Risky Bulletin Newsletter
April 13, 2026
Risky Bulletin: France takes first steps to ditch Windows for Linux
Written by

News Editor
This newsletter is brought to you by Corelight. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.
The French government is taking its first major steps to ditch Windows for Linux and reduce its dependency on US tech for local European alternatives.
The first department to bite the bullet will be the French Inter-Ministerial Directorate of Digital Affairs (DINUM). The agency is the unofficial IT department for the French government, and this is very likely a test of how a migration could happen at a larger scale.
The decision was announced last week at a seminar between several French government ministries, which also pledged to prepare plans for their own migrations and the alternatives they might need.
The French government is urging agencies to move to European alternatives for US tech products, but the government won't shy away from developing its own tools if it had to, if certain departments need custom software.
DINUM has been a sponsor for several open source projects, including the Matrix secure decentralized communication protocol, which it used as a base for developing Tchap, a secure messaging app used by French government employees.
Tchap itself is part of what DINUM calls LaSuite, a collection of open-source apps already adopted by French government agencies, such as Visio to replace Google Meet and Microsoft Teams for video conferencing, FranceTransfert and Fichiers to replace Google Drive and OneDrive for file sharing, Messagerie to replace foreign email services, and Docs and Grist to replace foreign office suites.
While other EU governments have expressed a desire to move away from US tech as President Trump is throwing sanctions left and right against his allies and lifting sanctions on Russia, the French government is sitting in a prime position for a migration unlike anyone else.
The only thing missing was a native OS, but that's not likely to happen due to the sheer costs DINUM would have to face. The easiest way forward was a migration to Linux and this test will ensure that any migration and compatibility glitches are smoothed out by the very same department that has been behind France's tech sovereignty push so far.
If things go as planned, and I fully expect them to since we're talking about DINUM, France will follow China and Russia to ditch Windows for Linux on the grounds of national security, with more EU countries soon to follow.
There haven't been official migration plans flaunted in other countries as of yet, but smaller local projects got underway after Trump and his buddies made it clear Europe is no longer a friend for them.
Several cities and government agencies in Denmark announced plans to ditch Microsoft products, fearing American espionage, after Trump threatened to invade Greenland last year.
The French city of Lyon followed after that, with a similar announcement.
The German state of Schleswig-Holstein also ditched Windows and Microsoft products last year, moving 60,000 public servants to Linux and other open-source alternatives.
Earlier this month, four Dutch cities announced a pilot program to test a migration of public services to Linux and LibreOffice, just as the government was becoming more and more antsy about hosting their data on the servers of American companies.
All the American tech giants who kissed Trump's feet are about to FAFO as EU countries appear to have had enough of the US' antics and are about to slash a big cut out of the profits of American tech firms as they seek their own digital sovereignty.
Things aren't rosy for the Europeans either. Those very same EU leaders should probably also find a way to develop their own cloud companies, as the EU doesn't have that many hosting alternatives to AWS, Azure, or GCP as of yet. You can create as many crappy M365 clones as you want, but it doesn't mean anything if you're gonna host them on aws-eu-west-3, does it?
Risky Business Podcasts
In this special documentary episode, Patrick Gray and Amberleigh Jack take a look back at hacking throughout the 1990s, from the feel-good vibes of the early hacking communities to the antics of young hackers who wound up on the run from the FBI.
Breaches, hacks, and security incidents
CPUID hacked to serve malware: Hackers have breached the CPUID software project and replaced download links with malware. Malware was added to CPU-Z and HWMonitor, two very popular utilities used to monitor the health of PC components. The malicious download links were live on the official website for only six hours. Security researchers linked the hack to a known cybercrime group that had been distributing malware-laced apps since last year. [Breakglass // Cyderes // Kaspersky]
The CPU-Z and HWMonitor incident is the sloppiest supply chain attack I've EVER seen. The payloads have been copy-pasted from a previous attack, with C2 server reuse. The final implant, STX RAT, wasn't even cleaned from detections with PUBLICLY available Yara rules!🤦[1/4] pic.twitter.com/iE9810XoC2
— Georgy Kucherin (@kucher1n) April 10, 2026
OpenAI rotates certs after Axios attack: OpenAI has released security updates for its macOS apps to rotate their notarization certificate. The old one was exposed in the Axios supply chain attack. OpenAI says the threat actor behind the attack didn't access its dev environment via the compromised Axios library, but it rotated the certificate out of caution anyway. Updates have rolled out for ChatGPT Desktop, Atlas, and the Codex app and CLI.
Orrick, Herrington & Sutcliffe hack and leak: The Silent ransom group has leaked data from another major US law firm, Orrick, Herrington & Sutcliffe. The group leaked data from Jones Day last week. [DataBreaches.net]
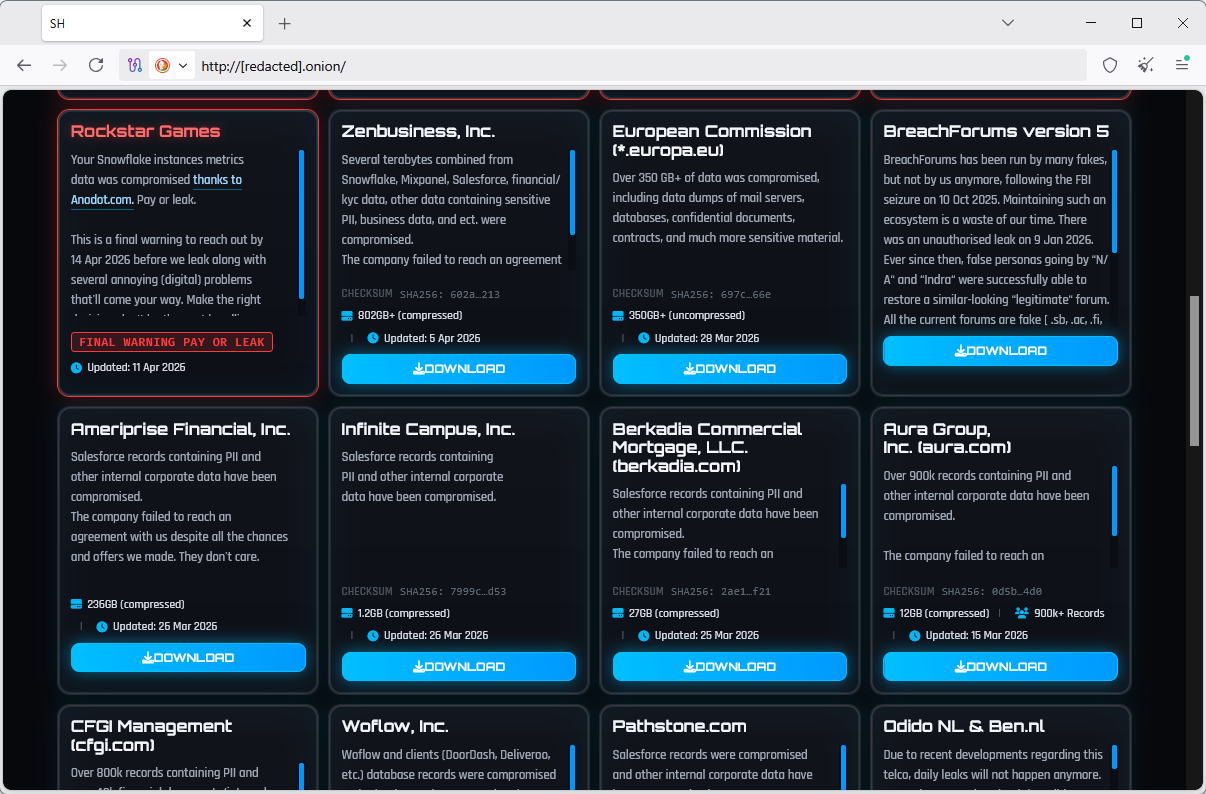
Rockstar Games hacked again: GTA maker Rockstar Games has been hacked and is being extorted by hackers. The ShinyHunters group has given the company until Tuesday to pay a ransom. The group claims it stole data from the company's Snowflake cloud storage after first hacking cloud-cost monitoring tool Anodot. Rockstar Games was also hacked and had its source code leaked in 2022. [IGN]
General tech and privacy
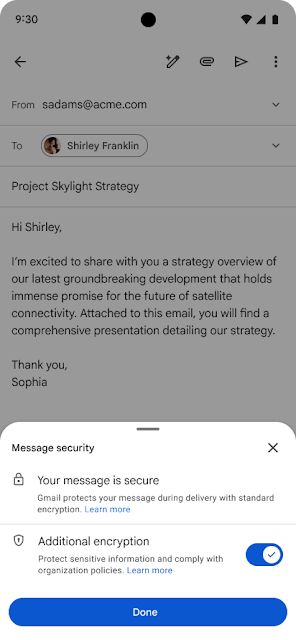
Gmail E2EE expands to mobiles: Google has expanded Gmail's support for end-to-end encryption to its Android and iOS mobile apps.
More Rust in Pixel phones: The Pixel 10 smartphones released last year are the first phones to use Rust for its modem firmware in an attempt to narrow the phone's baseband attack surface.
Bitcoin miners are in trouble: Bitcoin miners have entered the red as it now costs $88,000 to mint a $69,000 bitcoin, in an outcome that was eventually expected to happen but has now been accelerated by the recent military conflicts in Ukraine and Iran. [CoinDesk]
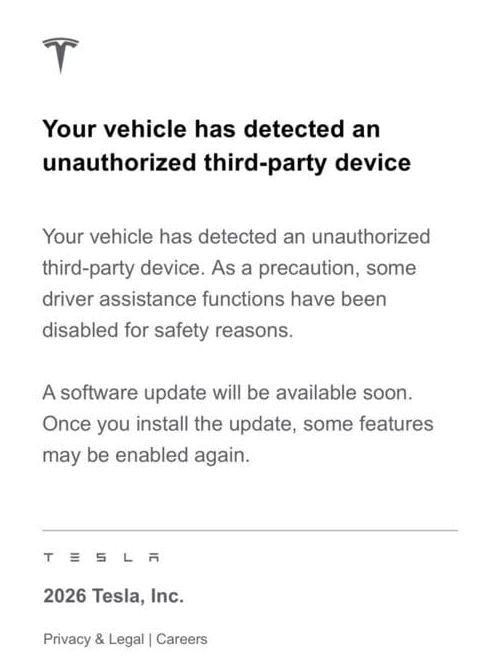
Tesla disables FSD in 100,000+ cars: Tesla has disabled the Full Self-Driving mode in more than 100,000 cars where the feature was enabled using activation hacks. Full Self-Driving is only available in a handful of countries where Tesla received permission from local governments. The feature can be enabled using special devices that trick the Tesla CAN bus into thinking it's operating in one of those countries. An update and email was sent to all car owners who activated FSD through these devices at the end of March. [autoevolution]
Government, politics, and policy
South Korea guarantees free mobile internet access for everyone: The South Korean government will guarantee citizens access to a mobile internet connection. Telco operators will provide users access to the internet at a reduced speed even after they exhaust their monthly limits. The speed will be capped at 400 kbps, enough to allow users to send emails or access government websites. [Yonhap News]
State Department barred from developing fact-checking tools: A DOJ settlement has barred the State Department from funding and developing fact-checking tools and technologies. The Department will also not be allowed to pressure social media companies to censor or downgrade the content of Americans and American companies. Right-wing news outlet The Daily Wire sued the US government in 2023 over alleged claims it had its content downranked on social media.
HHS replaces COBOL system: The US Department of Health and Human Services has replaced its COBOL-based payroll system with a newer cloud-based app. Great success! Just hundreds of more COBOL systems left to go! [NextGov]
UK to introduce prison sentences for tech execs: The UK government is updating its criminal code to counter the spread of AI nudify apps and non-consensual pornography. The update will introduce fines and prison time for tech executives that fail to remove nonconsensual intimate images from their platforms. Owning or publishing pornographic content of incest or adults pretending to be children will also become illegal, along with various other categories of porn.

Sponsor section
In this Risky Business sponsor interview, Corelight’s Senior Director of Product Management, Dave Getman, tells James Wilson how Corelight Agentic Triage helps defenders stay ahead of AI-powered attacks.
Arrests, cybercrime, and threat intel
Authorities seize stolen crypto: US and UK law enforcement have seized $12 million worth of cryptocurrency from a cybercrime operation. The group used a technique called "approval phishing" to gain access to crypto-wallets and empty their funds. Authorities notified more than 20,000 users who allowed hackers access to their wallets. They also seized more than 120 domains the group was using for phishing.

VerifTools arrests: Dutch police have arrested eight suspects who sold forged documents on the VerifTools marketplace. The eight were allegedly the most active users on the platform. Authorities seized the site last August. The site sold thousands of forged documents and made €3 million.
EFCC detains Yahoo boyz fraud academy members: Nigerian authorities have arrested 31 suspects for running online scams from a so-called fraud academy located in the country's capital Abuja. The academy lured individuals with job offers but placed them under guard at its premises, seized phones, and forced them into running online scams. The operation's two leaders were among the 31 arrested.

Twitter brute-forcing botnet exposed its C2: The operator of a Twitter hacking operation has left their brute-force botnet's backend exposed on the internet without authentication. The attacker was targeting users without MFA and was hacking tens of accounts per hour. According to Breakglass Intelligence, the operator is a Turkish speaker and the botnet was also hosted in Turkey.
A nest of RDP badness: A small cluster of only 21 IP addresses are now responsible for more than half of RDP scanning traffic. The addresses are registered to ColocaTel (AS213438), a company based out of the Seychelles. According to GreyNoise, the same company has hosted other clusters of badness that scanned RDPs worldwide in the past.
Datto RMM abuse: Fortra has spotted phishing campaigns trying to lure victims into installing Datto's CentraStage remote monitoring and management tool, which attackers are then using to connect back into the victim's internal network.
Device code phishing: Microsoft has published a report with IOCs on the wave of device code phishing hitting its service over the past month. The interesting part here is that several other security firms spotted this way before Microsoft, the company that operates the device code authentication system in the first place.
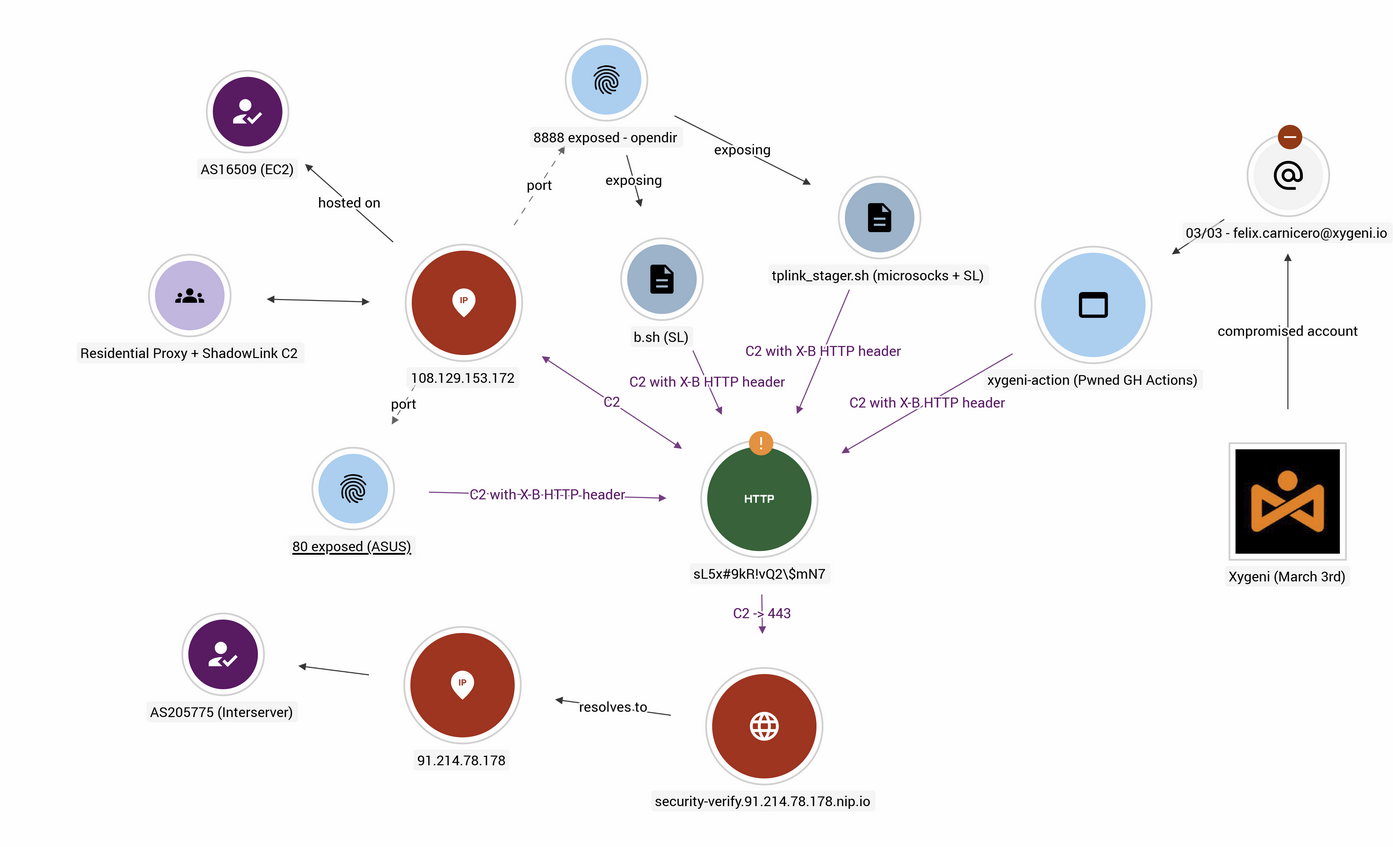
The plot thickens: Multiple connections have been found between the compromise of the Xygeni vulnerability scanner on GitHub and a proxy botnet of hacked ASUS and TP-Link routers. The two operations used the same command-and-control servers and the same authentication secret for the C2 protocol. The Xygeni compromise took place two weeks before similar hacks at the Trivy and KICs scanners. Those latter incidents were linked to a hacker group named TeamPCP. Researchers have not linked Xygeni to TeamPCP but pointed out that TeamPCP used the same techniques and also operated proxy botnets. [Ctrl-Alt-Intel]
Malware technical reports
Ottercookie: Panther looks at Ottercookie, North Korea's favorite infostealer as of late.
GIFTEDCROOK Stealer: Synaptic Systems looks at the obfuscation of GIFTEDCROOK, an infostealer used by UAC-0226 in attacks targeting Ukrainian orgs.
ASO RAT: Breakglass researchers have published a technical analysis of ASO RAT, a custom-built Android remote access trojan that was discovered deployed exclusively against Syrian targets. The malware's coder appears to speak Arabic.
REFUNDEE: The Breakglass looks at REFUNDEE, a mixed PhaaS and RAT-as-a-Service that left its server directories exposed on the internet.
Mirax: Cleafy has managed to get its hands on a sample of the new Mirax Android malware, spotted advertised on hacking forums last month. Per the company's analysis, the malware is being distributed using Meta malvertising campaigns, targets Spanish-speaking audiences, and is used to dump credentials and turn phones into residential proxies.
Qilin ransomware: Kirk of Derp.ca has published an analysis of the Qilin ransomware's Windows cryptor.
Sponsor section
James Pope, Corelight's Director of Technical Marketing Engineering, demonstrates the company's Open NDR Platform and how it combines network detections with a whole host of other data sources.
APTs, cyber-espionage, and info-ops
DPRK IT worker cluster: Blockchain investigator ZachXBT has discovered a cluster of 390 DPRK remote IT worker accounts making roughly $1 million/month.
Contagious Interview hits Reddit: ReversingLabs has spotted one of the DPRK's Contagious Interview campaigns targeting job seekers online, with the first time seeing them target people on Reddit, among many other places. (They prolly did it before, but this is the first time I see it in a report.)
Kimsuky C2: Researchers have dumped the contents of a Kimsuky C2 server to find a bunch of new and old malware, along with source code. I like how security firms aren't hiding the fact that they go into C2 servers to retrieve adversary tooling anymore. This used to be a big taboo once and infosec people wouldn't pretend they didn't do it and that all malware fell from the VT heavens. [Breakglass]
DPRK targets Polymarket bot devs: North Korean hackers (Famous Chollima) have been spotted publishing malicious npm packages that target developers of Polymarket betting bots. [Panther]
More Russian info-ops evasion: Russia's propaganda machine is using YouTube accounts registered in Monaco to evade the EU's sanctions and broadcast their Kremlin bs to French-speaking audiences. Obviously, the same channel also glorifies and hosts French far-right figures, the same that want to lift sanctions on Russia and are without a doubt a naturally established political movement and definitely not a foreign operation. [DFRLab]
APT35 profile: With Iranian hackers doing the hacking in every direction, CloudSEK has published a profile of the APT35 group's most common TTPs.
CyberAv3ngers profile: Tenable looks at the evolution of CyberAv3ngers from a lowly hacktivist group running a bunch of fake hack claims to an advanced APT pulling off some pretty big intrusions as of late.
"The group's trajectory from default credential exploitation in 2023, to custom ICS malware deployment in 2024, to active exploitation of Rockwell Automation controllers in 2026, demonstrates a deliberate capability escalation that tracks the broader maturation pattern Dragos identified across Iranian ICS-targeting groups–adversaries moving beyond pre-positioning to actively understanding and manipulating physical processes."
Vulnerabilities, security research, and bug bounty
Adobe patches Reader zero-day: Adobe has released an out-of-band security update to patch an Acrobat Reader zero-day. Tracked as CVE-2026-34621, the zero-day had been exploited in the wild since at least November. The attacks were spotted by Expmon founder Haifei Li. Adobe's regular Patch Tuesday is scheduled later this week.
Marimo bug exploited in the wild: Threat actors are exploiting a vulnerability in the Marimo notebook platform. Attacks started last week, less than ten hours after details were posted online. Tracked as CVE-2026-39987, the vulnerability is a pre-authentication remote code execution that lets attackers hijack Marimo notebooks hosted online. [Sysdig]
Juniper security updates: Juniper released a batch of 28 security updates on Friday.
MAX riddled with bugs: Russian security researchers have filed more than 200 bug reports in the Kremlin's MAX national messenger. The Russian government has awarded more than $300,000 (~23.5 million rubles) in payouts across three bug bounty platforms. Several major vulnerabilities were allegedly patched, with the most common reported bug class being insecure direct object references (IDOR) access issues. [Kommersant]
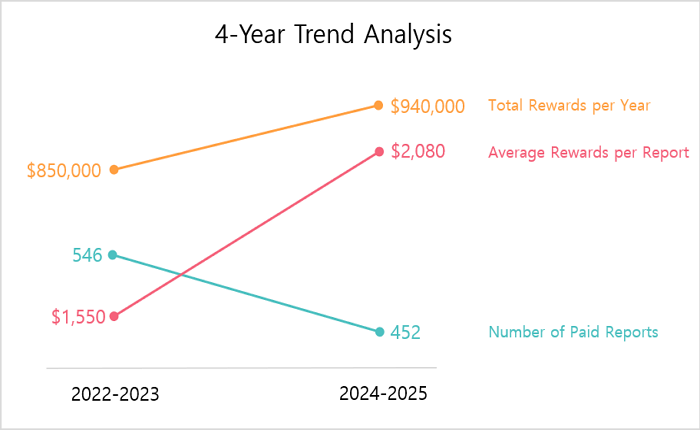
Samsung VRP: Samsung awarded almost $1 million in bug bounty rewards last year.
EngageSDK vulnerability: Microsoft has published a technical write-up of an intent redirection vulnerability it found last year in the EngageSDK, a library for managing push notifications. The bug could have been exploited to escape the Android app sandbox and access sensitive data stored on the device by other apps.
"Following our Coordinated Vulnerability Disclosure practices (via Microsoft Security Vulnerability Research), we notified EngageLab and the Android Security Team. We collaborated with all parties to investigate and validate the issue, which was resolved as of November 3, 2025 in version 5.2.1 of the EngageSDK."
Docker auth bypass: A vulnerability in the Docker containerization technology can allow threat actors to deploy privileged containers with host filesystem access. The issue can be exploited by sending an oversized HTTP request to the Docker API. This allows attackers to bypass any Docker authorization plugins. The bug, tracked as CVE-2026-34040, stems from incomplete patches for an older 2024 vulnerability (CVE-2024-41110). It was patched at the end of March. [Cyera]
NGINX RCE write-up: Security firm Calif has published a technical analysis of CVE-2026-27654, an unauth RCE they found in the NGINX web server with the help of the Claude AI agent. This was patched at the end of last month.
Slippi RCE: Security researchers have found a remote code execution in Slippi, a GameCube and Wii emulator to let users play old titles in multiplayer mode over the internet. The RCE is in the Slippi spectator mode that lets users watch others' matches.
"This vulnerability is patched in Slippi Playback Dolphin 3.5.2, released January 14th, 2026. The launcher automatically updates it."
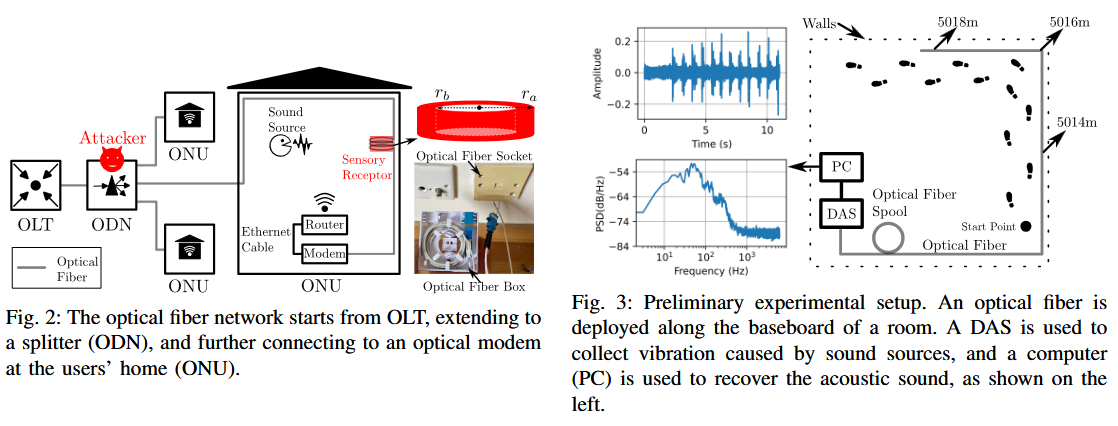
Fiber used as a microphone: A team of academics from Hong Kong has developed a technique to use the fiber optic cable going into a location as a spy into that facility, using it as a means to capture and extract sound vibrations from those premises.
Infosec industry
Threat/trend reports: Analyst1, Cerby, F5, Hiscox, LayerX, MIND, Positive Technologies, and Wiz have recently published reports and summaries covering various threats and infosec industry trends.
New tool—Janus: Security firm SpecterOps has open-sourced Janus, a tool to analyze C2 telemetry data to surface failure patterns, operator friction, and automation opportunities across engagements.
New tool—EyeWitness: Security firm Red Siege has published EyeWitness, a tool to take screenshots of websites, provide server header info, and identify default credentials if known.
New tool—AWS-Preflight: Cloud security engineer Gabriel Pavel has released AWS-Preflight, a security linter for AWS CLI commands to catch misconfigurations before they hit production.
"703 security checks across 91 AWS services. Findings include severity ratings and a remediated command."
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about the State Department taking to X to counter foreign propaganda. US Secretary of State Marco Rubio dismantled the State Department's counter-propaganda office when he took charge, but it turns out that giving adversary states free reign online is a bad idea.
We recently launched a new podcast series called Risky Business Features. In this episode, investigative journalist Geoff White joins James Wilson for a look into the complex machine that is North Korea’s IT worker infiltration scheme.
