Risky Bulletin Newsletter
March 27, 2026
Risky Bulletin: Russia to use custom crypto-algorithm for its 5G network
Written by

News Editor
This newsletter is brought to you by Authentik. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
The Russian government is working on a law that would require all mobile operators to use a custom domestically-developed encryption algorithm for the country's 5G mobile network.
If the bill passes, all phones sold in Russia going forward will have to support the NEA-7 algorithm or they will not be able to connect to Russian mobile networks.
Foreign algorithms such as SNOW (used in Europe), AES (used in the US), and ZUC (used in China) will be supported only until 2032, as part of a transitional phase to allow current smartphones to reach their end-of-life.
Work on the proposed regulations began last year and the bill is now in its second draft, according to Russian news outlet Izvestia.
The bill is part of a broader set of measures designed to hinder the operations of Ukrainian drones and missiles, which have used Russian SIM cards to connect to mobile towers, determine their location, and then guide themselves to planned targets.
Using a custom encryption algorithm to encrypt 5G traffic won't stop the Ukrainian side from using Russia's mobile network, since they can always fall back to older protocols like LTE and 3G.
On the other hand, the proposed law is a "patriotic" legislative flex. It's the type of unrealistic stuff that's happening in the Russia Duma all the time these days, to show that Russia is important and still matters on the global stage.
As Izvestia points out itself, Russia is insignificant on the mobile market, where it only accounts for 2% of annual sales, so it's very possible that most phone makers won't bother to implement NEA-7 on their chipsets.
There is also no base tower equipment that supports the algorithm, which raises the possibility that Russia will be years behind in rolling out its 5G network.
The Russian news outlet warns that NEA-7 may be used as a trojan horse by foreign manufacturers to request a favorable market position or a monopoly in exchange of adding the algorithm to their firmware.
On Ukraine's side, the answer is likely to be the same as in Russia's rollout of MAX. The Ukrainian intelligence services were delighted that Russia was mandating everyone in their country use an incredibly insecure and easy-to-hack mobile app.
Rolling out an untested and largely unknown encryption algorithm for your entire future mobile network may be a major opportunity for hacks and surveillance operations if you know your way around encryption, and intelligence services usually do.
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
Malware found on Luxembourg govt devices: Hackers breached the MDM platform of the Luxembourg government and deployed malware to the devices of public sector workers. More than 4,850 phones and tablets were infected at the end of February. All have since been updated and secured, according to the country's digitalisation minister. [Luxembourg Times]
Dutch Police disclose breach: The Dutch national police are investigating their own security breach after an employee fell for a phishing attack. Officials say they detected the attack right away and closed the attacker's access. An investigation is underway to determine what data was accessed.
Ajax leaks supporters' details: A hacker has breached the stadium management system of Dutch soccer club Ajax Amsterdam. The hacker could modify ticket details and see supporters' personal details. The club confirmed the incident after the hacker leaked a list of supporters banned from attending games to journalists. [RTL Nieuws]
Puerto Rico cyberattack: A cyberattack has disrupted the activities of the Puerto Rico Department of Transportation. Officials canceled all future appointments for vehicle registrations and driver's license issuance until the issue is resolved. The agency didn't say if the incident was ransomware. [The Record]
Ransomware at Vigo port: A ransomware attack has disrupted the port of Vigo, one of Spain's largest cargo ports. Officials have disabled IT systems and are now running the port manually. Cargo loading and unloading has not been disrupted. No ransomware group has claimed responsibility for the attack so far. [The Record]
Politico investigates possible hack: News outlet Politico Europe is investigating an incident where a call between one of its reporters and a EU official was recorded and posted online. The call was related to Hungary and Ukraine. Several Slovak and Hungarian pro-government news sites covered the call. The breach is being investigated as a possible hack.
Someone (probably Russia?) hacked a call bt an EU pol and a Politico journalist as part of Russia's attempt to help Orbán. So Politico did a security review and posted it. www.politico.eu/article/poli...
— emptywheel (@emptywheel.bsky.social) 2026-03-25T08:51:20.798Z
LiteLLM hack: Python AI package LiteLLM has been compromised as part of the TeamPCP hacks that hit Trivy and KICS last week. This is just the first victim in a long trail of hacks that will come to light in the aftermath of the Trivy and KICS incidents. [DataDog // Endor Labs // OpenSourceMalware // SlowMist // Step Security]
NSCC hack: That hack of the National Super Computer Center of China (NSCC) is becoming more real by the day. [NetAskari]
"That is of course not irrefutable proof and we always recommend to take anything on this story with a grain of salt, but the overall details we received so far seem like that this operation is more in the realm of 'real' than 'fake'."
At least 50 data-wiping incidents in Israel: At least 50 Israeli companies suffered data-wiping incidents over the past weeks. Twenty different groups were behind the attacks, according to Israel's National Cyber Authority. The attacks came in the aftermath of Israel's military campaign in Iran. Israeli officials warned companies that wiping attacks are likely to continue even after a ceasefire. [Israel National News] [h/t DataBreaches.net]
Hardware implant found at Ukrainian drone factory: Russian intelligence services installed a hardware listening device at a Ukrainian drone factory. The wiretap device was embedded in a thermostat and included a camera, microphone, and router. Drone maker TechEx says it knew of the device before it was installed after receiving a warning from Ukrainian intelligence. The company worked with the SBU to share incorrect intelligence. [24tv // Interfax Ukraine]

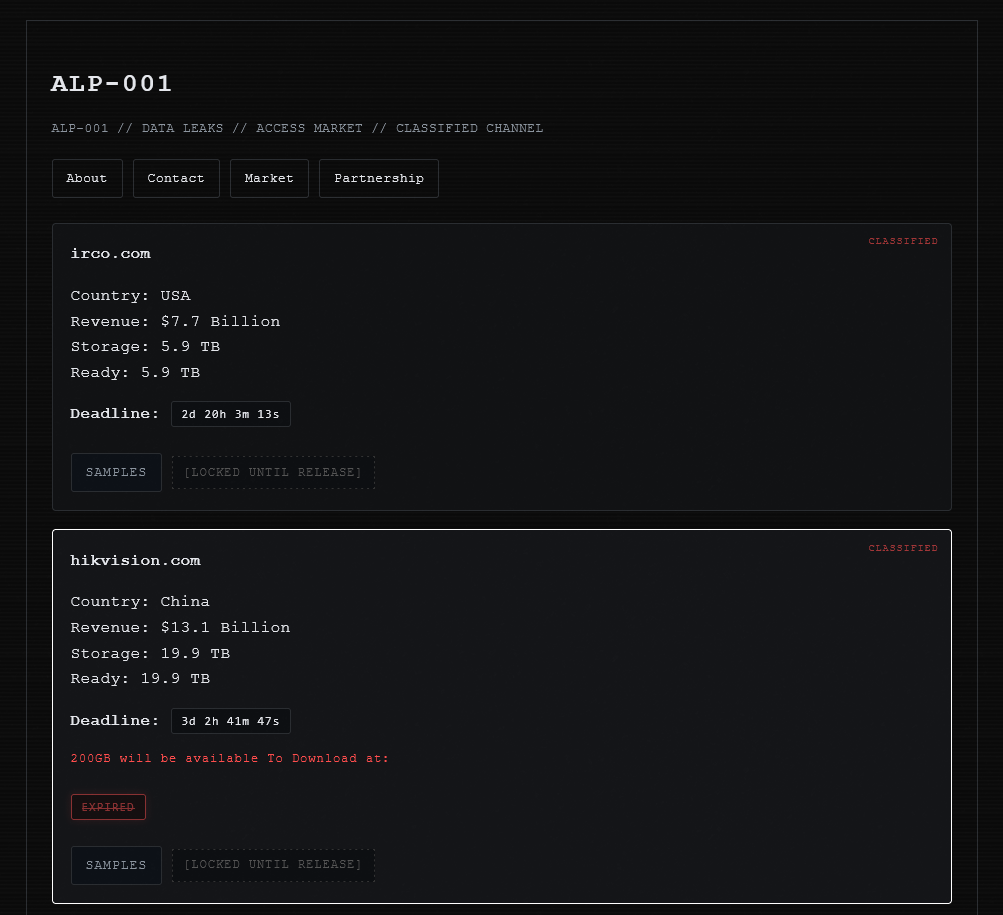
Hikvision ransomware attack?: A newly launched ransomware group has listed Chinese hardware vendor Hikvision on its dark web leak site.
General tech and privacy
Google moves Q Day to 2029: Google expects threat actors to break classic encryption using quantum computers by the end of the decade. The company has introduced a 2029 timeline to secure its products with post-quantum cryptography (PQC) protections. Chrome and Google Cloud already have PQC protections in place, while Android is getting them later this year. [ArsTechnica]
Meta whistleblower lawsuit dismissed: A judge has dismissed a lawsuit filed by Meta's former head of security. Attaullah Baig sued the company last year for wrongful termination. He argued the company fired him after he found serious privacy violations inside the company's WhatsApp division. [Courthouse News]
TailsOS 7.6: The Tor Project has released TailsOS 7.6, which replaces the OS' default password manager from KeePassXC with Gnome Secrets.
Apple rolls out age checks in UK: Apple has rolled out age checks for iPhone and iPad users in the UK. Customers who update to iOS 26.4 will be asked to verify their age to use certain apps. Verification includes adding a credit card or scanning their ID. [Politico Europe]
EU investigates Snapchat: The EU has announced an investigation into Snapchat's age control and child protection features after reports of minor grooming on the platform.
EU finds four pr0n sites guilty: An EU investigation found that four adult sites—Pornhub, Stripchat, XNXX, and XVideos—failed to implement proper measures to block children from accessing their content.
Wikipedia bans AI-generated articles: The WikiMedia Foundation has banned editors from using AI tools to write or rewrite Wikipedia articles. The Foundation said LLMs violate multiple of the site's core policies, such as accuracy and verifiability. The change applies to the English version of Wikipedia. Editors are still allowed to use AI to translate content into English. [Dexerto]
Meta and YouTube lose social media addiction case: A California jury found Meta and YouTube guilty of failing to warn users about the addictive nature of their platforms. [The Verge]
Meta and YouTube were both found liable by a California jury for harming a plaintiff's mental health with the design of their products. A massive ruling in a bellwether case that will open the floodgates for other lawsuits
— Ryan Mac 🙃 (@rmac.bsky.social) 2026-03-25T17:27:19.778Z
Meta loses child safety case: A jury has ordered Meta to pay $375 million in civil penalties for violating New Mexico privacy rules and failing to protect children on Facebook and Instagram from online predators. [TechCrunch]
GitHub to train AI on user Copilot data: GitHub will use its users' Copilot interactions and data to train its own AI models unless users specifically opt out by April 24.
"Because everyone else lowered the bar, we decided to join them" is so on-brand...
— Nathan McNulty (@nathanmcnulty.com) 2026-03-25T22:31:13.000Z
Government, politics, and policy
Russia expands national firewall bandwidth: The Russian government will expand the bandwidth of its national firewall system to 954 Tbps. The new bandwidth will be rolled out by 2030 and will be 2.5 times than what the system can handle today. Russia's national firewall allows the government to censor traffic and stop incoming cyberattacks. [Kommersant]
EU Chat Control fails again: The European Parliament has voted down the Chat Control message scanning regulation again. I've lost count of what number attempt this was. [Politico Europe]
Poland reports spike in cyberattacks: Polish officials said the country experienced 2.5 more cyberattacks last year over the previous year, as Russia intensifies its efforts to intervene in the country's politics. [Associated Press]
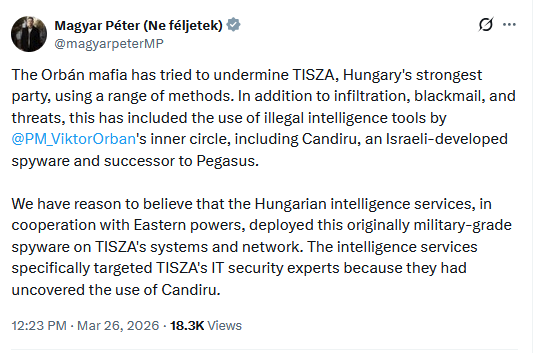
Magyar accuses Orban of using spyware: Hungarian opposition leader Peter Magyar accused Prime Minister Viktor Orban of deploying spyware against the TISZA party. Magyar claims the country's intelligence services used the Candiru spyware against TISZA operations. The TISZA party is expected to win the country's elections next month with a super-majority and ouster Orban's party from the government for the first time in two decades.
UK calls for security-minded use of AI: The CEO of the UK's cybersecurity agency has called on the cybersecurity industry to show an open mind to the current vibe coding trend. Speaking at the RSA conference, Dr. Richard Horne urged industry experts to adopt genAI tools and use them to write more secure software. The NCSC exec urged the industry to get ahead of the trend and make sure AI tools produce secure code rather than spend decades trying to fix the same bugs all over again. [The Record]
UK sanctions scam center marketplace: The UK government has imposed sanctions on Xinbi, a Chinese online marketplace used by large scam operations. The platform sold personal data that scammers used to target victims. It also sold satellite internet equipment that allowed scam compounds to stay online after authorities cut their fiber connections.
Greece looks at amending penal code: The Greek government has proposed changes to the country's penal code. The new changes will allow some convicted individuals to convert prison sentences into charity work or financial penalties. Local media is reporting on the changes as an escape door created for Intellexa CEO Tal Dillian. Dillian threatened to spill the beans on the government's use of the Predator software after he was sentenced to 126 years in prison, eight of which he'll be forced to execute, barring a successful appeal. [Dnews] [h/t Vas Panagiotopoulos]
HK police can demand passwords under national security law: Hong Kong police can demand phone or computer passwords from suspects accused of national security investigations. Suspects who refuse can face up to a year in prison and a large fine. Those who lie or provide misleading information could be locked up for three years. The new punishment was included in an update to the city's National Security Law last week. [The Guardian]
India orders national CCTV audit: The Indian government has ordered a national audit of CCTV systems. Local law enforcement will have to physically check cameras at their locations and ensure the networks use adequate access controls. The order comes after Indian authorities busted a Pakistani spy ring that hacked CCTV systems in India and even deployed their own rogue cameras at sensitive locations. [News18]
FCC changes numbering rules: The FCC is updating the rules to obtain American phone numbers in an attempt to crack down on some robo-calling operations.
Murica losing the cyberz: Speaking at the RSA security conference, four former high-ranking NSA officials warned that the US is losing its advantage in cyberspace as the government is failing to keep up with foreign adversaries. The four cited "brain drain" across the public sector and disintegrating relations with the private sector. [CyberScoop]
CISA barred 10 years from pressuring tech platforms: CISA and two other US government agencies have been barred from pressuring social media platforms to remove or suppress content for ten years. CISA, the Surgeon General's office, and the Centers for Disease Control and Prevention are barred from threatening tech platforms with fines or other punishment if they don't follow the agencies' request. The three are still allowed to forward reports of malicious or fake content but platforms will be the ones to decide if they act. [Reuters]
Ah peak stupidity. A bunch of grifters who were moderated on social media sued the Biden admin claiming "censorship." Bounced around stupid courts w/SCOTUS finally saying "um, no evidence of gov't censorship." Some of the plaintiffs now work in the admin. Either way the lawsuit has now "settled."
— Mike Masnick (@masnick.com) 2026-03-24T20:21:27.541Z
Sponsor section
In this Risky Business sponsor interview, Casey Ellis chats to Fletcher Heisler, founder and CEO of open source identity provider, Authentik. They chat about Extended Identity Access Management (XIAM), the company’s new acronym that has been seven years in the making.
Arrests, cybercrime, and threat intel
RedLine developer extradited to US: US authorities have extradited one of the developers of the RedLine infostealer. Hambardzum Minasyan, of Armenia, was arraigned in a US court this week. He is accused of working with a larger team to develop RedLine and offer it through a Malware-as-a-Service platform. Authorities disrupted the RedLine infostealer in late 2024.
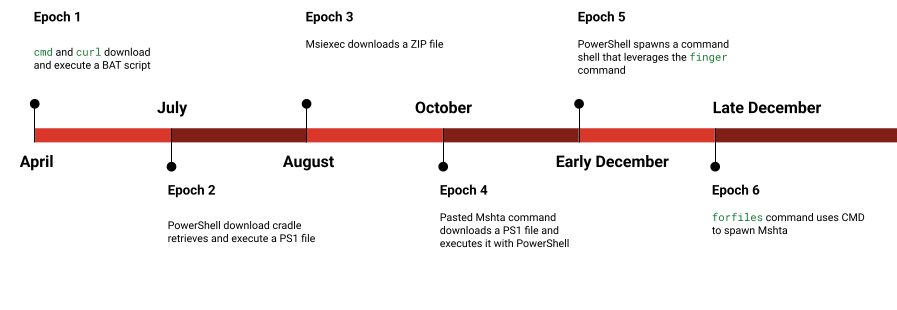
TA551 botnet operator sentenced to prison: A Russian national was sentenced to two years in prison for running a malware botnet. Ilya Angelov used phishing to infect PCs with malware and then sold access to the systems. His botnet has been active since 2017 and his activity has been tracked under codenames such as TA551, Gold Cabin, and Monster Libra. His botnet used malware such as Valak, Ursnif, Qakbot, and IcedID.
Russia arrests LeakBase admin: Russian authorities have arrested the administrator of the LeakBase hacking forum. The site was seized by US and EU law enforcement agencies at the start of the month. The suspect was detained in the Black Sea port of Taganrog. Threat intel firm KELA linked the LeakBase admin to a Taganrog resident a day after the site was seized. [TASS]
Leak Bazaar launched: A known threat actor has launched Leak Bazaar, a new platform for selling data that ransomware groups haven't been able to ransom.
Bubble AI abuse: Threat actors are abusing the Bubble AI website builder to host phishing site resources and avoid email security tools.
Hong Kong badness: GreyNoise says that half of the misbehaving IPs that were scanning the internet last week originated from several Hong Kong organizations.
Middle East phishing surge: Bitdefender has spotted a surge in phishing and malware campaigns targeting the Middle East after the US attack on Iran.
Keitaro: Confiant and Infoblox have published joint research on Keitaro, an advertising performance tracker used by marketers and cyber criminals to route and measure traffic.
Bearlyfy deploys custom ransomware: A pro-Ukrainian hacking group has hit more than 70 Russian companies with ransomware over the past year. The group has been active since January of last year and is tracked as Bearlyfy. While it initially used leaked ransomware strains, Bearlyfy has now developed its custom strain named GenieLocker. It was also seen working with other pro-Ukrainian hacking groups.
New Mora_001 hacks: Fortgale researchers look at a recent campaign that targeted Fortinet devices. They tied the campaign to Mora_001, a well-established ransomware affiliate to various RaaS platforms.
Cl0p member profiles: Ryan Moran has published profiles on members of the Cl0p (former ransomware) data extortion gang. This includes j0nny, AELS, Baddie, Rastafareye, and orlylyly.
TikTok AitM phishing: Sublime Security has spotted a wave of AITM phishing pages designed to target and hijack TikTok business accounts.
PAN warns of fake PAN recruiters: Security firm Palo Alto Networks says a threat actor is impersonating its recruiters in a phishing campaign.
Fraudsters target Russian kids: Russian security firm F6 has spotted a new trend in Russia where online fraud and scam groups are targeting children, social-engineering them into taking photos of their parents' e-banking apps and verification codes under threats or in exchange for in-game currencies.
Malicious Chrome extension: The DomainTools security team looks at a malicious Chrome extension that posed as an ad-blocker specialized in blocking ChatGPT's new ads, but actually stole its users' ChatGPT prompts.
Ivanti EPMM hacks IR: WithSecure has published details from its incident response work for companies hacked with two recent Ivanti EPMM zero-days (CVE-2026-1281 and CVE-2026-1340).
GitHub phishing campaign: A massive spam campaign is targeting GitHub users. A threat actor has opened more than 2,000 GitHub discussions about fake Visual Studio Code security alerts. The attacker is tagging thousands of users in an attempt to trick them into installing a malicious update. The posts are easy to spot because they use non-existent CVEs. [Socket Security]
Looks like there's a GitHub phishing issue/email going around for VS Code users. Be very wary and don't click on any links. As per a comment I've found: This is an ongoing attack on GitHub users, see: ParrotCanyon/CriticalPatch-99571#1
— Richard Bown (@bownie.bsky.social) 2026-03-25T19:53:41.115Z
ClickFix campaigns: Recorded Future has some details on five separate threat actor clusters engaging in ClickFix campaigns, the new scourge of the online and malware ecosystem.
Scarlet Goldfinch profile: Red Canary has published a profile on Scarlet Goldfinch, a threat actor that moved last year from running fake browser update pages to ClickFix (what else!!?!?!).
Malware technical reports
VoidLink: Elastic's security team has come across "a data dump containing source code, compiled binaries, and deployment scripts for the kernel rootkit components of VoidLink, a cloud-native Linux malware framework first documented by Check Point Research in January 2026."
Kamasers botnet: ANY.RUN spotted a new DDoS botnet spreading in the wild and named Kamasers. Interestingly, this one targets Windows PCs and also includes the ability to deploy other payloads.
"Kamasers is a sophisticated DDoS botnet that supports both application-layer and transport-layer attacks, including HTTP, TLS, UDP, TCP, and GraphQL-based flooding. The malware can also act as a loader, downloading and executing additional payloads, which raises the risk of further compromise, data theft, and ransomware deployment."
Interlock ransomware: Kirk from Derp.ca has published a teardown of the Interlock ransomware
BRUSHWORM and BRUSHLOGGER: Elastic's security team looks at BRUSHWORM and BRUSHLOGGER, two new pieces of malware found on the network of a South Asian financial institution.
"Despite their low sophistication and multiple implementation flaws, these two binaries deliver a functional collection platform that combines modular payload loading, USB worm propagation, broad file theft with air-gap bridging, and persistent keystroke capture via DLL side-loading. The iterative testing versions and active C2 infrastructure suggest an actor still refining their toolset."
Infiniti Stealer: Malwarebytes has spotted a new macOS infostealer named Infiniti Stealer. Obviously, like all the cool malware these days, it's being delivered via ClickFix.
PXA Stealer: Cyberproof researchers have published a report on a campaign spreading PXA Stealer, an infostealer first spotted in August last year.
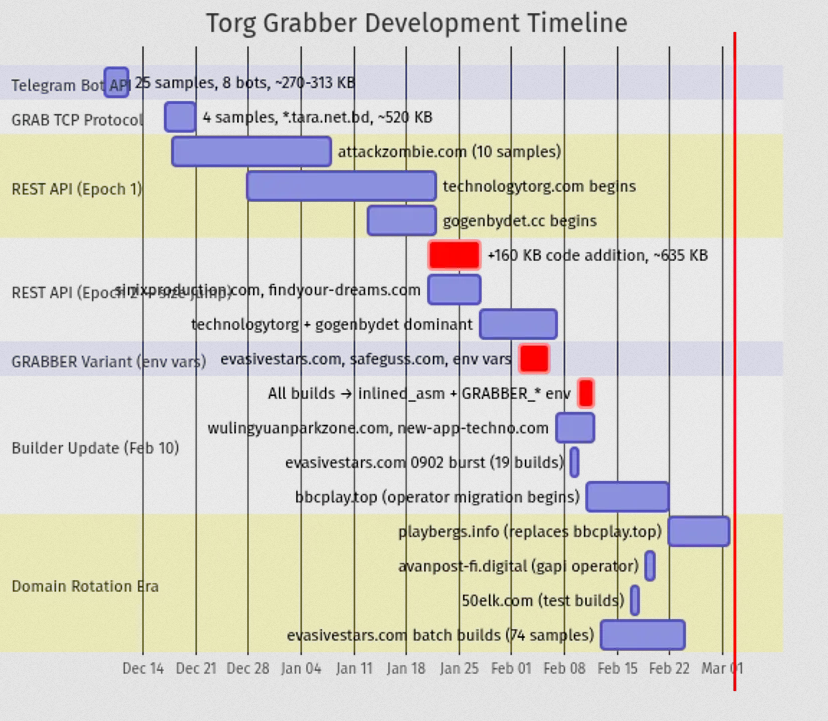
Torg Grabber: Gen Digital looks at the newest infostealer on the market, going by Torg Grabber. Development on the tool started in mid-December before it was spotted in the wild this month.
Sponsor section
Authentik is an open-source identity provider that is also offered with paid enterprise features. In this demo, CEO Fletcher Heisler and CTO Jens Langhammer walk Risky Business host Patrick Gray through an overview and a demo of the technology.
APTs, cyber-espionage, and info-ops
Red Menshen deploys BPFdoor: A Chinese APT group has deployed new and more advanced versions of the BPFdoor malware on the backbone of telecom operators. The attacks have been linked to a group tracked as Red Menshen. The new BPFdoor variants are far more complex than the initial backdoors found in 2021. Rapid7 says they act as a multi-layered access framework designed to bypass multiple security defenses. The company called the new versions as some of the most advanced malware its team has ever seen.

Coruna tied to Operation Triangulation: A Kaspersky analysis has linked the Triangulation hacking campaign to the Coruna iOS exploit chain. Code similarities have been found between the Triangulation iOS kernel exploits and other components of the Coruna framework. Triangulation attacks also employed two zero-days from Coruna's arsenal.
Contagious Interview: eSentire looks at a suspected Contagious Interview campaign spreading EtherRAT via a ClickFix page.
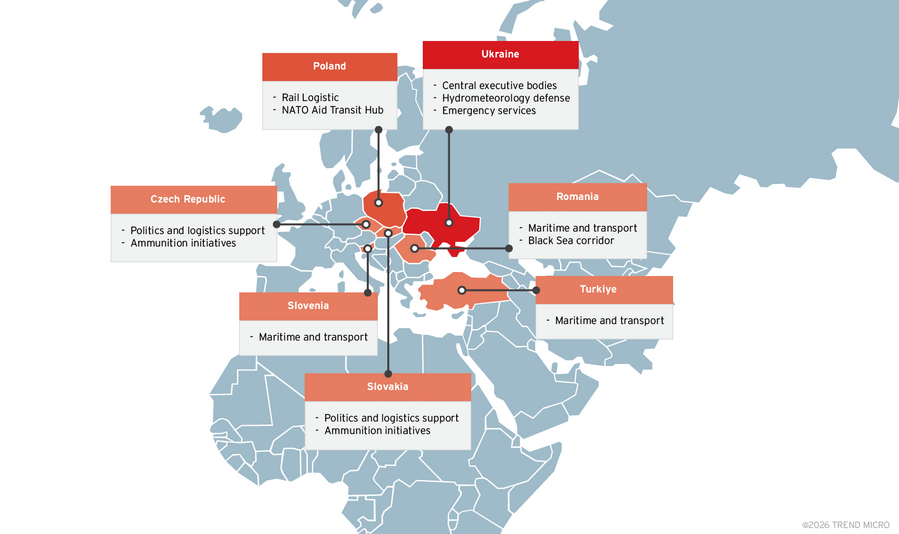
Pawn Storm: Trend Micro has published a report on a Pawn Storm (APT28) campaign that targeted the defense supply chain of Ukraine and governments of Eastern European countries such as the Czech Republic, Poland, Romania, Slovakia, Slovenia, and Turkey. The campaign used a new malware framework the company calls PRISMEX.
Vulnerabilities, security research, and bug bounty
Apple security updates: Apple has released a bunch of security updates on Tuesday for the iOS and macOS 26.4 rollout. No zero-days mentioned.
TP–Link security updates: TP-Link has released several security updates over the past week, including patches for serious bug fixes like hardcoded encryption keys and command injections.
Cisco semiannual security updates: Cisco has released its semiannual security update for Cisco IOS and IOS XE products. This one fixes 12 vulnerabilities. OPSWAT has a technical write-up of one of them.
"In direct response to customer feedback, Cisco releases bundles of Cisco IOS and IOS XE Software Security Advisories on the fourth Wednesday of the month in March and September of each calendar year."
ClawHub vulnerability: Silverfort researchers have found a vulnerability in the ClawHub portal that could have allowed threat actors to propel their malicious skills to the #1 spot in the popularity rankings.
Infosec industry
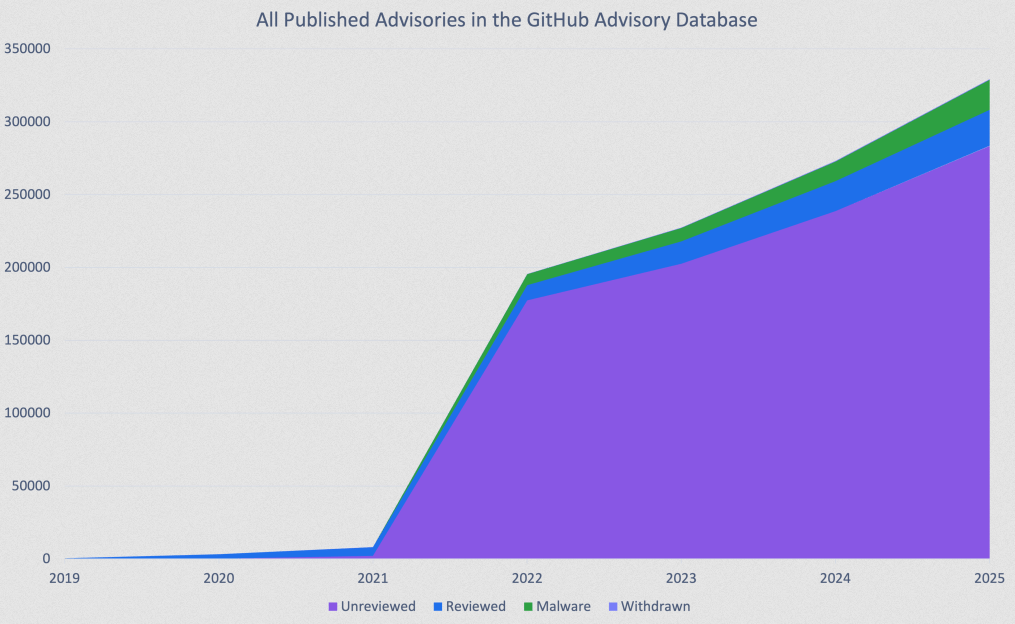
Threat/trend reports: Gcore, GitHub, Kaspersky, Keepit, and NCC Group have recently published reports and summaries covering various threats and infosec industry trends.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about FBI Director Kash Patel admitting to Congress that the Bureau is buying American's location data and using it to generate valuable intelligence. That's concerning, because commercially available information can be used in tremendously invasive ways and the FBI can buy it without needing a warrant.
We recently also launched a new podcast series called Risky Business Features. In this episode, James Wilson and Brad Arkin discuss the attack that devastated medtech company Stryker. It turns out the attackers used Microsoft's Intune to wipe the company’s devices, but what else could they have weaponised?
