Risky Bulletin Newsletter
April 15, 2026
Risky Bulletin: Malicious LLM proxy routers found in the wild
Written by

News Editor
This newsletter is brought to you by Corelight. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.
A recently published academic paper has studied the emerging ecosystem of LLM routers, a type of proxy that sits between AI agents and the AI provider to help with load-balancing and cost tracking and limiting.
The research team tested 28 paid routers available on marketplaces like Taobao, Xianyu, and on Shopify-hosted storefronts, as well as 400 free routers available on GitHub and other places.
The study searched for multiple suspicious behaviors, such as modifying the response to inject commands, using a delay/trigger mechanism to hide future bad commands behind a history of clean operations, accessing credentials that pass through them, and using evasion techniques to thwart analysts.
In total, researchers found 28 malicious routers. Nine injected malicious commands into a service response to the user, two routers used delay triggers, and 17 routers accessed AWS account canaries.
One LLM router went as far as to empty ETH out of a private wallet, a clear sign it was up to no good.
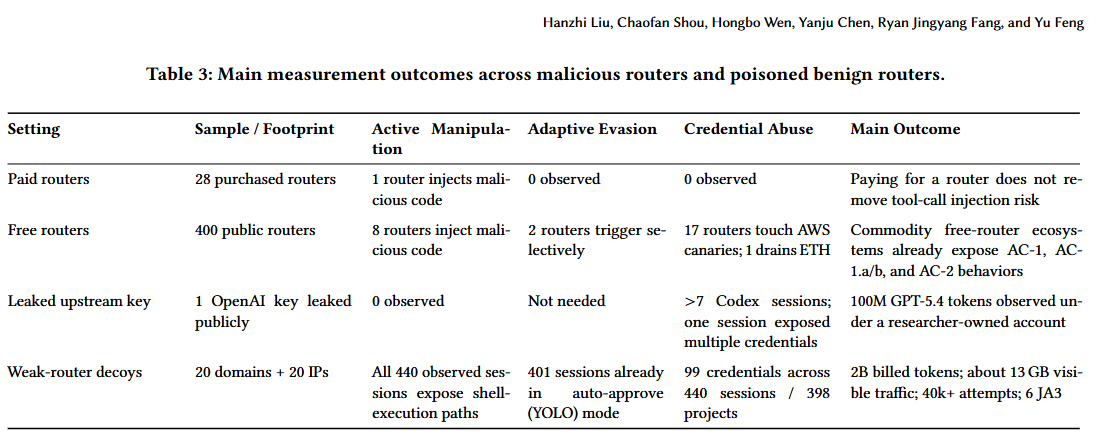
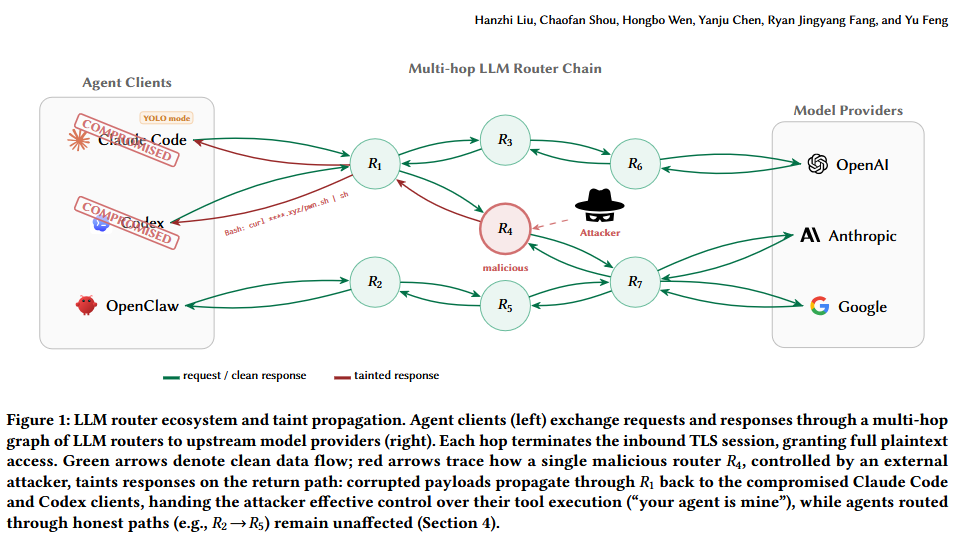
But this was only half of the study. Because these routers act like a giant mesh of proxy nodes in front of a company network, the communications between the agent and the AI provider don't go only through one node and will sometimes bounce around, depending on each node's load.
One compromised router can make other routers relay malicious commands on its behalf and have a path to a company's entire fleet of AI agents.
One weak node can ruin a company's entire LLM cost-control system and expose its entire staff to malware, credential theft, and data exfiltration.
To test this, the research team leaked an OpenAI API key on Chinese forums, WeChat, and Telegram groups, and also deployed 20 vulnerable proxies.
They later observed more than 400 sessions into their LLM proxy mesh, with one node acting as an initial point of compromise, capable of reaching anywhere in the AI chain.
Risky Business Podcasts
In this special documentary episode, Patrick Gray and Amberleigh Jack take a look back at hacking throughout the 1990s, from the feel-good vibes of the early hacking communities to the antics of young hackers who wound up on the run from the FBI.
Breaches, hacks, and security incidents
Booking.com discloses data breach: Booking.com notified customers last week of a security breach that exposed their personal data. Booking details, names, emails, home addresses, and phone numbers were exposed. The company said no financial data was exposed. It also reset PIN numbers for the affected customers' reservations. [ABC]
Hallmark leak impacts 1.7m: Hackers have leaked the personal information of 1.7 million of Hallmark customers. The ShinyHunters group leaked the company's data last week after Hallmark refused to pay a ransom. The data was stolen from the company's Salesforce accounts in a hacking wave last year.
NYK reports breach of fuel system: Hackers have accessed the marine fuel procurement system of Japanese shipping company NYK. The incident took place at the end of March and NYK had to stop using the platform. The company said some employee data was accessed and likely stolen. NYK is part of the Ocean Network Express, the sixth largest container shipping company in the world. [Ship&Bunker]
The Big Three all hacked: Security firm CodeWall used its own AI tool to hack the AI platforms of the Big Three, a term used to refer to the top three management consulting firms—McKinsey, the Boston Consulting Group, and Bain. The latest hack, of Bain's Pyxis platform, allegedly took just 18 minutes.
Fake Ledger iOS app steals $9.5m from users: A malicious Ledger crypto-wallet that managed to sneak onto the official Mac App Store has stolen almost $10 million from more 50 victims worldwide. The stolen funds were immediately laundered through KuCoin and an underground mixing service called AudiA6. The app was live on the store for almost two weeks. One of the campaign's victims is American singer Garrett Dutton. The artist lost 5.9 Bitcoin, an estimated $440,000, which he had saved through the past decade as his retirement fund. [ZachXBT // The Street]
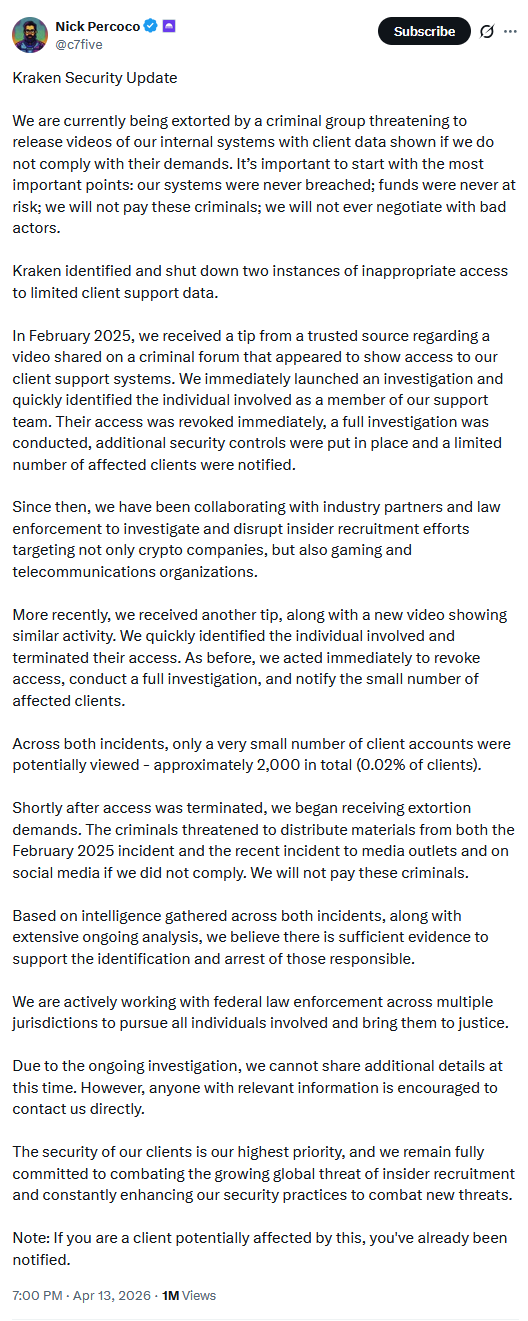
Kraken denies hack after failed extortions: Cryptocurrency exchange Kraken won't pay a ransom demand related to two malicious insider breaches. Kraken CSO Nick Percoco said a criminal group tried to extort the company last week using two videos shot by former employees. The videos allegedly depicted customer details stored in the company's backend. Kraken says it fired the employees and notified affected users and law enforcement.
General tech and privacy
Linux 7.0 is out: The Linux project has released version 7.0 of the Linux kernel. On the security side, this release adds support for ML-DSA.
OpenSSL 4.0 is out: The highly anticipated version 4.0 release of OpenSSL is out, with the biggest change being support for post-quantum encryption attacks protection.
Google cracks down on Back button hijacking: Google will downrank and classify as spam websites that hijack the Back button behavior. The technique has been abused for more than a decade to redirect users to ads or unrelated websites instead of the page users were previously on. Google is urging website owners to investigate their sites for this unwanted behavior, since many times it may originate from a third-party library they are not aware of. Enforcement of the new rule and website downranking will begin on June 15.
Genuinely the best thing out of Google in 5+ years
— Sean Hodgdon (@seanhodgdon.com) 2026-04-14T10:21:18.750Z
Government, politics, and policy
EU cracks down on Chinese solar inverters: The EU will stop financing projects that use Chinese-made solar inverters. The EU agreed on the new rules at a high-level meeting this week. Officials cited threats to the bloc's energy security. Chinese companies control more than half of the EU's installed solar capacity. [SCMP]
At a top level meeting of her 26 department chiefs in March, European Commission President Ursula von der Leyen quietly approved a plan to stop EU funds from going to clean technology projects containing Chinese inverters.
— Finbarr Bermingham (@fbermingham.bsky.social) 2026-04-14T10:04:44.000Z
Russia blocks BlueSky: Social media network BlueSky has been added to Russia's internet blocklist. Most of the social media networks are already banned in Russia, such as Facebook and Twitter. Most major western online platforms have been blocked in Russia. Most users are now flocking to Korean, Chinese, or Japanese platforms, looking for safe spaces without surveillance online. [The Record]
New US Cyber Trust Mark auditor: The FCC has picked a new organization to run a Biden-era program known as the US Cyber Trust Mark. The California-based non-profit the ioXt Alliance will be in charge of testing the security of routers and smart devices that will be sold in the US. Devices that pass will be allowed to put a special logo on their labels to highlight their improved security features. The FCC removed the program's initial administrator, UL Solutions, for alleged "deep ties" with China. [NextGov]
Plankey nomination: With a new DHS Secretary in Senator Markwayne Mullin, US officials hope the Sean Plankey nomination for CISA Director will finally move forward. They hope. [CyberScoop]
The Mythos grand scare of 2026: Banks and regulators across three countries—Canada, the UK, and the US—have held meetings over the past week about the possible dangers posed to their networks by Anthropic's new Mythos AI model. It's a silly meeting to have since the model is private, but they should be meeting on the dangers of AI overall, and not Anthropic in particular. In the meantime, EU financial regulators are all super pouty that they've been left out of talks about the new Mythos mega AI beast. Don't get me wrong, Mythos is very good at what it does, but it's not the world-ender everyone makes it look. The goal is to get all the large companies to pay for access and test their networks. I just really hope people understand that this "our AI is too dangerous to release" is a known tactic for AI companies dating back years. Here's an article from our friend Zack Whittaker back when OpenAI was doing "the thing." Uuuuu, the scary AI is here to get your toes! Run!!!
Sponsor section
In this Risky Business sponsor interview, Corelight’s Senior Director of Product Management, Dave Getman, tells James Wilson how Corelight Agentic Triage helps defenders stay ahead of AI-powered attacks.
Arrests, cybercrime, and threat intel
SMS blaster gang arrested in Kazakhstan: Authorities in Kazakhstan have arrested four suspects for using an SMS blaster device to send SMS spam messages. The device was installed on a car and drove around populated areas. It had a range of 300 meters and could send up to 100,000 messages per hour. The group's members are the first cybercriminals to be detained in a former Soviet state for using SMS blaster devices. [CommsRisk]

Restaurant hackers arrested in Moscow: Russian authorities have detained two men who hacked self-service kiosks at Tasty and Point restaurants. The duo designed and plugged a homemade device into the kiosks to access the restaurant's internal network. The suspects allegedly sought to gain access to the restaurant's rewards program and save money on food. A 49-year-old and a 19-year-old have been taken into custody. [Baza]
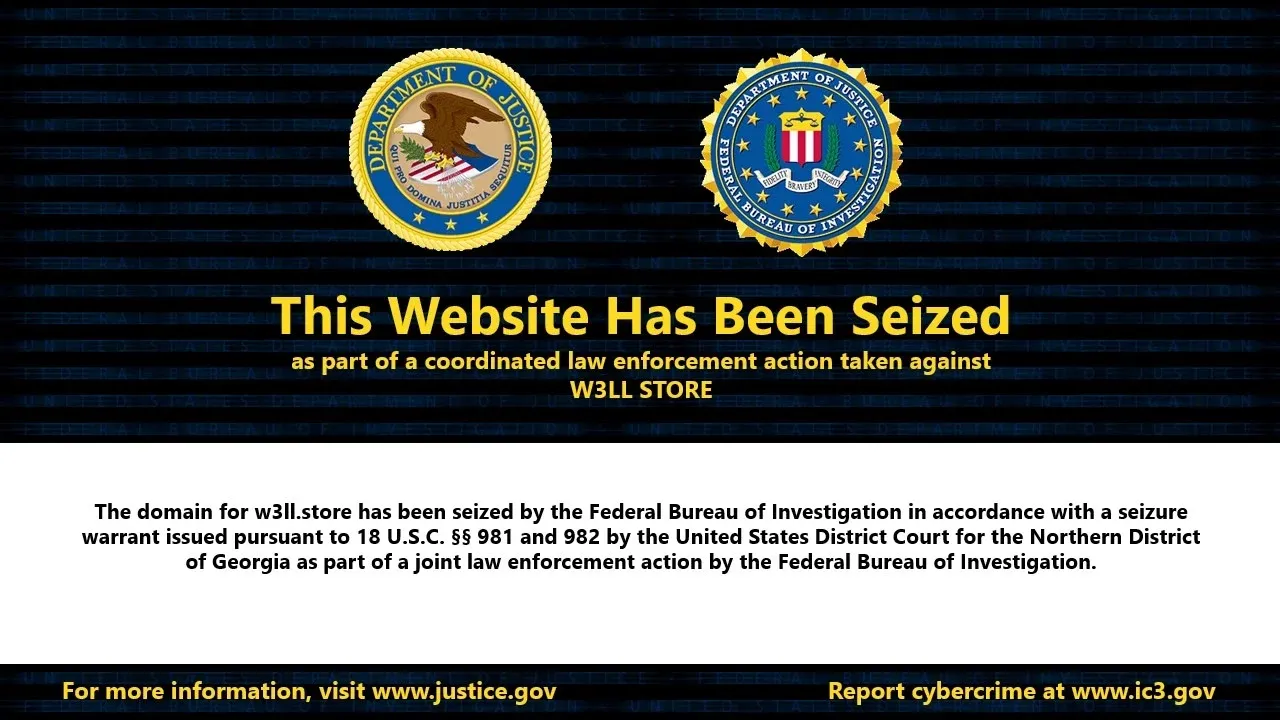
W3LL takedown: US and Indonesian law enforcement have dismantled the W3LL phishing platform. Authorities seized the platform's domains and arrested its developer last week. The platform launched in 2019 and sold access to an advanced phishing kit and stolen credentials.
FUNNULL returns after US sanctions: A Philippines-based CDN operator has returned online with new infrastructure after being sanctioned by the US last year. The company was known for renting IP address blocks from major cloud providers and making them available to cybercrime operations. According to security firm SilentPush, the new FUNNULL servers geofence US visitors to prevent scamming Americans and drawing the ire of US authorities again.
PowerSchool hacker profile: ABC News has published a profile of Matthew D. Lane, the individual who hacked school management platform PowerSchool in 2024. Lane is set to start his prison sentence this month. He traced his fascination and early steps into hacking to the Roblox game community.
Silent group hit almost 40 law firms in a year: The Silent data extortion group has hacked and ransomed almost 40 law firms over the past year. Thirty-eight law firms have now been listed on the group's leak site after refusing to pay ransoms. The group told DataBreaches.net that they attacked almost 80 firms in total, which means half of them have paid. The FBI warned that the group was targeting law firms last May in a private industry alert.
SonicWall recon campaign: There's a massive SonicWall reconnaissance and mapping campaign currently taking place and targeting the company's SMA appliances.
Prestashop exposure: More than 200 Prestashop online stores have left their installation folder exposed online. Attackers can abuse the installer to overwrite configs and hijack the stores or deploy malware. This includes a multi-billion dollar fashion retailer, two French university bookshops, and a pan-European retail chain. [Sansec]
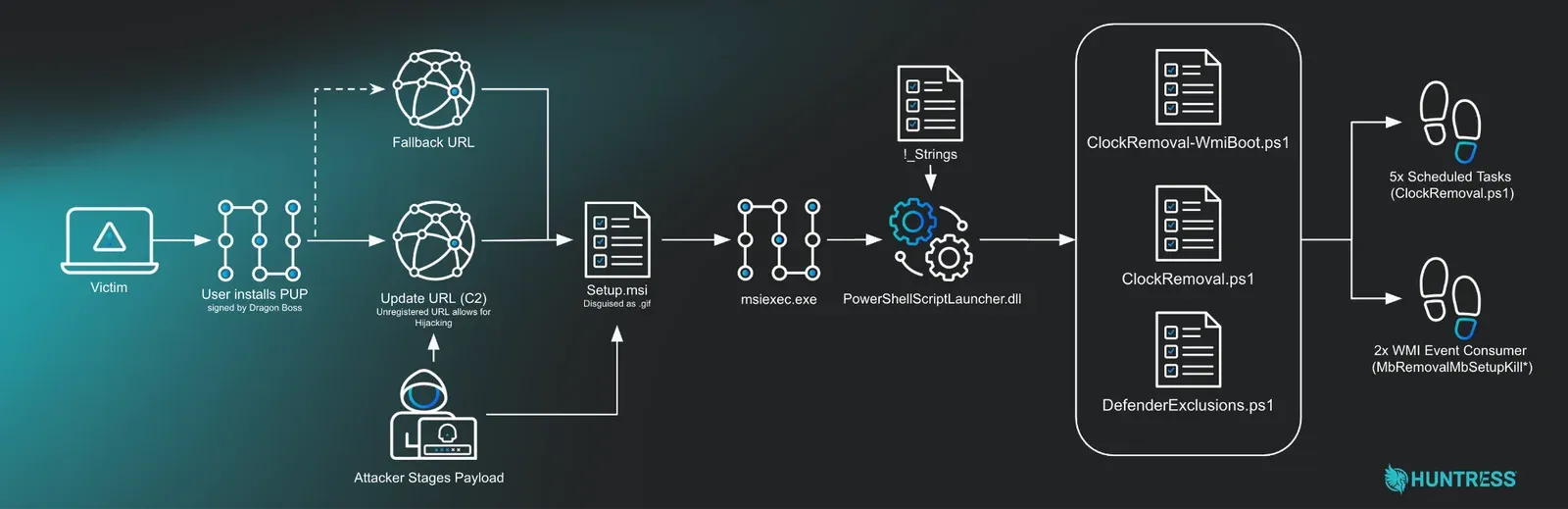
Adware op turns EDR killer: Huntress looks at a peculiar case where a PUP/adware family rolled out a multi-phase update across several days that tried to disable security software on infected hosts.
Cluster of malicious extensions: Socket Security has discovered a cluster of 108 malicious Chrome extensions that steal and send user credentials to the same command-and-control server. The extensions were published through five developer accounts and are still live on the official Chrome Web Store. Some of the extensions can also run malicious code, steal browser histories, and inject ads.
Threat actor backdoors 30+ WP plugins: More than 30 WordPress plugins have been backdoored to turn websites into pools of spam and scammy links. The plugins were developed ten years ago but were sold to a new owner last year. After laying dormant for eight months, they turned evil last week when the new owner deployed a backdoor to all sites where they were installed. The WordPress security team has since moved to remove all plugins running the Essential Plugin branding. [Anchor // TechCrunch]
Stardrop npm campaign: A threat actor has published more than 200 packages on npm claiming to integrate with a new AI coding agent named Stardrop. The libraries are obviously malicious and drop a cloud and AI credential harvester. According to security researchers, the packages appear to target developers at AI companies, luxury brands, and venture capital firms.
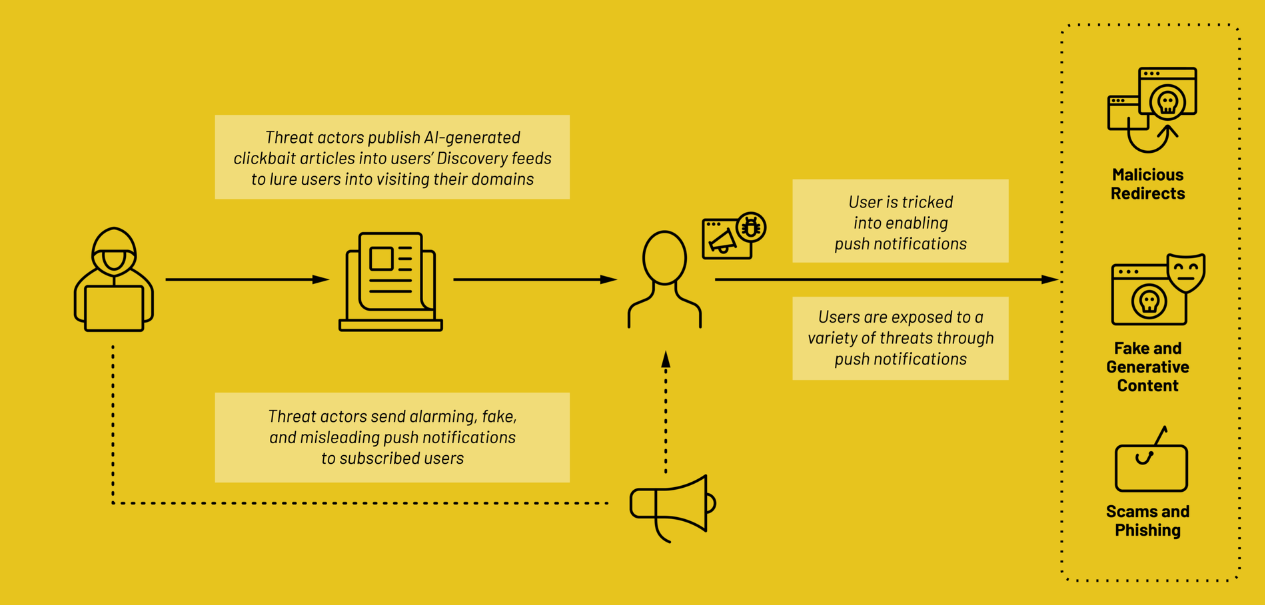
Pushpaganda takedown: Security researchers have found a network of more than 110 domains posing as news sites but involved in a cybercrime scheme. Tracked as Pushpaganda, the network uses AI content, paid ads, and SEO manipulation to promote its sites and trick users into subscribing to push notifications. The group then uses notifications to repeatedly lure users on malicious sites, such as phishing pages and cyber scams.
Malware technical reports
Predator's kernel engine: Jamf's Nir Avraham has published a report looking at how the Predator spyware exploits, interacts, and modifies the iOS kernel for its operations.
"The engine has never been reported on — until now."
JanelaRAT: Kaspersky GReAT published a report on JanelaRAT, a remote access trojan active in the Brazilian market since 2023, itself a variant of the older BX RAT.
PhantomPulse RAT: Threat actors are targeting individuals in the financial and cryptocurrency sectors through elaborate social engineering on LinkedIn and Telegram that deliver the PhantomPulse RAT. This activity has been linked to REF6598.
JitterDropper: OALabs has spotted JitterDropper, a new Rust and MSVC-based Windows dropper under active development since at least last month.
JanaWare ransomware: The Acronis security team has discovered a new ransomware strain named JanaWare being used in attacks targeting Turkish users.
Sponsor section
James Pope, Corelight's Director of Technical Marketing Engineering, demonstrates the company's Open NDR Platform and how it combines network detections with a whole host of other data sources.
APTs, cyber-espionage, and info-ops
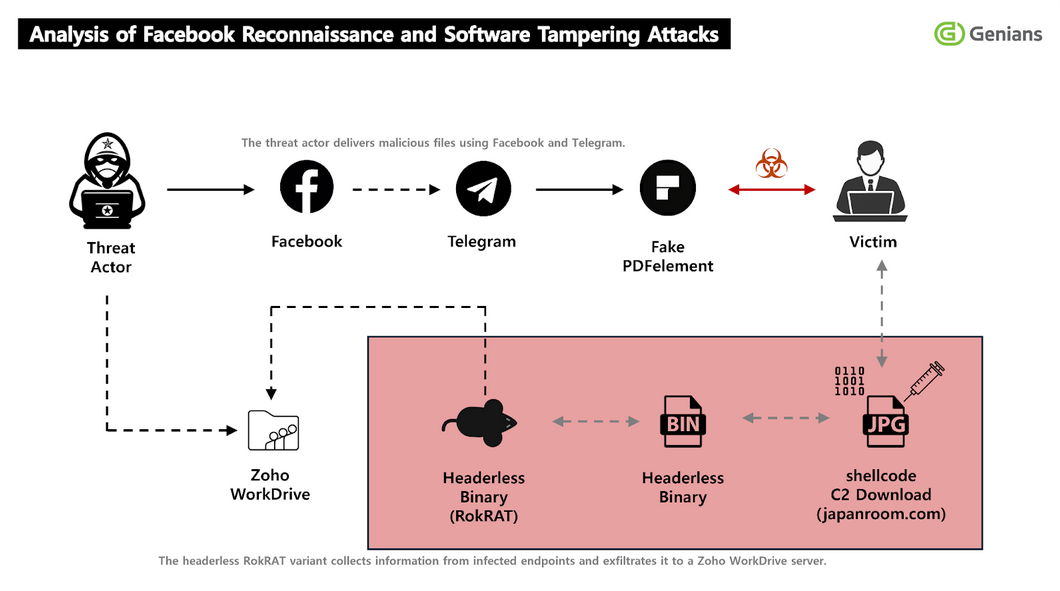
APT37: South Korean security firm Genians has a report out on an APT37 campaign that is targeting victims via Facebook social engineering campaigns.
Vulnerabilities, security research, and bug bounty
KEV update: CISA has updated its KEV database (twice) with nine vulnerabilities that are currently exploited in the wild. This includes six Microsoft bugs, two from Adobe, and one from Fortinet. The holy trifecta of in-the-wild exploitation of this century.
wolfSSL fixes bug allowing forged identities: The wolfSSL library has patched a bug that could have allowed attackers to trick servers or apps to accept forged certificates. Tracked as CVE-2026-5194, the bug resides in wolfSSL's component that verifies ECDSA certificates. The bug was discovered by Nicholas Carlini of Anthropic.
ShowDoc RCE enters exploitation phase: Threat actors are abusing a vulnerability in document management and collaboration platform ShowDoc. Attacks are exploiting CVE-2025-0520, a bug disclosed last year that allows hackers to upload malicious files anywhere on the platform. Placing PHP files in the platform's core folders can allow attackers to run their own code. ShowDoc patched the issue in April last year. The platform is popular among Chinese companies.
Patch Tuesday: Yesterday was the April 2026 Patch Tuesday. We had security updates from Adobe, Microsoft, IBM, SAP, Fortinet, Ivanti, AMD, Supermicro, Joomla, Moxa, ABB, Schneider Electric, and Siemens. Other projects and companies like Android, Apple, Cisco, Dell, HPE, Juniper, D-Link, Axis, TP-Link, Chrome, Firefox, Samsung, Qualcomm, AWS, NVIDIA, Synology, WatchGuard, Palo Alto Networks, Kubernetes, Apache ActiveMQ, OpenSSL, OpenSSH, and Drupal released security updates earlier this month.
Microsoft Patch Tuesday: This month, Microsoft patched 167 vulnerabilities. One of the patches addressed an actively exploited zero-day in Microsoft's SharePoint server (CVE-2026-32201).
Infosec industry
Threat/trend reports: The Corporate Governance Institute, Emsisoft, IANS, Kaseya, Lightrun, Ox Security, SumSub, ThreatMon, and WBA have recently published reports and summaries covering various threats and infosec industry trends.
NDSS 2026 videos: Talks from the Network and Distributed System Security (NDSS) Symposium 2026, which took place at the end of February, are available on YouTube.
JSAC 2026 videos: Talks from Japan CERT's JSAC 2026 security conference, which took place in January, are available on YouTube.
Risky Business podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq discuss how the rise of AI, which is very good at vulnerability and exploit development, will change the cyber security industry and competition between states.
In this episode of Risky Business Features, James Wilson chats to professional hacker Jamieson O’Reilly about Anthropic’s Mythos and the impact it could have on offensive security. Jamieson is CEO of DVULN and co-founder of Aether AI.
