Risky Bulletin Newsletter
August 29, 2025
Risky Bulletin: npm attack uses AI prompts to steal creds, crypto-wallet keys
Written by

News Editor
This newsletter is brought to you by Okta. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
A novel supply chain attack has hit the users of NX, a popular developer tool used to automate and optimize CI/CD pipelines.
The incident took place on Tuesday, after a threat actor compromised the npm token for one of the NX developers, and then released malicious updates for several NX tools to the npm package repository.
The new versions contained a malicious script that:
- Attempted to run a prompt on local AI CLI tools like Claude, Gemini, and Q.
- The prompt instructed the AI agents to search the local filesystem for text-based files that may contain GitHub tokens, npm tokens, SSH keys, .env secrets, and wallet files.
- All found data was encoded and written into a file.
- Other commands would use the GitHub API to create a new public repository on the infected user's GitHub account and upload the file with all the stolen data.
- The script also adds a shutdown command to the local shell environment (~/.bashrc and ~/.zshrc) that would restart the developer's machine every time the terminal was started.
All public GitHub repos containing stolen data used the same "s1ngularity-repository-" prefix, making them easy to spot on GitHub.
This is probably how the attacker collected the stolen data, without using a third-party server, which is dangerous since it may lead investigators back to the attacker(s).
According to a GitHub search, there were around 1,400 GitHub repositories with that prefix, which is roughly the number of users the attacker infected before the malicious NX libraries were taken off npm.
GitHub has also hidden the repositories and notified affected users.
The malicious libraries were live for 5 hours and 20 minutes, but were quickly taken down, mainly due to NX's huge popularity in the dev community.
An attack like this typically works best against smaller projects, not against one with 4.6 million weekly downloads.
Adding that shutdown loop to the terminal environment was also a dumb idea, since that basically made every developer go into debug mode and look for what happened.
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
Ransomware attack disrupts Swedish government: A ransomware attack has disrupted the activity of more than 200 Swedish municipalities and regional governments. More than 80% of local city governments are affected. The attack hit Miljödata, a shared IT provider. Attackers have allegedly requested a ransom of 1.5 Bitcoin (~$160,000). [Additional coverage in Aftonbladet/English coverage in The Record]
TransUnion hack: US credit union TransUnion says a July security breach exposed the details of 4.4 million customers.
SK Telecom receives mega fine: South Korea's privacy regulator fined the country's largest telco $97.2 million (134.8 billion won) over a major security breach. Hackers stole the SIM card data of over 23 million SK Telecom users in a breach this April. The fine is South Korea's largest penalty imposed over a hack. The Personal Information Protection Commission said SK Telecom failed to protect user data and report the breach to authorities in due time. [Additional coverage in BusinessKorea]
BetterBank crypto-heist: A hacker has stolen almost $5 million worth of crypto-assets from DeFi platform BetterBank. The hacker returned around 80% of the stolen funds a day later. [Additional coverage in BitGet]
General tech and privacy
4chan, Kiwi Farms sue Ofcom: Two of the internet's worst websites—4chan and Kiwi Farms—have sued the UK's Office of Communications (Ofcom) over the country's age verification law. The two sites claim the UK law represents a foreign attempt to restrict the free speech of Americans and that Ofcom is a global censorship bureau. [Additional coverage in CourtWatchNews]
OpenSSH PQC warning: OpenSSH v10.1 will show warnings if users connect to an SSH server that does not have post-quantum cryptography protections.
Windows 11 is the best: Microsoft is adding a dedicated keyboard shortcut for En dash (–) or Em dash (—) in Windows 11.
"Going forward, pressing WIN + Minus (-) will insert En dash, and WIN + Shift + Minus (-) will insert Em dash."
Cloud auto-save coming to Word: Microsoft Word is adding a new option to automatically save all new files to the cloud, and free users from the burden of having to save their work at regular intervals.
Government, politics, and policy
EU Cybersecurity Reserve: The EU has designated its cybersecurity agency ENISA to manage the EU's Cybersecurity Reserve. ENISA will receive €36 million in funding for the cyber reserve's activity. The funds will be used to contract cybersecurity providers in cases where the Cybersecurity Reserve needs to be deployed. The EU established the Cybersecurity Reserve under the EU Cyber Solidarity Act to provide incident response during major cyber incidents at member states or EU bodies.
US House to investigate Wikipedia: Two Republican lawmakers launched an investigation into efforts to manipulate Wikipedia. James Comer (R-Ky) and Nancy Mace (R-SC) cited campaigns designed to push anti-Israel and pro-Kremlin narratives on the site. The two have requested that the Wikimedia Foundation provide records on accounts involved in the influence campaigns and how the organization handled them. [Additional coverage in Gizmodo]
Russian code in the DOD: According to NextGov, a silly innocent little uncospicious naive friendly Russian developer is the sole maintainer of a library used across 30 DOD software packages. Nothing here, please move along! I SAID MOVE ALONG!!!
Trump threatens entire countries after Meta meeting: According to Bloomberg, Donald Trump threatened to impose "substantial tariffs" on countries that impose digital taxes on US tech firms. This came after a meeting with Meta's head Mark Zuckerberg. If I were one of those countries, I'd just outright ban Meta sites, but what do I know?
Nothing like running federal policy and the economy via threats, bribery and coercion.
— BK (@bk13k.bsky.social) 2025-08-28T19:13:55.995Z
Sponsor section
In this Risky Business sponsor interview, Tom Uren talks to Brett Winterford, Okta's VP of Threat Intelligence, about FastPass. Brett explains what it is, how Okta uses it, and why threat actors avoid it.
Arrests, cybercrime, and threat intel
Germany charges Rosneft hacker: German authorities have charged a local man with hacking the German subsidiary of Russia's Rosneft state-owned oil company. The suspect allegedly hacked Rosneft in March 2022, shortly after Russia's invasion of Ukraine. He stole 20TB of data and deleted crucial systems. The incident shut down Rosneft operations for days. The company estimated the damages to €9.75 million.
Spain arrests school hacker: Spanish police arrested a hacker who broke into a government school platform to change grades for the baccalaureate and university national selection exams. The hacker allegedly used compromised teacher credentials to access the Seneca scoring platform. One of the teachers spotted the intrusion and alerted authorities. Police found a notebook at the hacker's home in Seville with a list of all changed scores. The suspect allegedly has a history of similar crimes. [Additional coverage in Diario de Jerez] [h/t DZ46]
Taiwan arrests two data traders: Taiwanese authorities have detained two local men on charges of trading in hacked data. The two allegedly handled and sold data stolen by a Chinese ransomware crew from Taiwanese organizations. In April, Taiwanese authorities linked the CrazyHunter ransomware to a Chinese man working for a Chinese cybersecurity company. The attacks hit 11 Taiwanese organizations, including three major hospitals. [Additional coverage in Taiwan News] [h/t DataBreaches.net]
Instacart fraudsters charged: US authorities have charged eight men for a large-scale fraud operation that stole more than $30 million from grocery delivery services Instacart and Shipt. According to Forbes, the group used legitimate accounts to place orders that were picked up by hacked accounts. The suspects bought gift cards and cryptocurrency with funds routed by Instacart and Shipt to gig workers to cover grocery pickup bills. They canceled orders after hijacking funds and then switched to new accounts. According to the FBI, the group used more than 7,500 hacked gig worker accounts since 2022 as part of the scheme.
VerifTools seized: US and Dutch authorities have seized an online service that sold forged IDs. The VerifTools service has been online since 2022 and has sold forged driver's licenses, passports, and other identification documents. The site made at least €1.3 million.
US sanctions DPRK remote IT worker network: The US Treasury has imposed sanctions on a Russian national and a Chinese front company for helping launder the salaries of North Korean "remote IT workers."
Purgatory group behind US university swatting: An online Telegram group named Purgatory is behind a series of fake active-shooter alerts at US universities over the past week. The group is selling swatting services for prices ranging from $20 to $50. They are also offering intimidation services, like tire slashing and throwing bricks through windows, for as little as $10—although, prices have now gone up due to the group's success. Purgatory's admin claims to have made more than $100,000 since the swatting spree began. According to WIRED, the Telegram group has connections to an online community known as The Com.
Anthropic disrupts GTG-2002: AI company Anthropic has disrupted the activity of a cybercrime operation. The group, tracked as GTG-2002, was allegedly using the Claude Code AI agent to automate data theft from compromised environments. Anthropic found evidence of the group breaching at least 17 different organizations.
VS Code Marketplace loophole: ReversingLabs found a loophole on VS Code Marketplace that allows threat actors to reuse old, removed package names for malicious purposes.
FIFA WC26 campaigns ramping up: BforeAI has spotted almost 500 malicious domains preparing to target the FIFA World Cup 2026 tournament in the US. The early bird catches the worm!
SilverFox campaigns: Check Point looks at the recent campaigns of SilverFox, a suspected financially motivated threat actor with infrastructure inside and targeting China.
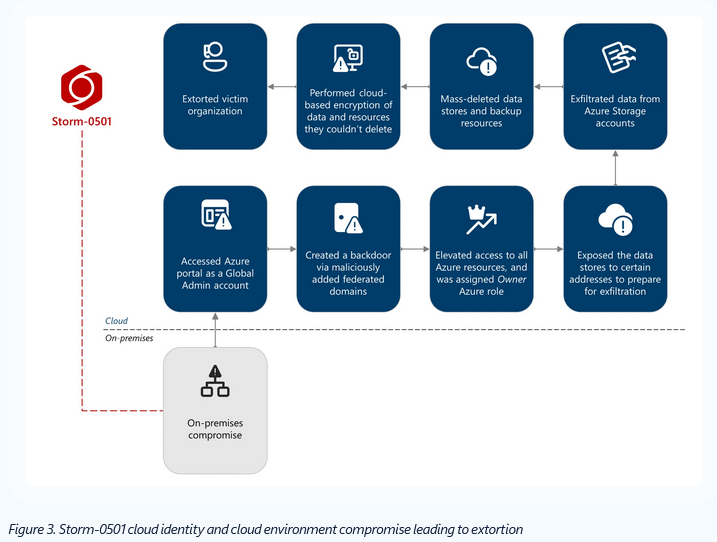
Storm-0501 destroys cloud data: A hacking group tracked as Storm-0501 is hacking into cloud environments, stealing data, deleting files, and then asking for ransoms. The group previously targeted corporate systems with classic ransomware. It switched to hybrid cloud environments last year, before focusing primarily on cloud attacks this year.
ScreenConnect phishing campaign: Trustwave researchers have spotted a phishing campaign using AI-themed lures to trick users into running an executable containing a malicious, pre-configured ScreenConnect installer. Attackers used the ScreenConnect app to access infected systems and deploy the Xworm RAT.
Velociraptor abuse: Sophos researchers have spotted threat actors abusing Rapid7's Velociraptor DFIR tool in attacks. They used the tool to download apps and create tunnels.
DPRK IT worker research: Threat intel analyst Rakesh Krishnan has published new research unveiling new clusters of North Korean remote IT workers.
"In this article, we shall explore various GitHub Profiles and other Code sharing platforms, along with Resumes of DPRK IT Workers, to assess a greater picture of the Remote Job Market in North Korea via Fake Identities."
Meta malvertising goes wild: Because the last time Meta removed malicious ads from its platform was the Paleozoic era, a malvertising campaign that used Meta ads to trick users into installing Windows malware has now expanded with Android payloads! Yoohoo!!!
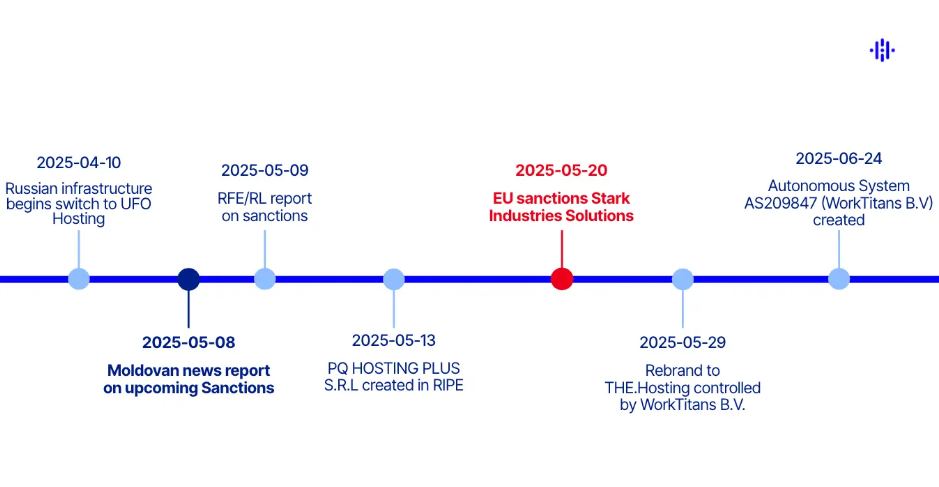
Stark Industries rebrand: Recorded Future looks at how bulletproof hosting provider Stark Industries migrated its infrastructure and rebranded days before it was sanctioned by the EU.
Malware technical reports
MystRodX backdoor: QiAnXin has spotted MystRodX, a new C++ backdoor deployed on *NIX systems, acting as a dropper for other payloads.
AppSuite PDF Editor backdoor: G DATA has found a backdoor hidden in the AppSuite PDF Editor software.
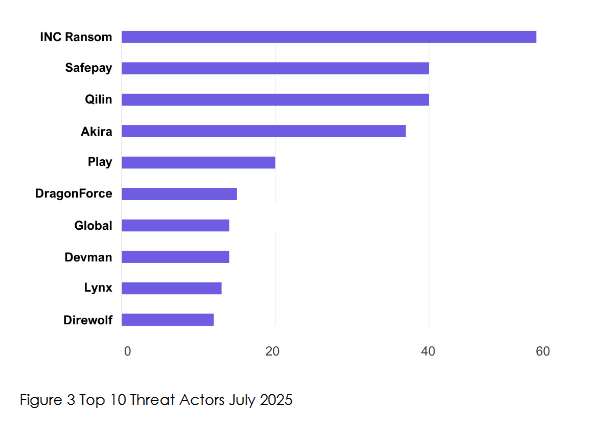
Qilin ransomware: Threat intel firm KELA has published a profile on the Qilin ransomware.
BQTLOCK ransomware: K7 researchers have published a report on the BQTLOCK ransomware and its multiple variants and names.
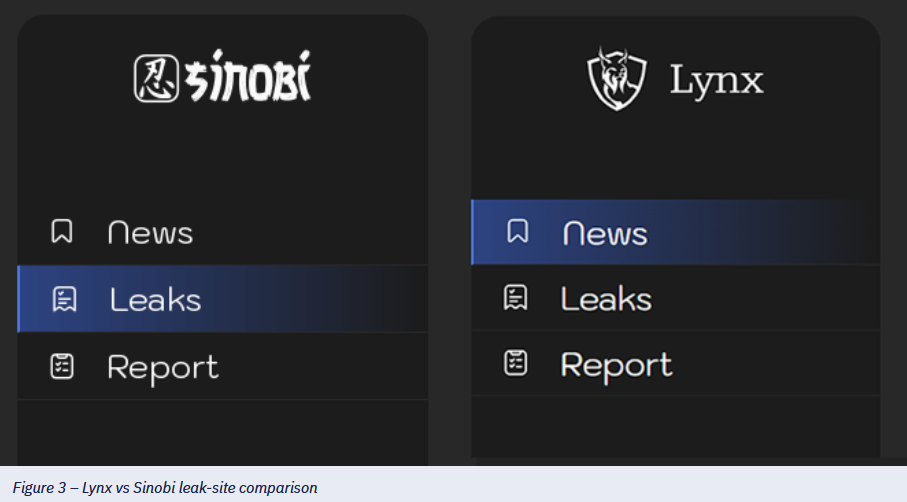
Sinobi ransomware: eSentire looks at the Sinobi ransomware, deployed via compromised SonicWall VPNs. The ransomware is a rebrand of the old Lynx RaaS, which is quite obvious from their UI and code.
Sponsor section
In this sponsored product demo, Okta's Harish Chakravarthy and Brett Winterford walk through four new features Okta introduced in the wake of the emergence of modern attacker techniques targeting identity providers. These features will help you to prevent or limit the damage to your environment if an attacker manages to compromise a session token. If you're an Okta shop, you should absolutely watch this video.
APTs, cyber-espionage, and info-ops
Salt Typhoon hacks now linked to three Chinese firms: Three Chinese tech companies are behind a global hacking campaign tracked as Salt Typhoon. The intrusions target telecommunications, government, transportation, and military networks. Cybersecurity agencies from 13 countries say the hacks have now reached more than 80 countries. Authorities linked the intrusions to Sichuan Juxinhe Network Technology, Beijing Huanyu Tianqiong Information Technology, and Sichuan Zhixin Ruijie Network Technology.

TAOTH campaign: A suspected Chinese espionage group has taken over the expired domain for an end-of-support application to deliver malicious updates. The campaign targeted Sogou Zhuyin, an editor for inputting traditional Chinese characters. Several hundred victims were infected with the group's malware. Trend Micro says the campaign was highly targeted and went after dissidents, journalists, researchers, and business leaders.
ShadowSilk (YoroTrooper): A mysterious cyber-espionage group named ShadowSilk (Silent Lynx, YoroTrooper) appears to include both native Russian and Chinese-speaking operators. The group has been active since 2023 and was still launching operations last month. Its main targets are governments in Central Asia. It's unclear for which government the group operates, or if the Chinese and Russian operators cooperate on an official level or are just for-hire mercenaries.
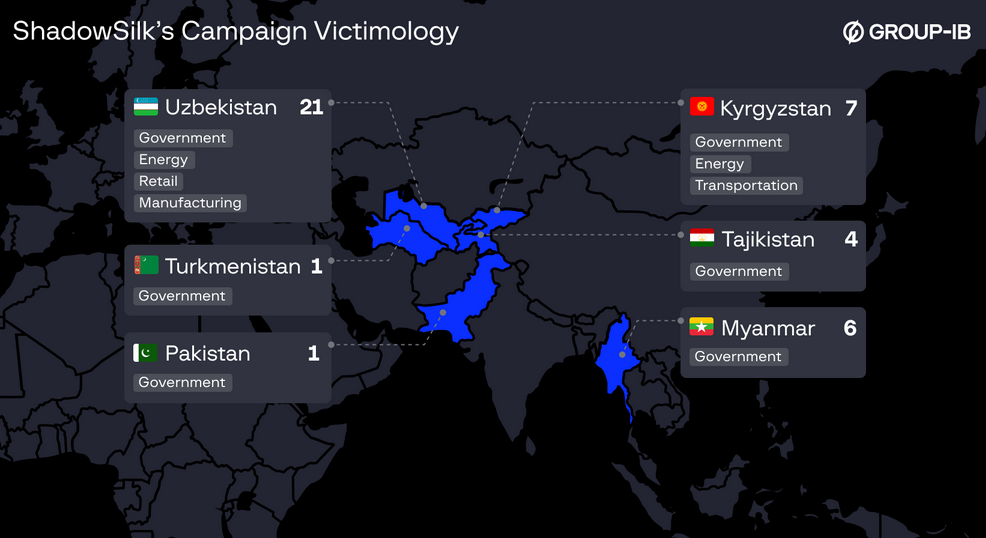
I find this report by Group-IB quite intriguing since it would appear to suggest a collaboration between Chinese and Russian actors. That itself is interesting and would appear to mimic the geopolitical landscape where Russia and China are quite cozy. https://www.group-ib.com/blog/shadowsilk/ […]
— Christoffer S. (@cstromblad.com) 2025-08-27T08:28:50.000Z
Vulnerabilities, security research, and bug bounty
CrushFTP zero-day write-up: WatchTowr Labs has published a technical analysis of CVE-2025-54309, a zero-day in CrushFTP patched in late July.
FreePBX zero-day: Hackers are exploiting a zero-day vulnerability in the FreePBX open-source telephony software. The attacks are targeting the FreePBX systems with their control panel exposed on the internet. Attacks have been traced as early as August 21. A patch is expected by the end of the week.
BadSuccessor bug can still be exploited: Akamai says that Microsoft's patch for the BadSuccessor bug, which the company released this month as CVE-2025-53779, can be bypassed through a different exploitation method.
Cisco security updates: Cisco has released ten security advisories for its firewall products.
Infosec industry
Threat/trend reports: Kaspersky, NCC Group, Netscout, and Recorded Future have recently published reports and summaries covering various infosec trends and industry threats.
New tool—vCenterHound: Security researcher Mor David has open-sourced vCenterHound, a tool to collect infrastructure and permissions data from vCenter and export it as a BloodHound‑compatible graph.
Google establishes disruption unit: Google is establishing a cyber disruption unit. The company says more details will be provided in the coming months as the cyber offensive landscape evolves in the US. The Trump administration has advocated this year for the US to go on the cyber offensive and start hacking back. Recently proposed legislation would allow the President to give letters of marque to contractors for certain types of hacking operations. [Additional coverage in CyberScoop]
Acquisition news: Cybersecurity industry giant CrowdStrike has agreed to acquire Onum, a company specializing in real-time telemetry management. The transaction is estimated at around $290 million.
Sophos rebrand: Well, in "design is my passion" news, Sophos announced a new visual rebrand this week. I'll give it a 9/10 rating.

Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about proposed legislation that would allow the President to license private sector hackers to go after cybercrime groups. The bill won't pass, but letting hackers loose on industrial-scale scam farms actually makes sense.
In this edition of Between Two Nerds, Tom Uren and The Grugq talk about how the teenage hacking groups Scattered Spider, Lapsus$, and ShinyHunters are collaborating.
