Risky Bulletin Newsletter
May 01, 2026
Risky Bulletin: The mysterious hack of Moldova's healthcare database
Written by

News Editor
This newsletter is brought to you by runZero, the Total Attack Surface & Exposure Management platform. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.

A mysterious hacking group has stolen the personal and financial information of Moldovan citizens from the country's national healthcare database.
Moldova's national health insurance agency, CNAM, confirmed that data was stolen but denied initial news reports that almost a third of the database had been destroyed in the attack.
Ion Vintilă, an adjunct director for Moldova's Cybersecurity Agency, had told reporters in a taped interview that almost 30% of the agency's data was impacted in the incident, but didn't specify in what manner.
From the wording in the CNAM press release, it appears that 30% might have been stolen or had to be restored from backups.
Vintilă said no ransom request was involved and that they don't exclude Russia's involvement.
Regardless of what happened, the data was extremely sensitive in nature. The database in question stores a vast amount of personal and financial information on every citizen or foreigner who paid for Moldova's national health insurance scheme.
It also contains the financial details of all of Moldova's private medical service providers that work with CNAM and have partnerships to provide certain medical services under the national insurance scheme.
CNAM wrote on Wednesday that payments to providers had gone out as scheduled and that the incident didn't impact medical services in any way.
The theft of such detailed personal information on almost every adult in Moldova comes as Russia has threatened Moldova with military intervention. Russia has had troops and extensive military equipment and ammo depots in the breakaway region of Transnistria since 1992, following its backing of anti-independence forces in Moldova's civil war.
The Moldovan government has repeatedly accused Russia of cyberattacks, disinformation, and election meddling ever since pro-EU parties came into power more than half a decade ago.
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat, Adam, and James at the helm!
Breaches, hacks, and security incidents
China breaches Cuban embassy in US: Chinese hackers have breached Cuba's embassy in Washington to spy on the US' naval blockade. Hackers breached an Microsoft Exchange email server and stole email inboxes for the Cuban diplomats. The same group hit more than 5,000 Exchange servers in a massive hacking campaign this year. [Bloomberg // Gambit Security]
Jerry's Store leak: The Jerry's World carding forum has leaked more than 345,000 stolen credit card numbers due to a misconfigured web server. The leak was traced back to a server configuration that was generated using an AI-based code editor. The AI-generated code left the server and its contents exposed without any kind of authentication. The value of the leaked card details is believed to be between $1 million and $2.6 million. [Cybernews]
Ardmore ransomware attack: The city of Ardmore in Oklahoma has suffered a ransomware attack earlier last month, on the 8th.
Estée Lauder breach settlement: Cosmetics company Estée Lauder will pay out CAD$1.5 million to settle a class-action lawsuit in Canada over a 2023 security breach.
Huge Networks hack: A Brazilian DDoS had a security breach earlier this year and then had its server infrastructure abused to relay attacks towards Brazilian ISPs, the very same customers it was supposed to protect. [KrebsOnSecurity]
Leaky stalkerware server: Security researcher Jeremiah Fowler has found an internet-exposed web server that stored logs from a single victim of spyware, identified only as "a prominent European celebrity, entrepreneur, and media personality." [ExpressVPN]
General tech and privacy
Google tries to take control of browser AI standards: Mozilla is raising hell over the new LLM Prompt API that would effectively mean that all LLMs shipped with any browser anywhere must adhere to Google's terms and conditions. And this is why every web developer under the sun had warned you that a Chrome browser monopoly was bad!
Meta failed to comply in the EU: The EU has accused Meta of failing to comply with the Digital Services Act and allowing children under 13 to register on its platform.
OpenAI Advanced Account Security: OpenAI is rolling out a super-secure mode for ChatGPT accounts. The new Advanced Account Security mode will disable password logins and only allow access using passkeys or physical security keys. The mode also comes with shorter logged-in sessions and a more secure account recovery process. Users who enable this mode for their account will also have their past conversations automatically excluded from the training of new models.
Claude Security: Anthropic has opened Claude Security to a public beta. This is Mythos' smaller brother, a tool for cybersecurity work that's not "too dangerous" to release.
New AI security standards group: Seven organizations involved in AI security standards have united under a new group to reduce industry and standards fragmentation. The new standards group is named MOSAIC, which stands for Multi-Organization Secure AI Coordination. Founding members include some of the most notable standards organizations in the world, such as NIST, OWASP, SANS, and the Cloud Security Alliance.
Cloudflare opens itself up to AI agents: Cloudflare says it will let AI agents create accounts on its platform, buy domains, and deploy code. Agents can also be given budgets, to prevent customers from ending up in world-ending debt when their stupid LLM goes into a loop.
Thundermail to have a beta test: Mozilla will invite users to the first beta run of its upcoming Thundermail webmail service. The beta is expected this month.
Fedora 44: The Fedora v44 release is out.
Meta sweeps problems under the rug: Meta has canceled a major contract with a Kenyan company that reviewed footage from its AI smart glasses. The company claims it was dismissed after workers spoke with journalists from a Swedish news site. The workers revealed that the Meta glasses were often capturing graphic imagery, such as people having sex, undressing, and going to the toilet. [BBC]
Government, politics, and policy
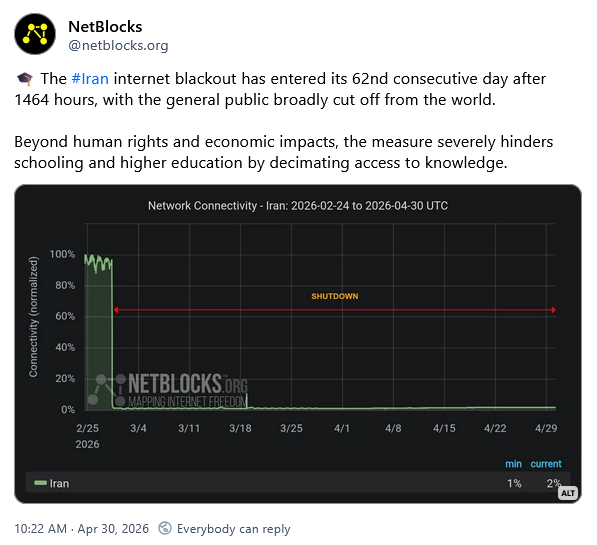
Iran's internet blackout is costing it $80m/day: The Iranian government is losing an estimated $80 million per day due to its country-wide internet blackout. The blackout has been in place since February 28, when Israel and the US began a new wave of military strikes against the Iranian regime. According to Bloomberg, the current blackout is dividing Iran's civilian government and security services. Camps have emerged on both sides asking for the internet shutdown to be lifted. [Bloomberg]
Kenya views scammers as a security risk: The Kenyan government is treating workers repatriated from Asian scam compounds as potential security risks. Officials are afraid former scammers will establish cyber scam compounds of their own when they return home. The government has proposed strengthening its legal framework and running a nationwide awareness campaign about the proper ways of finding overseas employment. [CommsRisk]
Paragon refuses to work with Italian authorities: The Italian government says spyware maker Paragon Solutions is refusing to help its investigation of a major surveillance scandal. The company has yet to respond to a formal request sent through the Israeli government. Paragon cut ties with the Italian government last June, claiming that the Italian government refused its help in investigating alleged abuses of its tools by Italian intelligence services. [WIRED Italy // TechCrunch]
Greece closes Predator case: The Greek Supreme Court prosecutor has closed the country's investigation into the Predator spyware scandal. The official closed the case despite a call from lower criminal courts to continue the investigation. The Greek justice system sentenced four Intellexa managers to more than 126 years in prison for selling the spyware last month. No government officials were even investigated for deploying the spyware against the opposition, journalists, and prosecutors. [Tovima] [h/t Jurre van Bergen]
Canada bans crypto-ATMs: Canada will ban cryptocurrency ATM kiosks due to an increase in scams. Officials say crypto ATMs have now become the "primary method for scammers to defraud victims" across the country. Canada has the most crypto ATMs per capita in the world, with more than 4,000 installed kiosks. [CBC]
Germany tells MPs to switch to Wire: The German Parliament has told MPs to switch from Signal to Wire for secure communications. Officials said the app is more secure than Signal because it's not associated with public phone numbers. Bundestag President Julia Klöckner fell victim to a Signal phishing attack earlier this year. The incident was blamed on Russian hackers. [Heise]
Pentagon cyber apprenticeship program: The US Department of War has a cyber apprenticeship program to help recruit and onboard more cybersecurity professionals. The 12-month program will start this summer in a small pilot program. The program will not have degree requirements after the OPM removed the criteria across the entire US government earlier this year. [NextGov]
Another FISA extension: Congress has passed another temporary extension to the FISA Section 702 surveillance clause. FISA surveillance powers were extended for another 45 days until June 15. They were set to expire on Thursday. The US House of Representatives passed a three-year FISA extension this week but the Senate couldn't agree on a longer deal. [NPR // The Hill]
White House opposes Mythos expansion: The White House is opposed to Anthropic expanding access to its private Mythos cybersecurity model to 70 new companies. The new additions would have brought the total number to more than 120, more than double the number of organizations that already have access. US officials told Anthropic they oppose the move because of national-security risks. They also oppose the move because it would put a strain on the company's computing resources, which could hamper the government's own Mythos access. [Wall Street Journal]
Sponsor section
In this Risky Business sponsor interview, Casey Ellis chats to RunZero’s founder and CEO HD Moore about RunZero’s new release: 4.9. It drops this week and doubles down on OT scanning. Animated world and network maps add another layer to visualisation and for those that have been asking: yes, there’s a dark mode.

Arrests, cybercrime, and threat intel
15yo arrested for ANTS hack: French authorities have arrested a 15-year-old for the hack of the ANTS government database. The teen is accused of taking the data and selling it on hacking forums last month. ANTS is the French government's agency that manages identity documents, driving licenses, and vehicle registrations. The teen faces up to 7 years in jail and a fine up to €300,000. [Paris Prosecutor's Office, PDF]
Russian game hacker sentenced: Russian authorities have confiscated the laptop and prohibited a 19-year-old from Veliky Novgorod from leaving the city for hacking and stealing the GTA 5 Online and Roblox accounts of other children. [Mash]
Europol dismantles Tirana scam centers: Albanian authorities have raided three call centers in the capital of Tirana that ran cryptocurrency investment scams. Ten suspects were also arrested during the operation last month. The call centers had allegedly operated on an industrial scale since at least 2023. Scammers were organized in different teams based on the language they spoke. Most of the scams targeted users in Canada and Western Europe, such as Germany, Austria, Italy, and Spain. Financial damages have been estimated at over €50 million.

Dubai scam centers raided: Nine cyber scam compounds have been raided in Dubai in a joint operation by Chinese, US, and UAE authorities. Two-hundred seventy-six suspects were arrested following raids this week. Four of the compound's managers have been detained in the UAE and Thailand, while two are still at large. This is the first-ever crackdown against scam compounds in the UAE. Meta warned last year that scam compounds had expanded from Southeast Asia to the Middle East, with Dubai being a preferred destination.
Cambodia deports 600+ Thai scammers: Cambodian authorities have deported 635 Thai nationals for being involved in online scams. The individuals crossed the border illegally to work in cyber scam compounds established in Cambodia. Cambodia is in the midst of a major nationwide crackdown on cyber scam operations following international pressure from China and the US. [FreshNews] [h/t CyberScamMonitor]
Black Axe members detained in Switzerland: Swiss authorities have arrested 10 members of the Black Axe Nigerian criminal syndicate. The suspects were involved in romance scams and other cyber fraud operations. Europol says one of the detained suspects is believed to be the group's regional leader for Southern European operations.
Swatter sentenced to four years: A Romanian national was sentenced to four years in federal prison for swatting more than 75 US public officials. Thomasz Szabo's victims included a former US president, members of Congress, state governors, and US law enforcement agencies. Szabo and a Serbian national were identified and arrested in 2024 after using Google Voice to place the swatting calls.
Europol decries inadequate data retention policies: Europol says that inadequate or restrictive data retention policies at online companies are hampering its efforts to investigate criminal activity. The agency says companies don't store logs for long-term access, which is creating investigative blind spots. Officials are asking the EU and other countries to pass stronger data retention and lawful access policies to counter this problem, as well as the rise of new technologies like AI.
Hackers are aiding cargo thefts: The FBI says that hackers are aiding criminal groups to steal real-world cargo loads. The campaigns include compromises of cargo brokers and cargo transport companies in order to control accounts that manage cargo loading and movement processes. The access is exploited to redirect legitimate cargo hauls to complicit drivers.

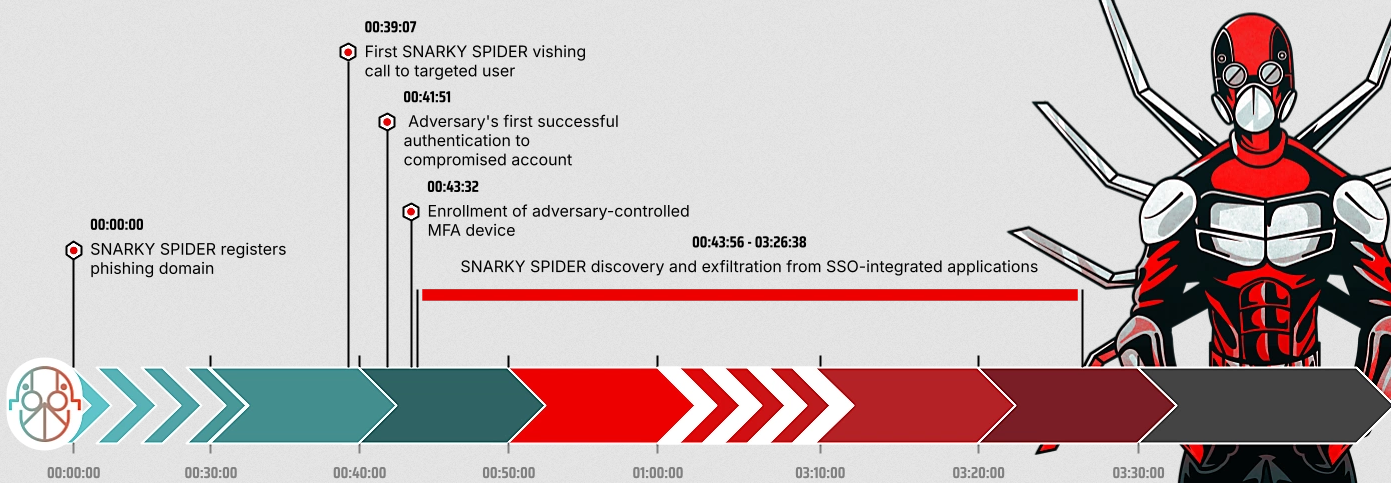
Cordial Spider and Snarky Spider: CrowdStrike says it's tracking two new groups named Cordial Spider and Snarky Spider that are mimicking the tactics of their predecessors, Lapsus$ and Scattered Spider. Both target large companies by posing as IT support to contact employees and trick them into running malware or accessing phishing sites. The groups have been very active since October.
xlabs_v1 walks around naked: Hunt Intelligence has found an open directory containing the guts of the xlabs_v1 DDoS-for-hire service and its attached Mirai-based botnet.
WP plugin backdoor lay dormant for years: The Quick Page/Post Redirect WordPress plugin contained a secret backdoor in all versions released since March 2021. [Anchor Host]
Komari abuse: Add the Komari remote management toolkit to the list of RMM tools abused in the wild by threat actors. [Huntress]
Operation Road Trap: Bitdefender has analyzed a sprawling smishing campaign targeting 12 countries with SMS spam impersonating transport authorities, toll operators, and parking services.


Malware technical reports
Mini Shai-Hulud: A new self-spreading worm is targeting the npm JavaScript ecosystem. Named Mini Shai-Hulud, the malware spreads via SAP-themed npm packages. Once it infects a victim, it downloads the Bun JavaScript runtime to execute an infostealer and steal credentials and tokens. The malware also contains logic to copy itself inside an infected developer's accounts and packages. Researchers believe the malware might be the work of the same TeamPCP group that has been hounding code developers across multiple supply chain attacks this year. [Aikido Security // OpenSourceMalware // SafeDep // Snyk // Socket Security // Step Security]
GachiLoader: Malwarebytes looks at a malware delivery campaign using AI lures and dropping the new GachiLoader, which, in turn, was dropping the Rhadamanthys infostealer as the final payload.
Phoenix System PhaaS: Group-IB looks at Phoenix System, a Phishing-as-a-Service platform that has been operating since January of 2025. The service operates more than 2,500 phishing domains designed to target over 70 companies. Researchers believe the service was also used in conjunction with SMS blaster operations.
Bluekit PhaaS: Acronis researchers have uncovered a new AI-powered phishing kit named Bluekit, complete with "40+ website templates, automated domain purchase and registration, 2FA support, spoofing, geolocation emulation, Telegram and browser notifications, antibot cloaking, and add-ons like an AI assistant, voice cloning, and a mail sender."
ValleyRAT: The security team at Japan's ITOCHU corporation looks at all the malspam campaigns targeting Japan that delivered the ValleyRAT this year. Apparently, it's been a lot.
SilverFox's new ABCDoor backdoor: SilverFox, an e-crime group that usually targets Chinese-speaking users, has recently begun targeting Indian and Russian organizations with malspam campaigns delivering the new ABCDoor backdoor.
The Gentlemen ransomware decrypter: Canadian security firm Bedrock Safeguard has released a decryption utility that can recover files encrypted by The Gentlemen ransomware. The decrypter can be used if companies can recover at least one memory dump taken while the ransomware encryption process was active. Bedrock says the ransomware stores all its encryption keys used at various stages of the encryption process in memory.
Sponsor section
In this product demo Patrick Gray hosts Ali Cheikh while he shows off how you can use runZero to scan for and manage vulnerabilities in your environment.
APTs, cyber-espionage, and info-ops
APT seeks GIS data: A cyberespionage group is trying to steal GIS files and geolocation data from Russian state structures and its aviation industry. A campaign that began last September has sought to exfiltrate sensitive GIS files. The format is used in CAD engineering to store geographic-related data, such as terrain, roads, and construction information. Kaspersky attributed the hacking campaign to an APT it tracks as HeartlessSoul. Some of the group's infrastructure overlaps with the older GOFFEE group.
Vulnerabilities, security research, and bug bounty
Security updates: Chrome, cPanel, Jenkins, Kubernetes, NVIDIA, Ollama, ProFTPD, SonicWall, Xen.
Practice by Numbers patches bug: Dental software maker Practice by Numbers has fixed an IDOR bug that allowed anyone with an account on the platform to view everyone else's files just by fiddling with URL parameters… like it's 2010 all over again. [TechCrunch]
Major cPanel bug exploited in the wild: The cPanel project has released a security update to patch a major vulnerability in its web hosting management software. Tracked as CVE-2026-41940, the bug allows attackers to bypass authentication and access a web hosting customer's cPanel account. If the patch can't be applied, blocking access to the cPanel backend is advised by blocking TCP ports 2083 and 2087. In the wild exploitation has been reported weeks before and confirmed by CISA within a day after disclosure.
RCE on AI infrastructure servers: Cato Networks has found vulnerabilities in NVIDIA NeMo and Meta PyTorch that can allow attackers to take over AI servers by tricking victims into running malicious AI models.
Xen API "Shittrix" vulnerabilities: The Xen project has released security updates for the Xen open-source virtualization software. The fixes patch some of the 89 bugs disclosed last week by Jakob Wolffhechel without any prior notice. The bugs are in the XAPI management interface and affect every Xen version released over the past two decades (2006). They also impact the Citrix XenServer hypervisor.
SonicWall advises "immediate firmware updates": SonicWall has released firmware updates for its firewall devices. The update patches three bugs discovered by security firm CrowdStrike. SonicWall has told customers to immediately apply the patches or disable access to the device's web management interface. Device management should be carried out via SSH only. The company didn't specify if the three bugs were under active exploitation.
Major ProFTPD bug: ZeroPath discovered an SQL injection in ProFTPD's mod_sql extension (CVE-2026-42167) that can allow remote code execution, authentication bypass, and privilege escalation depending on configuration.
Copy Fail vulnerability impacts Linux distros going back to 2017: All Linux distros released since 2017 are vulnerable to a new privilege escalation vulnerability named Copy Fail (CVE-2026-31431). Exploitation relies on running a small script of only 732 bytes to get root access. Copy Fail is considered one of the most straightforward ways to gain root access on Linux systems since it's not as error prone as previous bugs like Dirty COW and Dirty Pipe. The vulnerability was discovered by South Korean security firm Theori using AI tools. [Decipher]
Infosec industry
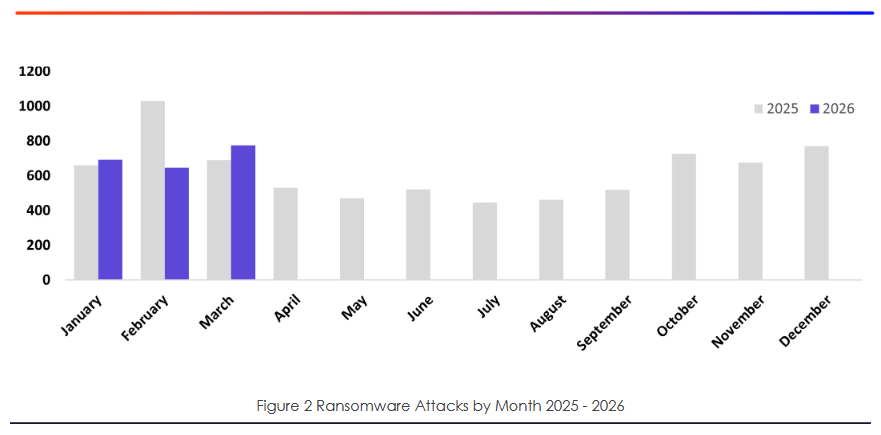
Threat/trend reports: Cloudflare, Coveware, eCrime.ch, Europol, Incogni, KELA, Microsoft, NCC Group, Rostelecom, RunSafe Security, and Thales have recently published reports and summaries covering various threats and infosec industry trends.
Zero Trust in OT: Five US federal agencies have released joint guidance on implementing Zero Trust principles in OT networks to help secure the country's critical infrastructure.
New tool—CopyFail-Detect: Security researcher Kadir Can has published CopyFail-Detect, a detection toolkit for the Copy Fail Linux vulnerability (CVE-2026-31431).
New tool—Model Provenance Kit: Cisco has open-sourced the Model Provenance Kit, a Python toolkit and CLI for detecting model provenance.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about the US government stepping in to fight 'distillation attacks' by Chinese AI labs. These are methods used to steal the special sauce of frontier AI models simply by asking questions.

In this episode of Risky Business Features, Anthropic’s Nicholas Carlini joins Patrick Gray and James Wilson to talk about advancements in AI-driven vulnerability research and exploit development.


