. The domains are registered via NameCheap and NameSilo, and privacy-protected, in line with behavior previously observed by Recorded Future."
Silver Dragon: A suspected Chinese APT group named Silver Dragon is targeting organizations across Asia and Europe in a campaign employing both spear-phishing and exploitation of public-facing servers. Its main tool is a backdoor named GearDoor. Check Point believes the group is closely connected to the larger APT41 operation.

Vulnerabilities, security research, and bug bounty
Google patches Android zero-day: Google has patched an actively exploited zero-day in the Android mobile operating system. Tracked as CVE-2026-21385, the zero-day impacts a Qualcomm component. It was discovered by Google's security team in December and patched this month.
curl returns to HackerOne: curl has returned to HackerOne after leaving the platform earlier this year after being flooded with AI slop reports. The project experimented with GitHub's bug triage system but got annoyed by several UI and management issues.
"This move turns out to have been a mistake and we are now undoing that part of the decision. The reward money is still gone, there is no bug-bounty, no money for vulnerability reports, but we return to accepting and handling curl vulnerability and security reports on Hackerone."
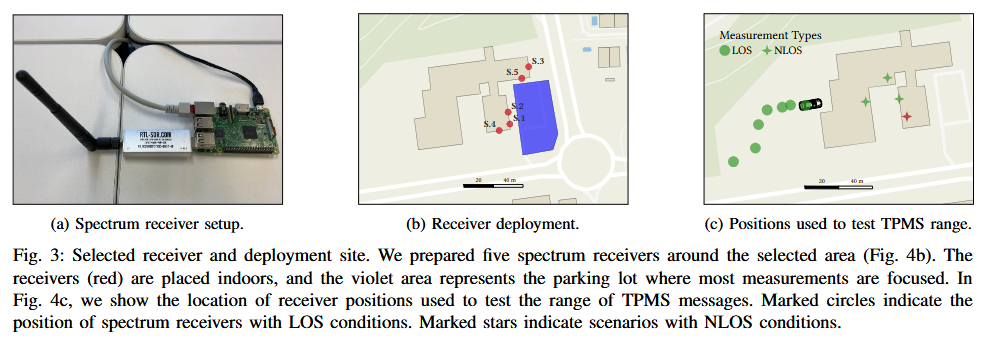
TPMS car tracking risk: Tire pressure monitoring systems (TPMS) installed in modern cars leak data that can be easily harvested to track driver movements. The issue is caused by the tire sensors sending unencrypted data to a car's computer about tire pressure. These signals contain unique IDs that can be used to track individual drivers using covertly installed road radio equipment. According to IMDEA Networks, these messages can travel and be intercepted up to 50 meters.
PerplexedBrowser attack: Zenity Labs has discovered a zero-click attack against Perplexity's Comet agentic browser that allows remote attackers to hijack user sessions, credentials, or steal local files.
Infosec industry
Threat/trend reports: Black Kite, Cloudflare, CyberProof, CyberVandals, Cydome, F6, Henry Jackson Society, HP Wolf Security, and RKS Global have recently published reports and summaries covering various threats and infosec industry trends.
BSides London videos: Talks from the BSides London 2025 security conference, which took place in December, are available on YouTube.
RIP FX: Security researcher Felix Lindner, aka FX, has passed away. I wish I could say more about him, but he was before my time in infosec. Luckily, he has many friends to remember him.
RIP FX - You are a legend
— Jeff Moss (@thedarktangent.defcon.social.ap.brid.gy) 2026-03-02T05:03:13.000Z
phrack.org/issues/68/2#... Another legend has crossed over. Thank you @fxv2.bsky.social for being your kind, brilliant self, whose contributions are too many to name, not just in hacking, but in being a superconnector who I now know is responsible for so many friendships & marriages. You are missed.
— Katie Moussouris (she/her/she-hulk/she-ra)🌻 (@k8em0.bsky.social) 2026-03-02T19:09:55.712Z
Everyone today is a hacker in a sense but there are very few OG hackers on which shoulders we stand
— Daniel Cuthbert (@dcuthbert) March 2, 2026
Oh dude, Felix “FX” Lindner you were so much a hackers hacker and you will be missed
RIP my friend and thank you pic.twitter.com/Ru9j6elbqf
Risky Business podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq how the use of cyber operations in the war in Ukraine has evolved over time.
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about the argy bargy between the Pentagon and AI company Anthropic. US Defense Secretary Pete Hegseth is demanding that all safeguards are lifted from Claude, while Anthropic CEO Dario Amodei is insisting on protections against mass surveillance of Americans and use in lethal autonomous weapons.
