Risky Bulletin Newsletter
April 29, 2026
Risky Bulletin: UK NCSC blasts SOC metrics
Written by

News Editor
This newsletter is brought to you by runZero, the Total Attack Surface & Exposure Management platform. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.

The UK's cybersecurity agency has advised public and private organizations against relying too much on bad metrics to evaluate the efficiency of their security operations centers (SOCs).
Officials say bad metrics incentivize SOC teams to be careless about their jobs and rush through tickets and detections rather than be dedicated to protecting their networks.
While metrics can be used for other IT departments to evaluate their effectiveness, the true value of a SOC team comes from insight and not speed or quantity, hence SOC teams should not be treated as any other department that needs to be optimized.
The agency listed four common metrics that have been known to cause major issues:
- Number of tickets processed
- Time taken to close a ticket
- Number of detection rules written
- Volume of logs collected
Dave Chismon, CTO for Architecture at the UK NCSC, warns that prioritizing any metric related to tickets will only result in SOC team members hurrying to close that ticket with minimal investigations. Since most SOC alerts/tickets are usually false positives, this is bound to create automated mental responses where security staff associate alerts with a waste of their time rather than a source of a security breach.
Focusing on the number of logs also pushes SOC teams to mass-produce detections that are likely to cause the very same false positive SOC alerts.
Focusing on the volume of collected logs should never be prioritized over just collecting a few and well enriched logs from systems likely to be (ab)used by attackers.
"Unfortunately, many of the most common SOC metrics provide no insight to seniors about the effectiveness of the SOC," Chismon said. "The NCSC have seen SOCs with great potential rendered entirely ineffective through poor choice and application of metrics."
The NCSC says that using no SOC metrics is far better than relying on bad ones.
If organizations have to use metrics, Chismon recommended relying on time-to-detect (TDD) and time-to-respond (TRR), which are far superior and incentivize thorough and thoughtful investigations.
The NCSC official has also advised allowing SOC teams to follow their instincts. This includes allowing SOCs to perform hypothesis-led threat hunting, where they investigate their network based on theories and hypotheses of how an attack could occur.
SOC teams should also be allowed to study threat actors and techniques, rather than be terrorized about their metrics, as this would allow them to prepare and defend their networks for the most common techniques used at a particular time.
Risky Business Podcasts
In this episode of Risky Business Features, Anthropic’s Nicholas Carlini joins Patrick Gray and James Wilson to talk about advancements in AI-driven vulnerability research and exploit development.
https://risky.biz/RBFEATURES16/
Breaches, hacks, and security incidents
China's surveillance system left exposed online: Chinese companies that support the government's sprawling surveillance network have left backend dashboards exposed online, effectively revealing the true depth of how much the Chinese government tracks its own citizens. [NetAskari]
Gonets breach: Ukraine's cyber units have allegedly breached Gonets, a Russian low-orbit satellite communications platform and the country's Starlink alternative. Hackers allegedly stole highly classified internal documents over a three-year intelligence operation. They also compromised at least two high-profile figures in the Gonets leadership to intercept private communications. Ukraine's 256th Cyber Assault Division took credit for the intrusion. [United24] [h/t Alex Rudolph]
Vimeo is getting extorted: The ShinyHunters hacking group is threatening to leak data stolen from video hosting platform Vimeo unless they pay a ransom demand. The group stole data from the company's Snowflake cloud storage after first hacking cloud-cost monitoring tool Anodot. ShinyHunters breached Anodot earlier this month and has been engaged in a slow and methodical campaign to extort its customers. Previous victims also included GTA maker Rockstar Games, fashion retailer Zara, and payments provider Payoneer. [Vimeo blog]
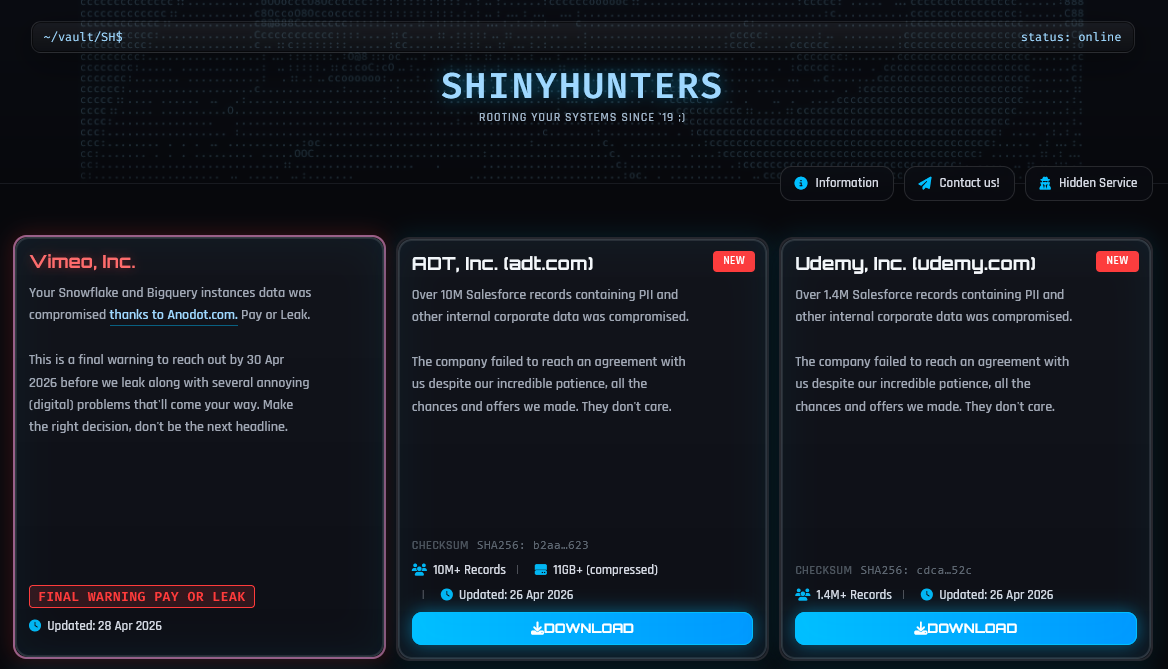
AFC leak: Hackers have leaked data stolen from the Asian Football Confederation (AFC). The data allegedly includes the personal details of every player and coach working for Asian football clubs. The leak includes player contracts, verified email addresses, and even passport scans. The leakers claim they obtained the data from the ShinyHunters hacking group. [DataMinr]
Handala leaks US Marines data: An Iranian hacking group has leaked the personal details of almost 2,400 US Marines stationed in the Persian Gulf region. The leaked data includes details about families, home addresses, their bases, and shopping habits. It's unclear from where the data was taken. [Metro]
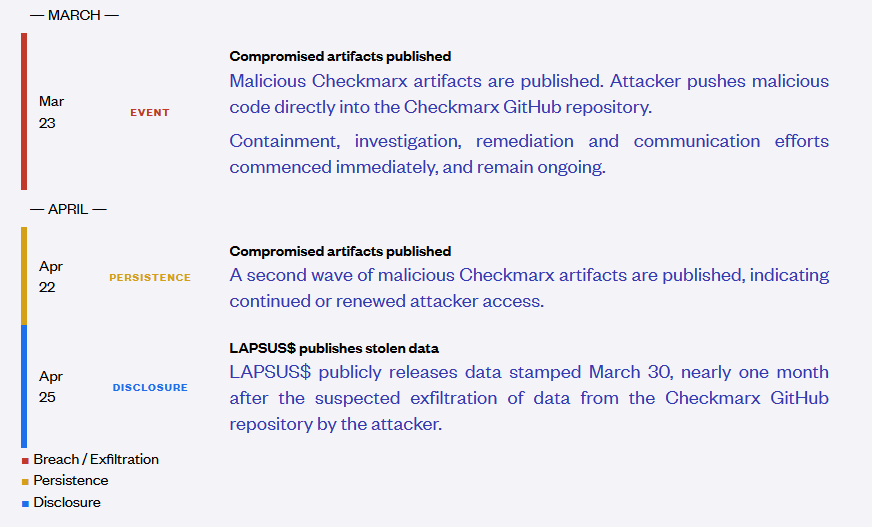
Checkmarx incident blamed on Lapsus$: The Lapsus$ cybercrime group was behind the supply chain attack against security firm Checkmarx and its KICS vulnerability scanner. The group breached the company's GitHub account and published malicious payloads in March and again last week. The malicious payloads allowed Lapsus$ to steal credentials and hack other organizations that used KICS to scan their internal networks. The group also leaked some of Checkmarx's data online over the weekend. [Checkmarx]
General tech and privacy
Mystery outage takes out tens of piracy sites: Tens of pirate streaming sites have gone dark this week after their shared backend, a suspected Piracy-as-a-Service provider, went down under mysterious circumstances. [TorrentFreak]
Geofence warrants at the USSC: The US Supreme Court is hearing a case this week on the legality of geofence warrants and their legality against the Fourth Amendment. The court appears to be split, but no decision yet, or at least by the time I filed this newsletter. [SCOTUSblog]
Apple Music is drowning in AI slop: A third of all Apple Music content is AI slop songs that nobody's listening to, accounting for only 0.5% of all track plays. [AppleInsider]
Exchange Online deprecations: Microsoft will deprecate TLS 1.0 and 1.1 for POP3 and IMAP4 connections to Exchange Online in July.
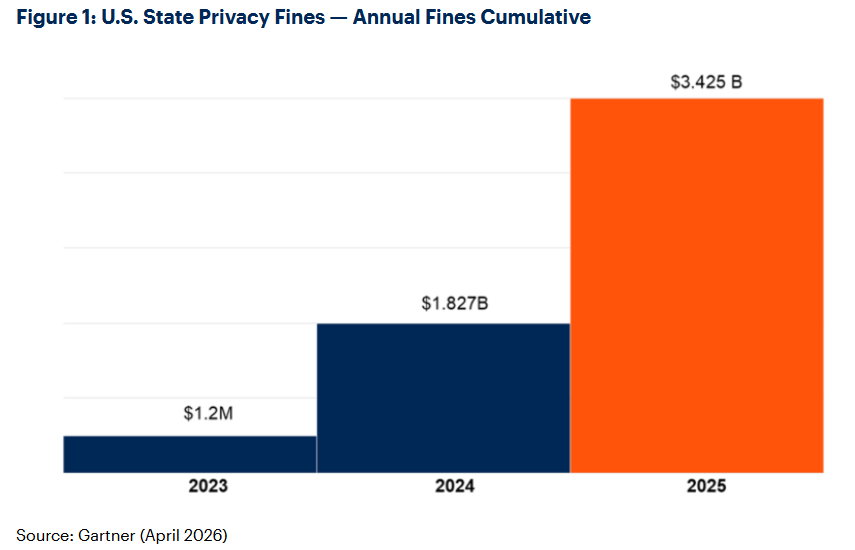
US privacy fines go over $3.4b: American companies were fined more than $3.4 billion last year for privacy-related infractions. The total fines are larger than the last five years combined. According to Gartner, the increased fines have been driven by the wide adoption of insecure AI technologies and new state privacy laws. [CyberScoop]
Government, politics, and policy
Japan sets up Mythos task force: The Japanese government will stand up a special cybersecurity task force to assess the potential dangers posed to its infrastructure by Anthropic's new Mythos LLM. [Japan Today]
South Africa withdraws AI-hallucinated AI rules: The South African government has withdrawn its national AI policy after researchers found fabricated sources in its reference list. All evidence suggests the government had used AI to draft its new AI policy. Several politicians have called the incident a "national embarrassment" and the government promised to investigate. [IOL]
South Korea claims political pressure on Coupang investigation: South Korea has accused the US of meddling and political pressure over its investigation of a data breach of e-commerce giant Coupang. More than 90 South Korean lawmakers will deliver a signed formal complaint to the US ambassador this week. Coupang suffered a major data breach last year when it exposed the personal data of a third of South Korea's population. Several members of the US House of Representatives have accused the South Korean government of targeting Coupang because of its American ownership. They did not present any evidence to support their claims. [Bloomberg]
Greek government to ban: The Greek government plans to ban anonymity on social media networks. Officials cited the rising levels of toxicity in online comments, coordinated harassment, fake news, and political manipulation. Greece is set to hold national elections next year. [Euractiv]
Tennessee bans crypto-ATMs over scams: The US state of Tennessee has banned cryptocurrency ATM kiosks over an increase in scam incidents. Tennessee is the second US state to ban cryptocurrency ATMs. Indiana also outlawed the technology last month. Cybercriminals have been tricking victims into buying crypto at an ATM as a way to bypass banking anti-fraud detections. [The Record]
NSA head warns of upcoming election disinfo: The new CyberCom and NSA lead, Army Gen. Joshua Rudd, has warned Congress this week that foreign adversaries are expected to interfere in this fall's midterm elections. [The Record]
Locked Shields 2026 concludes: Forty-one countries had participated in NATO's yearly cyber defense exercise Locked Shields. The joint Latvia and Singapore team scored the most points.
Sponsor section
In this Risky Business sponsor interview, Casey Ellis chats to RunZero’s founder and CEO HD Moore about RunZero’s new release: 4.9. It drops this week and doubles down on OT scanning. Animated world and network maps add another layer to visualisation and for those that have been asking: yes, there’s a dark mode.

Arrests, cybercrime, and threat intel
Scattered Spider member arrested in Finland: The US Department of Justice has filed charges against a member of the Scattered Spider hacking group. Peter Stokes, 19, was arrested earlier this month in Finland attempting to board a flight to Japan. He went online under his hacker name of Bouquet. The US is now seeking his extradition. [The Chicago Tribune] [h/t DataBreaches.net]
Ukraine arrests Roblox hackers: Ukrainian police have arrested three suspects who hacked and resold access to Roblox accounts. The group operated out of the city of Lviv and compromised more than 610,000 accounts. They hid infostealers in Roblox apps that stole account credentials. The accounts were later sold on Russian Telegram channels.
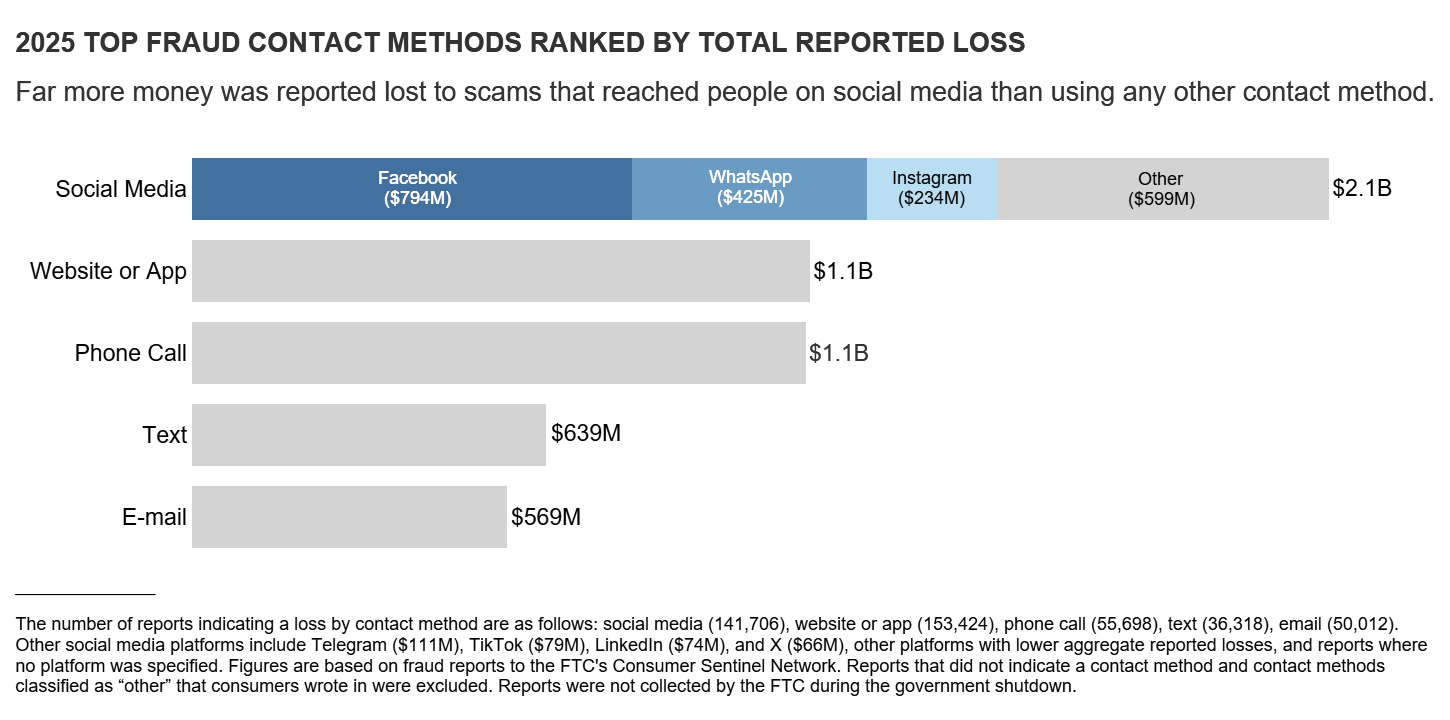
Social media scams hit $2.1b: Americans lost more than $2.1 billion to social media scams last year. Most of the scams started on Meta sites, with Facebook, WhatsApp, and Instagram occupying the Top 3. According to the US Federal Trade Commission, Facebook scam losses were far above those originating from SMS or email.
SonicWall behind a third of ransomware insurance claims: One in three cyber-insurance claims filed last year with insurance provider At-Bay originated from a hacked SonicWall device. Most of the claims were from attacks by the Akira group, which repeatedly targeted the devices. Akira was also the most active group last year, accounting for more than 40% of all ransomware claims. [InsurranceBusinessMag]
Chrome extensions that sell your data: Security researchers have found more than 80 shady Chrome extensions that collect and sell their users' data. This includes a cluster of 24 extensions sold viewing habits from streaming platforms and another cluster of 50 extensions that sold web browsing histories. All extensions were available on the Chrome Web Store and downloaded and installed more than 6.5 million times. [LayerX]
Robinhood abused for phishing: Threat actors are exploiting the Robinhood account creation process to inject malicious content inside new account notifications and use the emails for phishing operations. [BleepingComputer]
VPNs and residential proxy abuse: In a joint research, IPinfo and AbuseIPDB look at the type of malicious activity coming out of 260 million unique IPs, including 94 million residential proxy IPs and 24 million VPN IPs. The conclusion is that more than half (53%) of all known bad IPs are coming from VPNs or residential proxy networks, even if they account for just under 10% of all the IP population.
"The signal here is concentration. When abuse occurs, it’s often associated with infrastructure designed to abstract identity and location."
Malware technical reports
Vect ransomware destroys large files: The Vect ransomware is using a flawed encryption algorithm that permanently destroys any files larger than 128KB. Security firms Check Point and JUMPSEC warn against paying the group's ransom demands. According to recent reports, the Vect group is collaborating with the TeamPCP group to ransom companies from the Trivy and Checkmarx KICS supply chain attacks.
Kyber ransomware: Matt Kirkland looks at Kyber, the ransomware that claims to support quantum-resistant cryptography. It's kinda true, but only for a few of its versions.
M3rx ransomware: Matt also has a report out on a new ransomware group named M3rx. The group launched last week and has already six victims listed on its leak site. Its encryptor is written in Go, so it can technically work on other platforms too.
Rebex-based Telegram RAT: Security researcher dmpdump looks at a new RAT being used to target Vietnamese internet users.
StepDrainer and EtherRAT: LevelBlue looks at two campaigns targeting web3 devs and crypto owners with the StepDrainer crypto-draining phishing kit and the EtherRAT malware.
SLOTTAGENT: The security team of Japanese telco IIJ has published a technical analysis of SLOTTAGENT, a mysterious implant found in the wild.
Saiga 2FA: Barracuda looks at Saiga 2FA, a little known, small-scale but sophisticated phishing kit.
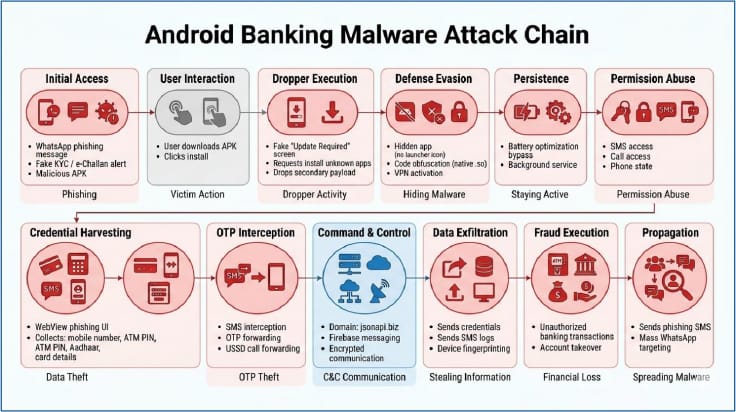
KYCShadow Android banker: A new Android banking trojan named KYCShadow is being distributed in India via WhatsApp spam, posing as a KYC application.
Sponsor section
In this product demo Patrick Gray hosts Ali Cheikh while he shows off how you can use runZero to scan for and manage vulnerabilities in your environment.
APTs, cyber-espionage, and info-ops
Italy approves Hafnium APT member extradition: Italy has approved the extradition of a Chinese hacker to the US. Xu Zewei allegedly hacked and stole information on a COVID vaccines from American companies. The US Justice Department claims he is a member of a Chinese state-sponsored hacking group named Hafnium.
GLITTER CARP and SEQUIN CARP: Chinese state-sponsored hackers have conducted a year-long espionage campaign against journalists, human rights defenders, and exiled ethnic and religious groups. Two separate campaigns have been spotted, carried out by two distinct groups. The first, tracked as Glitter Carp, targeted the foreign Chinese diaspora, its activists, and the journalists reporting on it. The second, tracked as Sequin Carp, specifically targeted journalists who report on China's state repression tactics. Both campaigns heavily impersonated journalists in an attempt to lure users on phishing sites or as part of social engineering attacks. CitizenLab believes the Glitter Carp group is likely a private contractor carrying out state-funded espionage. [CitizenLab // ICIJ]
APT29's EasterBunny implants: S2Grupo and Lab52 have published a joint report [PDF] on EasterBunny, a secretive implant linked to Russia's SVR APT29 group that was used back in 2019.
Info-op promotes US annexation of Alberta: A network of YouTube accounts is using AI-generated content to promote the US annexation of Canada's Alberta region. The inauthentic network produced low quality videos that repeatedly mispronounced names and misidentified politicians' genders, yet still got more than 40 million views combined. CBC News tracked down the accounts to three Dutch nationals. The network started operating after US MAGA politicians met with Alberta's separatist movement last year. [h/t Alex Rudolph]
Storm-1516: Bloomberg has a profile on how Russian disinformation group Storm-1516 operates at such a massive scale that it's actively warping realities across the US and Europe.
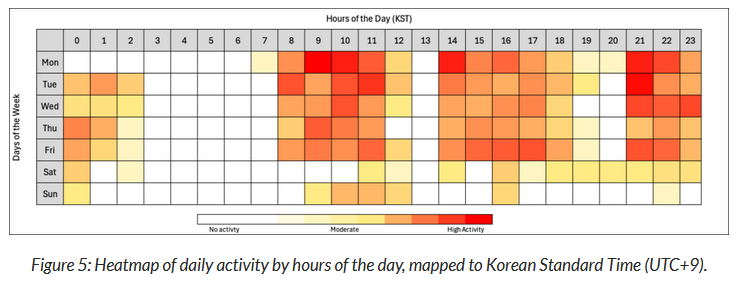
BlueNoroff campaign: Arctic Wolf has spotted a BlueNoroff campaign targeting Web3 devs in North America with fake Zoom meetings. Based on screenshots and videos of past meetings found in a BlueNoroff server, more than 100 devs hopped on meetings. Most of the campaign's activity took place Monday to Friday, between 09:00 and 17:00, Korea time.
Vulnerabilities, security research, and bug bounty
Security updates: Citrix, CrowdStrike, Kubernetes, Tenable.
OpenEMR vulnerabilities: The OpenEMR project has patched 38 vulnerabilities in its open-source electronic health records management platform. Several issues allow a takeover of an unpatched vulnerable platform, and two bugs received a maximum severity score of 10/10. The bugs were discovered by Aisle Security this year. OpenEMR is used by more than 100,000 healthcare providers and manages the data of more than 200 million patients.
Qinglong RCE exploited in the wild: Threat actors are hacking Qinglong task management servers to deploy cryptocurrency miners. Attacks have been taking place since early February. Threat actors exploited an authentication bypass bug (CVE-2026-3965) that was a zero-day at the time but has since been patched. [Snyk]
NSA GRASSMARLIN vuln: The US National Security Agency has released a security update for its GRASSMARLIN security tool. The app was open-sourced a decade ago and allows companies to map out ICS devices in their OT networks. The update fixes a bug found by CISA that allows threat actors to leak information about a GRASSMARLIN-protected network.
GitHub fixes major exploit: GitHub has fixed a major vulnerability that could have allowed threat actors to take over its own servers. The bug could have been exploited using a custom, maliciously crafted "git push" operation. The issue was discovered by Wiz researchers and patched at the start of March. GitHub says it found no evidence that the bug was ever exploited in the wild. Patches have also been rolled out for self-hosted GitHub Enterprise servers.

Infosec industry
Threat/trend reports: At-Bay, Cloudflare, Gartner, Horizon3, ISC2, NASCIO, Nokod, the Open Observatory of Network Interference, OT-ISAC [PDF], ProjectDiscovery, Quokka, S2Grupo and ScanFactory have recently published reports and summaries covering various threats and infosec industry trends.
Acquisition news #1: Identity security platform Silverfort has acquired rival identity security provider Fabrix Security.
Acquisition news #2: DevSecOps platform Socket Security has acquired Secure Annex, a new cybersecurity company specialized in detecting malware in browser and IDE extensions.
New tool—MCPwned: FenriskSecurity has released MCPwned, a Burp Suite extension for auditing MCP servers.
New tool—CI/CD Abuse Detector: The Elastic security team is open-sourcing CI/CD Abuse Detector, a collection of drop-in CI templates that use an LLM to detect suspicious changes to CI/CD pipelines, workflows, and automation configurations.
Risky Business podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq discuss what the North Korean hack of Drift can tell us about the future of hacking.
https://risky.biz/BTN164/

